Protect Your Identity on Internet - 1

Your online identity consists of a number of unique details that ideally only you should know. Which some people might think that your name, address, credit card information and account number are the only bits of sensitive information that require protection, there are many other details that can be used to steal your identity. Your IP address, usernames and password, PIN numbers, account numbers, and even your secret questions for passwords can all be used in combination or individually for identity fraud.
A computer user working offline need not worry much about identity theft as long as his PC is protected with a decent login and password and he does not leave it unattended. Once you go online , however, you are vulnerable to various methods of attack. The biggest advantage for ID thieves online is that they do not have to physically steal your information or even steal information at all. More often than not, users unknowingly hand over their details through malicious spam email, messages and websites.
What Is the Threat ?
Any official or financial activity, transaction or documentation requires a person to furnish identity proof. Whether you are purchasing a new SIM card for your phone, purchasing something with a credit card, booking a flight or applying for a loan, none of these activities can be completed without ID proof, so it is obvious that you need to maintain the secrecy and legitimacy of your identity.
Should your personal details fall in the wrong hands, they can be used to open bank accounts, apply for loans, create email IDs and accounts on social media sites, or even purchase expensive items using bills, thereby ruining your credit history and even affecting your reputation.
The hardest part about identity theft is that you will not be aware of it until you have noticed discrepancies in your bills or have been contracted about controversial or unacceptable material being posted by someone using your identity. Often, an intelligent attacker will know how to regulate these details to avoid detection.
How It's Done
Your personal and confidential details can be stored in many ways and sometimes not even directly from you, but rather from a service provider that has not taken sufficient security safeguards to protect its customers.
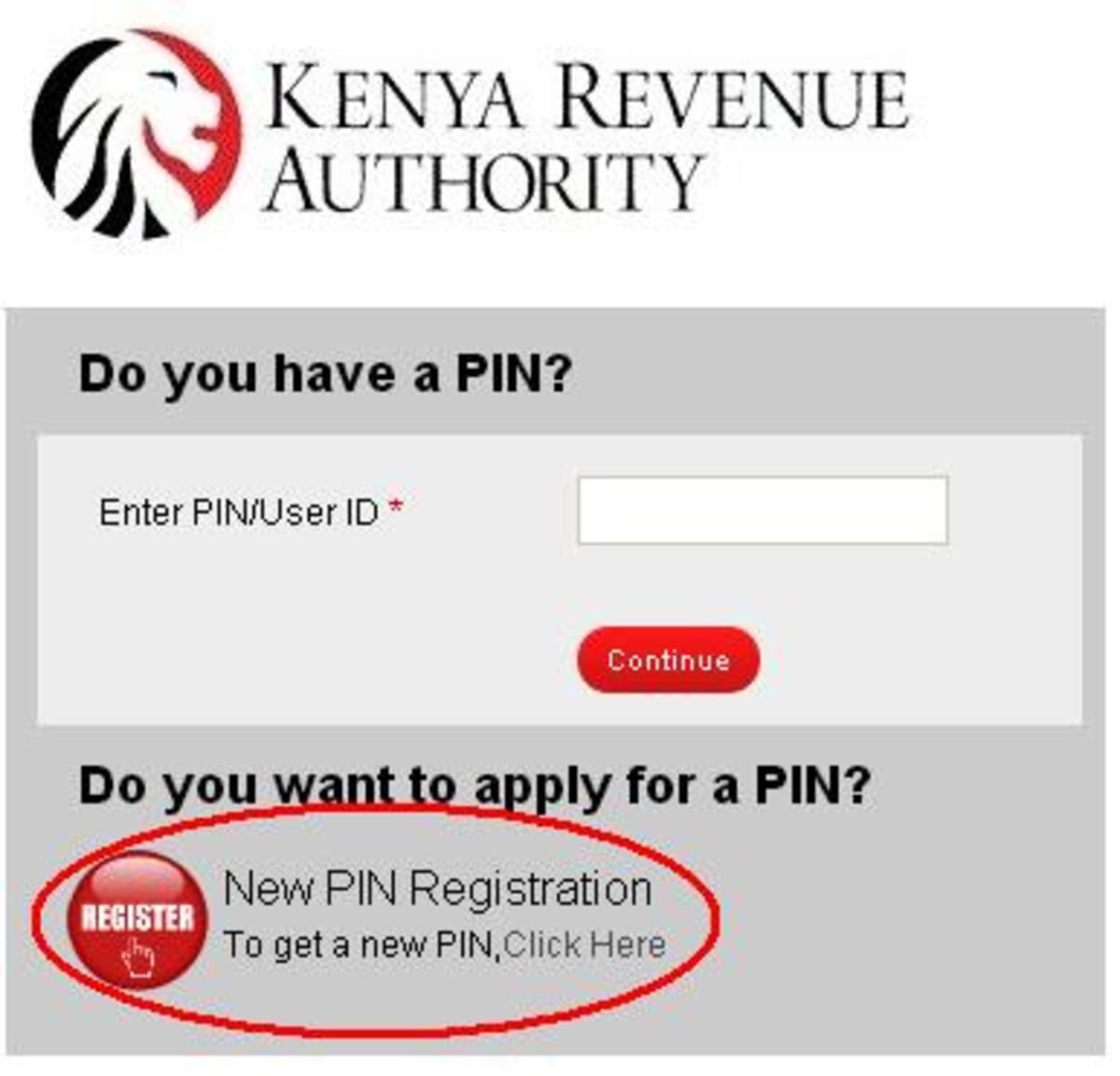
The simplest way for a fraudster to gather information from an unsuspecting user is to fool them into submitting the details themselves. Phishing mails are sent out to multiple email addresses requesting bank account information, passwords, PINs or credit card details under the cover of a legitimate-looking website. This is a hit-or-miss process, where only a fraction of the recipients to steal a considerable number of identities, which they can them use or distribute.
