Protecting Your Privacy from Tools like RIOT and PRISM
Introduction
The RIOT or Rapid Information Overlay Technology software application was developed by Raytheon. RIOT is revolutionary in the fact that it performs social network data mining across all social networking platforms, mines location information in graphics posted by users, creates maps of online relationships in record time and timelines of user activity.
However, RIOT is not the first social network data mining software out there and the use of data mining in conjunction with large-scale analytics is only going to increase over time. PRISM became public in June of 2013, doing the same analysis of not only social networks but all of a person's online activities. Big Data is here, and it helps the government watch everything you are doing.
How then can you protect your privacy in the face of Big Data becoming Big Brother?
Minimize the Aggregation
- Don't get in the habit of talking about your activities online, providing fodder for a pattern to be created.
- Make it harder to have your pattern correlated. Don't use the same computer for all of your online activity, as they can be linked by IP address. Don't use the same user name on all social media platforms. Don't put your instant messaging ID on your personal social networking page or your Twitter account in your email signature.
- Change user accounts periodically, but don't follow the same pattern. For example, create new email addresses, social media accounts or web pages. Don’t replace a Google account based on your initials with an Outlook account based on your initials.
- Maintain distance between your online profile and your personal life. Don't talk about vacation plans, your spouse, your children or your job on social media sites where you also discuss political matters. Even if the political site profile doesn't reference your phone number or business name, someone could search for similar discussions about the same people and events and link the identities. For example, talking about your upcoming camping trip to X location on Y date on different forums gives data miners information that could be used to link all accounts on which you discussed the upcoming trip - and more correlations when you talk about the trip when you return.
- If you have several accounts as fall-back accounts in case the primary one is banned, maintain them. Log in under these accounts from time to time, and post comments occasionally. Then the change in behavior is less obvious than a silent account suddenly becoming active. And do not create the replacement account when you shut down the old one; the time stamps are close enough to be correlated.

Maintain Your Privacy
- Don't talk about your activities in public chat rooms and forums. If you want to talk to someone privately, visit them in person or pick up the phone. However, telephone conversations are also subject to being recorded and analyzed by software, as are conversations in public places such as restaurants. Look for signs at the entrance that state that audio and visual surveillance is in use before you make a call you want to be private.
