Protect Yourself From Cybercrime by Knowing These Common E-Mail Scams

Cybercrime Is As Old As the Internet
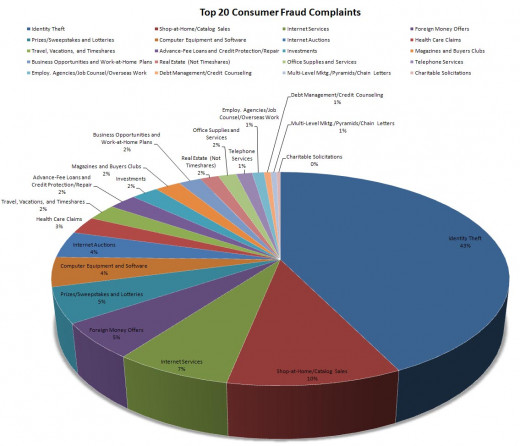
Ever since the introduction of the internet into mainstream life, there has also been people on the internet trying to scam other users. Even before the advent of Facebook, Twitter, and other social networking sites, there was a massive problem with the spread of e-mail scams, hoaxes, and other types of internet spam.
Cybercrime remains a lucrative business for spammers looking to steal people’s money and sensitive personal information, due to the fact that these con artists continue to reinvent new ways to scam internet users. Fortunately, there are things you can do to protect yourself from identity theft and use the internet without fear. In this situation, the more you know the better and arming yourself with knowledge is the best way to avoid falling prey to one of these common internet scams.
Some Useful Terms:
- Spyware – Unwanted software that infiltrates a computing device. Spyware can steal your internet usage data and sensitive information like passwords and bank information to relay to advertisers, data firms, or con artists.
- Malware – malicious software designed to gain access to or to damage your computer, usually without your knowledge (spyware is a type of malware).
- Cybercrime – A crime involving a computer and a network. Often used to refer to myriad internet security scams or cybersex trafficking.
- Phishing – The fraudulent practice of sending e-mails purported to be from a reputable company in order to lure individuals into revealing personal information.
Common Scams and How to Spot Them
- The Foreign Lottery Scam: One of the most common types of e-mail scams involves the receipt of what looks like an official document from a foreign lottery. In the subject line, there is a characteristic congratulatory announcement which often includes the amount of money the recipient has “won.”
- How to spot the fake:If the sender is an individual (rather than an official lottery e-mail address), then it is almost certain that you are being scammed. Use common sense. For example, laurajones123@hotmail.com is probably not the person who is going to deliver the news of your lottery winnings. If your name is not in the “To” field, the e-mail might be a phishing e-mail sent to many people in hopes that someone will fall for the trick. Another indication of phishing is if the scam e-mail requests sensitive personal information. Once you respond with this information, you are liable to have your identity or savings stolen.
- Survey Scam: This scam is innocent at first, and you might not even realize that anything is wrong until you suddenly notice unfamiliar charges on your credit card bill. If you receive an e-mail requesting your input for a survey, be wary of clicking the link unless you specifically requested to be on the mailing list. It could cause malware to be installed on your computer, which allows cybercriminals to collect your sensitive information.
- How to spot the fake: If you are sent a survey requesting your input, ask yourself, do I recognize the name of this organization, and/or did I sign up for this survey’s mailing list? If the answer is no, go ahead and mark the e-mail as spam and move on. Scammers will often use social issues, political issues, or other tragedies to appeal to people’s emotions, making them seem harmless or more trustworthy, making you more likely to click.
- PayPal or Online Credit Card Scam: In this scam, you will receive an e-mail that looks like it is from PayPal, with a warning message like “Act now, or your account will be deactivated,” which might cause you to panic, click the link, and log in to your account. This leaves you at risk of having your personal information stolen because the website is not actually PayPal’s website, but rather a false website designed to look exactly identical to the real thing.
- How to spot the fake: Like in the first example, check to see if the sender’s e-mail is suspicious. The name might sound official like “PayPal Security Center,” but strange and suspicious-looking e-mails are a dead giveaway that you are dealing with a scam. PayPal sends its e-mails from an address that ends in “@paypal.com,” not “@pay-pal./security.uk.org.” Another hint is to look for correspondence that beings with “Dear Valued Customer,” or any other such generic response. A legitimate company that you choose to do business with will definitely know your name and use it when they are trying to contact you.
- Finally, no legitimate company will threaten to close your account if you simply ignore an e-mail. They have other means to contact you, and they want your business. If the e-mail threatens you to take action immediately or your account will be deleted, you are likely being scammed.
A Few More Examples:
- The Mystery shopper: There are several variations, but all are designed to steal your money or personal information. The e-mail sucks you in with a subject line promising a large income by working as a secret shopper, no experience or education required. It sounds too good to be true until the company asks you to pay upfront to get your “training materials.” Once you send the money, the package never arrives. Another version involves receiving a fraudulent check as your first payment. You are then requested to send some of the money back to cover the training expenses. You cash the check and wire the money, only to discover that the check has bounced, and you are now responsible for thousands of dollars in related fees.
- The Nigerian Prince: This infamous scam is characterized by an e-mail from someone with a royal or official sounding name or title like “Dr. Bakare Tunde, Astronautics Project Manager.” The e-mail will ask you to help recover a large sum of money from an overseas bank. In return, you will receive a large cash reward. Unfortunately, your eagerness to help in what seems like a win-win situation gets you into trouble, because the next step is that you must provide your bank account information, so that the money can be transferred. After you pay a few hundred dollars in transfer fees, you receive another e-mail stating that something is wrong, and you must send more cash. This continues until you eventually realize that something is not quite right.
Are you at risk of being scammed? Former con artist and bestselling author of Catch Me If You Can Frank Abagnale shows you how to stop scammers in their tracks.
Avoid Common Online Scams by Following These Simple Guidelines
- Delete all unsolicited emails – The best way to avoid email scams is to delete all unsolicited emails. Notice that legitimate companies never send sensitive, personal information via an unsolicited e-mail.
- Don’t believe it when you are promised money or prizes – You should dismiss all emails or links that promise anything “too good to be true,” including free money or lavish prizes, as these are nearly always scams.
- Be skeptical of donation requests – Scammers might use a recent national disaster or some other event to scare or guilt people into making bogus donations. Never donate to an unknown charity that you have never heard of.
- Don’t disclose personal information – Again, a legitimate company will never ask for sensitive information through e-mail. This includes your bank account or social security number. No matter what they promise, it is never safe to disclose personal information via e-mail.
- Think before you click – If you receive an unsolicited e-mail inviting you to “click here,” you should beware even if the company seems legitimate. These e-mails can take you to a third-party website designed to steal your information.
Have you ever been a victim of fraud or identity theft?
In Conclusion
If you or someone you know has fallen for an online scam remember you are not alone, and that con artists have grown increasingly clever with new technology to steal your information. The good news is, protecting your identity and money from online scams is pretty simple if you are armed with the knowledge to help you avoid scams. Always be skeptical when you are using the internet or communicating via e-mail, and remember that if something seems too good to be true – then it probably is.