Privacy Hacks: Secure Your Privacy in a Surveillance State

The Idea of Privacy is an Illusion.
Let me scare you for a minute. Now I don't profess to be a hacker or even a computer expert by any means but I have been a human rights and freedoms advocate for over 20 years and maintain serious concerns about privacy, security, freedom and surveillance. No one likes to be spied on, monitored or watched in any regard, be it by a snoopy neighbour, a hacker, the government or tracked on the Internet.
WATCH DOG: BIG BROTHER
But you are. Do you not think we are living in a surveillance state not only in the United States but here in Canada, too? Ever notice that there are now cameras on practically every city intersection, in every retail store, on the transit buses, in taxi cabs, on police vehicles, on your neighbor's house and there is certainly a camera staring straight at you, your webcam on your computer. I have a piece of tape covering mine whenever it is not in use...just in case.
In fact, a few years ago there was a new expensive facility added to Canada's protection services for C.S.E.C., the Canadian Security Establishment Commission. It is quietly located near the city of Fredericton, in the province of New Brunswick which the people in town call "The Potato Farm", because it is labelled as a farm but is actually a multi-million dollar high technology facility operating artificial intelligence surveillance. The military come and go from the area in uniform, day and night and the Canadian Forces Base Oromocto, is nearby. All, for the sake of protection against terrorism of any kind whether it be real or cyber and perhaps it seems, even against citizens of Canada.
Just a note: This article does not constitute revealing classified information and 'does not' convene any limitations on Freedom of Expression as outlined in Canada's Charter of Human Rights and Freedoms. I did not list any specific address, albeit the people of the area are well aware of its existence.
In fact, many persons within the justice community in Canada are well aware where collected evidence on the public is derived, especially on high profile cases which would be intelligence from CSEC or CSIS or supplied to police agencies or requested by them. In court documents, identity or 'informant' or evidence source supplied to the police and/or the Crown Attorneys are blacked out and gag orders are put upon the court observers and media.
This includes paid short term or long term informants providing evidence on citizens. Informants who are recruited via different methods by authorities, including Crime Stoppers in Canada, the identities are blacked out in all court documents and gag orders apply.
In short, an accused, or the defendant in a case is not aware where "confidential evidence" is supplied from, whether it be obtained by an informant (person) or by surveillance and is deemed protected evidence even the defendant's attorney is not privy. Obviously, it does seem to contravene the Charter Rights in Canada, as protected person's identities who truly are supposed to be kept secret include: they are a child or minor or a victim of a crime related to the case. Big Brother, big's agencies and/or let us call it "the informant" is protected with anonymity.
The Canadian Communications Security Establishment Commission
- Communications Security Establishment
Canada's Digital Cyber Watchdog. Our version of the United States' National Security Agency (NSA).

Surveillance on the Streets...