- Be careful of friend requests. This opens the door to being watched by a false persona. There are software applications now that allow one social media manager to simultaneously monitor and maintain ten false profiles.
- Use VPN and other tunneling to limit the ability of others to track your connection to the internet.
- Teach your children to respect your household privacy. Don't let your children talk about upcoming trips, parents' political beliefs and personal details online.
- Turn off the GPS on your phone if you're not lost, and don't let your phone post you location when you post pictures online.
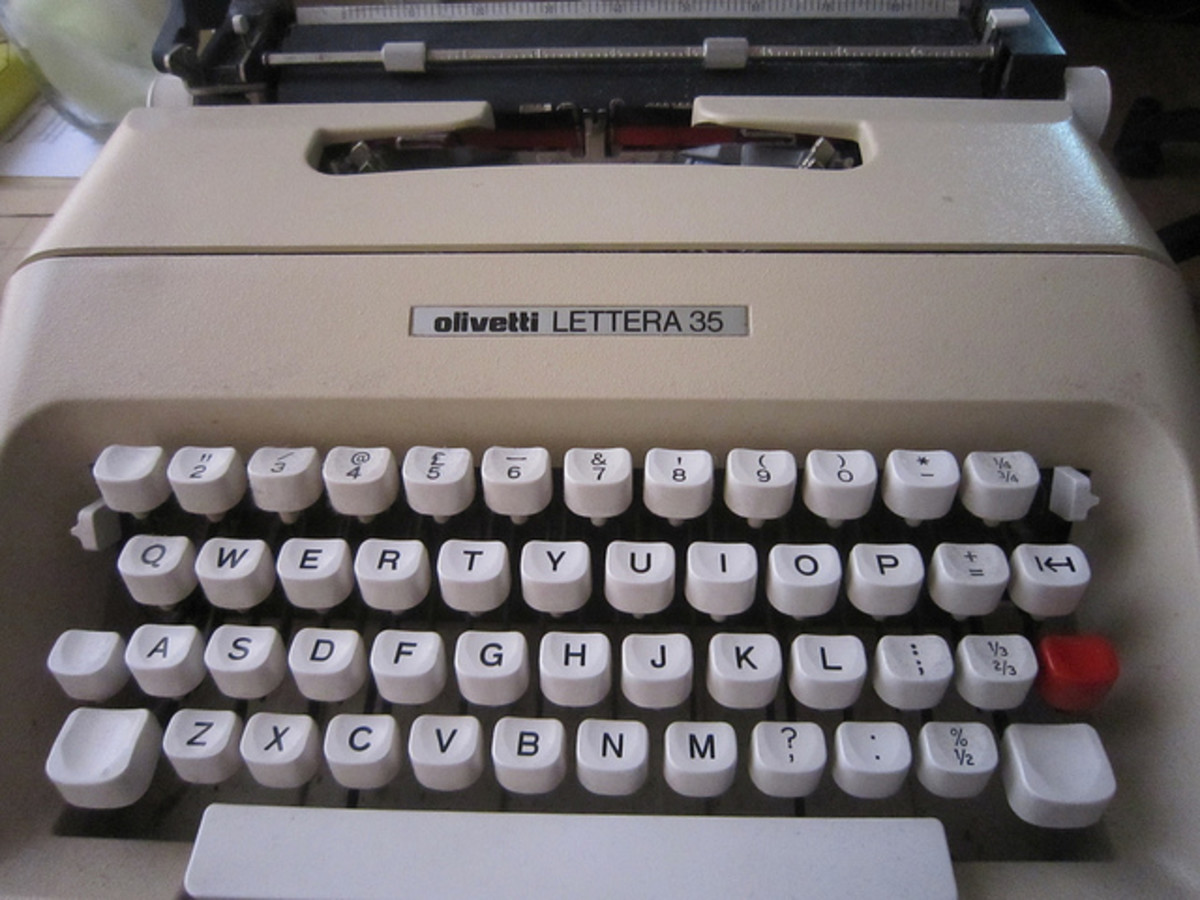
- Many high-end cameras can also record your GPS location on the picture, digitally and invisibly. Be certain to remove such information before you post these pictures to any public sites.
- Use social forums behind pay walls and invitation only chat rooms for more privacy. But never assume these sites are truly private. Even if every person with access to these more private sites has been vetted in the past, their accounts may be hacked, giving someone access to the site under their identity.
- Don't save social media passwords in your browser, and don't use the same passwords for your social media accounts.
- Don't let people around you get in the habit of posting pictures of everything they are doing online, including pictures of you. There are data mining tools other than RIOT by Raytheon that can search for your image among pictures taken by others, and this technology will only improve over time.
- Use different devices to access your social media pages. The RIOT app can track devices by their addresses as well as individual behavior.
- Keep your firewall up to date, scan your computer regularly and use multiple anti-virus tools.
- If you do not want apps like this to know where you are going, don't log in online while traveling.
- Limit your rants online. This increases the odds that you'll fall under suspicion.
- Use a captcha app or something similar to prevent drunken or late night postings online. Stop yourself before you say something you don't want to have read and analyzed. Once you attract attention, you’re more likely to be included in future searches for suspected troublemakers.
- Don't post your picture on your social networking profile, or the same pictures of your pets and favorite scenery.
- Never use a government issued cell phone for any type of texting, instant messaging or email unless you want the government to know what you’re saying. The same caution applies to such activities from your employer's computers.
- Don't assume that text embedded in a JPEG or graphic file is going to go unsearched, though terrorists have used this method to send messages to each other when planning attacks.
- Pay with cash instead of a cell phone or credit card to protect your purchase history. Don’t use your primary credit card or bank account to pay for pay-wall subscriptions to access private websites/forums/servers. Don’t share your Paypal address unless truly needed to receive payment. Protect your payment information – this is a form of personally identifiable information, and very valuable in an era where email addresses and user IDs change often but bank accounts rarely do.