Trojans are also a very common cause of identity theft. Trojans are viruses that infect your system and then dispatch information saved on your PC such as login IDs and password or track keystrokes with which hackers can determine other personal details. Key-logging is a legitimate feature that many applications incorporate for functions such as parental control, hot keys and corporate security. Illegal key-logging software, however, can be designed to detect certain keystrokes when accessing specific sites such as your email, social media profiles or secure banking sites, thereby recording your user ID and passwords.
Password strength is something that all sites stress upon, and for good reason. Cracking a long password containing different cases, characters and symbols takes a lot longer than a password is a common word or phrase. Another point often stressed on is to have different passwords for different sites, so that a hacker cannot access all your accounts if he cracks the password any one of them.
Users that do not heed these warnings often end up losing data and information from multiple profiles as hackers glean through their accounts and gather information. For example, skimming through an average user's e-mail, Facebook,Twitter and online bank accounts can provide a hacker with all required personal information, credit card and financial details to apply for a new credit card or bank loan.
Another source of credit card information that hackers often target are payment has gateways. Online shopping and bill payment has gained popularity in India over the last few years and now several services such as cell phone network providers, Internet services, e-shopping sites,etc are beginning to often online bill payment directly through their sites.
While most of these businesses are reliable and provide sufficient information to prove that your credit card information will be safe, some sites could have loopholes in their security measures or might fail to create a secure connection, in which cases, attackers can easily access your credit card information and use it to make purchase online in your name.
A more recent form of identity theft, and one of major concern, is through social networking and social media sites. the danger with these services is that they are popular among youngsters, who are unaware of what type of information must not be shared online and how this information and use it to make purchases online in your name.
Users with Facebook, Twitter, Youtube, Flickr or any other such social media accounts often have weak privacy or security settings and also sometimes divulge too much information. Even something as simple as a status update or a video mentioning the names of your family members, pets or friends, birthdays can be used to hack accounts and create duplicates or elicit data.
Identity fraud beginning with information collected from social media sites is often opportunistic where the attacker happens upon an accounts which lets strangers view all the information shared.
Part - 2 of this Thread
- PROTECT YOUR IDENTITY ON INTERNET - 2