Artificial Intelligence: National Cyber Surveillance in the Name of Safety
Proof: We are all under Surveillance...
A reputable attorney colleague of mine confided, in one of our conversations, that during the 2011 Vancouver Stanley Cup riots where there was extensive property damage and fires, there were over 3,500 photos of individuals identified by artificial intelligence facial recognition programs for criminal activity on the streets. Out of this 3,500 photos, 1,500 resulted in actual court criminal convictions. The street surveillance photos were "enough" evidence to prosecute and convict a person of a crime in Canada.
I suppose this is why civilians are afraid to protest for social justice and civil liberties against the system. Why they are afraid to post truthful commentary even on my controversial publications. I have risked a great deal to investigate these serious issues and dare to publish it online because no one else will. I will exercise my right to free speech.
Can I Smash My Computer with a Hammer Now?
Think about this. Once upon a time, I thought to really educate myself about computer and Internet security, privacy and protection. So after extensive reading, I made significant changes to my security settings, permissions, installed and changed software and so forth. I was rather thorough and it was about two days of tweaking and changing my habits to make my experience as anonymous and secure as possible.
I woke up one morning soon after this adventure. For some reason, I couldn't sleep, it was very early, about 4 a.m. I happened to walk by my computer to go the kitchen to make coffee and noticed it was not in sleep mode, was lit up and operating. The only program I have set to automatically update is my custom anti-virus software on a specific day and time each week. It was not this day and there was nothing scheduled.
The computer was installing updates and flashed a processing message on a blue screen which took about 30 minutes to complete, then it restarted. I use Windows 10. I logged in to my local non-networked administrator account to investigate. To my alarm, I discovered all my security and privacy settings were restored and changed back to their insecure states.
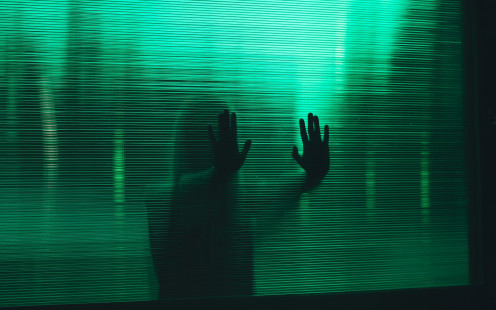
IS THERE A GHOST IN MY COMPUTER?
Further more, my preferences and application changes were changed back to Microsoft with automatic notifications and feedback to Microsoft turned on and locked on. I could not turn them off and when I tried to reset to my custom privacy and security preferences, these options were no longer available. My files were still in tact and my new software was still installed with icons on the desktop, but some aspects of the operating system and appearance were different. Upon further snooping, I discovered the computer had independently installed a new build. But...how and why?
I had relocated to a new town that weekend in the province and...had not had time to arrange any cable or Internet services from any provider yet. My computer was NOT connected to the Internet in anyway, neither by ethernet, wifi nor mobile device. I thought I was having a delusion, a bad dream and asked myself if I was in some strange alternate reality.
I checked all the cables to the computer to ensure I wasn't seeing things or missing something, there was only one- the power cord. I didn't even have a modem. I checked my network settings and browsers, there was absolutely no connection to the Internet. There were no wifi connections open in the area either and it was in offline mode. I checked my cell phone on the desk that was charging. Although there was data turned on my phone, there were no devices connected to the data, nor wifi or any mobile hot spot or tethering activated. Can you say crazy?
The night you intend to spend an hour, only to realize many hours have passed by. What?