What to Do if You Don’t Want to Break the Pattern
- If you do post information online, maintain your current appearance and pattern of activity. For example, keep your professional profile professional and your personal profile personal. If you want to discuss politics, use a different profile or different social network entirely for those discussions.
- Sudden shifts in tone and emotion get flagged. If you’re ready to explode on a topic, call someone to talk about it instead of posting online comments about how you’d like to radically reinvent the nation. Unless, of course, you’re already talking about this sort of thing in your online account.
- Change group associations slowly over time if you need to do so. Suddenly dropping all political groups and notifications is the type of change software like RIOT will be able to capture. The same is true of suddenly dropping all connections with one particular person.
How to Break the Pattern on Purpose
You may want to protect your privacy by not maintaining a pattern that could be used by others. In these cases, you will want to break the pattern these tools will see on purpose so that changes you want to make will not appear suddenly. How can you break the pattern social network data mining tools and data analytic software will see?
- RIOT can build a map of your online social relationships. If you change your social media profiles periodically, don't immediately reconnect with all your old friends - this can be used to identify you as you or at least flag your new profile as very similar to the old one.
- You could interfere with the pattern by letting others log into your computer and generate a totally different history and behavioral pattern.
- Occasionally log in on public computers to accounts that are tightly tied to you, reading generic messages and deleting spam.
- Vary your schedule so that changes in behavior later are less obvious. Better yet, don't tell the world what you are doing and where you are going.
- Vary the times you check your email, post updates and check in with others. Then later shifts in the places and times you log in won’t be flagged as a sudden change.
- There is a reason the President takes different routes each time. Alter your routes to and from meetings and locations if you want to throw off pattern recognition software. Don't go to the same Internet cafe to check your email. Don't visit the same websites in the same order. Go to a different spot to check your text messages.
- Vary the analogies you use to describe things.
- Overwhelm the monitors. The more inane posts and generic conversations you have, the harder it is to find potentially suspicious discussions. Re-posts of jokes and news headlines adds to the volume through which software and users must search. However, posting and re-posting generic articles and jokes punctuated by "real" discussions is itself a pattern. Mix it up.
- There has been increasing use of handwritten sheets of paper held up in a photo to prevent the use of someone’s text taken out of context to twist their words. Use the same method to share your opinion, so that your text cannot be taken out of context or easily searched by an application like RIOT. You can use the same concept in a new way, such as creating text in another font or art and then posting a screen shot of it online as long as the screen shot doesn’t include your computer’s identifying information.

Planning Ahead for the Future
- Recognize that you don't have to be under surveillance now to be analyzed later. If you don't want something to be found out, don't post it.
- Encryption is useful, but only to protect data on your device or email communications. Encryption software won't prevent public postings from being data mined.
- The RIOT application has already been used to track both people and devices across cyberspace. If you want to hide your identity online, pick a user name that is the online equivalent of "John Smith". Then it is harder to identify which "John Smith" you are and build a clear picture of your online behavior.
- Mix up your message with multimedia. Use video one time to send a message and text on a forum another. Take a picture of yourself holding up a sign one time and send an audio file the next. Data mining tools like RIOT work best with text.
- If you have an article or manifesto you want to publish, rewrite it instead of copying and pasting. Run it through a plagiarism checker if necessary to make each version sound sufficiently different to not look like you are posting the same thing over and over again across the web. Or use article spinning software to make each edition different.
- If you want to meet up with someone, a very large gathering for innocuous purposes is more private than two people arranging a private meeting. The crowd provides anonymity.
- If you are concerned about having your conversations monitored via Carnivore or data mined by software like RIOT, communicate via methods it doesn’t include in its aggregation. Contact friends using ham radio to discuss things like meeting times and locations. While ham radio broadcasts are public, they are not monitored, nor is it data-mined like internet postings. Or communicate through the chat features in online games. The communication is public and available to system administrators of those sites and gaming forums, but it isn’t reviewed along with your emails and social media updates.