Embedded Software, Monitors and Reporting Built into Your Operating Systems
I tried to be rational about it. Since there was no Internet connection, which is what is usually required to download and install updates, my computer must have downloaded the new build sometime before, at least, a week ago or earlier. It downloaded it in the background somewhere unbeknownst to me. It would also have had to schedule the install for a later date. Nonetheless, it did so all without my knowledge or consent and cost me hours.
SO I PUT AWAY THE VOODOO BEADS AND DEAD CHICKEN...
The exorcism had to wait for another day. Ha, ha! But regardless, I was much more alert to the fact that I was not in control of my own computer, security and privacy. How coincidental, however, that only a few days after I attempted to take control of those issues, that Microsoft conveniently installed this new build and reset all my settings and controls, even blocking some from being turned off. Does Windows 10, which is reportedly notorious for sending observed and habit tracking data back to bug central, alert Microsoft when data reports are blocked from certain computers?
I am not so vain to think that Microsoft gives two bits about the habits of a writer and political activist in Canada. BUT I am aware that more and more trends of people in the world who use the Internet are educating themselves on how better to protect their anonymity and privacy while using the Internet. You don't have to be a user who wishes to hide something, be it a business trade secret, a substantial purchase, a financial plan, online banking, whistle blowing data or even kinky erotica. It is your human right and freedom to information privacy and security, even in an online world. Albeit, it seems few people respect those rights such as snoopers and spies like hackers, thieves, jealous lovers, corporate trackers or even certain government departments.
Windows OS always attempts to restore to factory installed applications upon Windows Update.
Customizing your Experience is a Nightmare.
SAMPLE PROBLEM:
Attempting to remove embedded built in sponsored software which comes auto installed with your Windows OS, is only reinstalled all or in part upon your next Windows Update. Trace files are embedded in the operating system. It is all software promotion, advertising and sponsorship.
You think you are receiving all this free software with your OS but in reality, you are being given the manufacturer's sponsored software built into the OS to eliminate freedom of choice and prevent you from downloading from the competition, who may have better options for you.
Changing your privacy, monitoring and reporting settings can also be undone and reset by updating. Therefore, if you installed programs you truly prefer, instead of using the sponsored built in software, can present you with serious errors and operating conflicts whenever Windows Update runs on your computer. And, all your downloading, purchases and customization, often hours of work, is gone to waste.
For instance, Norton Utilities comes installed with Windows OS, but it is a memory hog on RAM, significantly slowing down your computer and controls many aspects of your programming. It is almost impossible to uninstall when expired and this ensures you purchase it again because the first trial was built in free.
So if you prefer Freeware, Shareware, or choose to purchase a custom Antivirus Program Suite, you may run into serious conflict issues. Even entering the program's folder on your hard disk and manually attempting to remove trace files of built in programming by each file, the OS will block removal to the recycle bin.
BEST TROUBLESHOOT EVER:
I feel for you, because none of these issues are mentioned in the operating manual with any operating system. To save time, money, headaches, and nights wanting to smash your computer with a hammer, do your research on different operating systems and builds online before your purchase. There are many video tutorials on the web for you to review.
Click and play built in systems seem great for beginners, but intermediate and advanced users become very frustrated when they realize there are so many better software options out there, many of them free.Then you are a downloading freak and much of it conflicts with the built in software, so you just want to pull your hair out. How bad do you want freedom of choice?
Although some other Computer Operating Systems are more expensive or there is the process of learning a brand new operating system, please realize that most viruses, worms, spyware and malware malicious hackers and identity thieves create are made especially for Windows OS.
So using alternative operating system computers have the benefit of less infections and identity thefts over the internet because hacker programming is not compatible. Is protecting your financials, trade secrets, copyrighted material, photos, online banking, business, credit, identity information, passwords or even your music and erotica collections with the option to totally customize your computer with your choices in best software, worth investing in and learning a different system?
A different choice means you are in control of your freedom, security and protection, not the manufacturer. Hacker terrorists and their annoying infections and thefts which cost billions each year prey upon beginners, the naive and the novice costing vast money and resources in investigations and security trouble shooting by I.T professionals, police, banks, government agencies and resource protectionists, let alone you, the lone consumer with a computer at work or home.
I recommend the following generic software necessities to protect your privacy and ensure better security. There are plenty of Freeware and Shareware sites.
Antivirus & AntiMalware
| Freeware or Small Fee
| Total Protection for Computer and Web Browsing
|
A Registry Cleaner Defrag
| Freeware
| Cleans Disk, Registry and Optimizes
|
A Driver Update Program
| Freeware
| Updates all your software driver programs
|
A Decent VPN Service
| Monthly or Annual Fee
| Creates a Tunnel, Hides your I.P. location
|
Remember to regularly schedule Boot Time Scans to deep scan your computer for infections, malware, spyware and junk BEFORE windows loads up and starts. Boot Scans are the only way to get rid of some of the worms and viruses that infect.
Why VPNs are the best way to protect your identity, privacy and security.
But what I got is cheap and works for what I need to do. Okay, then this is for you...
If you choose to stick with what you got, and wish to browse and read sensitive content in anonymity, or if you like interesting downloading using a Torrent Client, you can use your VPN in tandem with the TOR Onion Browser which also accesses the Dark and Deep Web through it's platform and Duck Duck Go Search Engine.
TOR can also be added as an Add On Extension in your Firefox browser but you must install a Native program first available for download on various sites. If you are adventurous, before you dive into the dark and deep side, please review my article, Mystery Revealed: What is the Dark Web? The link is provided below.

If you dare to venture deeper into the web...read my following article before you jump in.
- Mystery Revealed: What is the Dark Web?
Did you know there is a mysterious hidden internet called the Dark Web and Deep Web? With greater surveillance from governments, ISPs and hackers, what you should know about the 'hidden' Internet...
Rate Yourself on the Cyber Scale...
Where you at?
Learn More...
This article is accurate and true to the best of the author’s knowledge. Content is for informational or entertainment purposes only and does not substitute for personal counsel or professional advice in business, financial, legal, or technical matters.
© 2019 Claudine Chaboyer