Secure Your Local Data - Offline Protection - 2

Password - Protect Everything
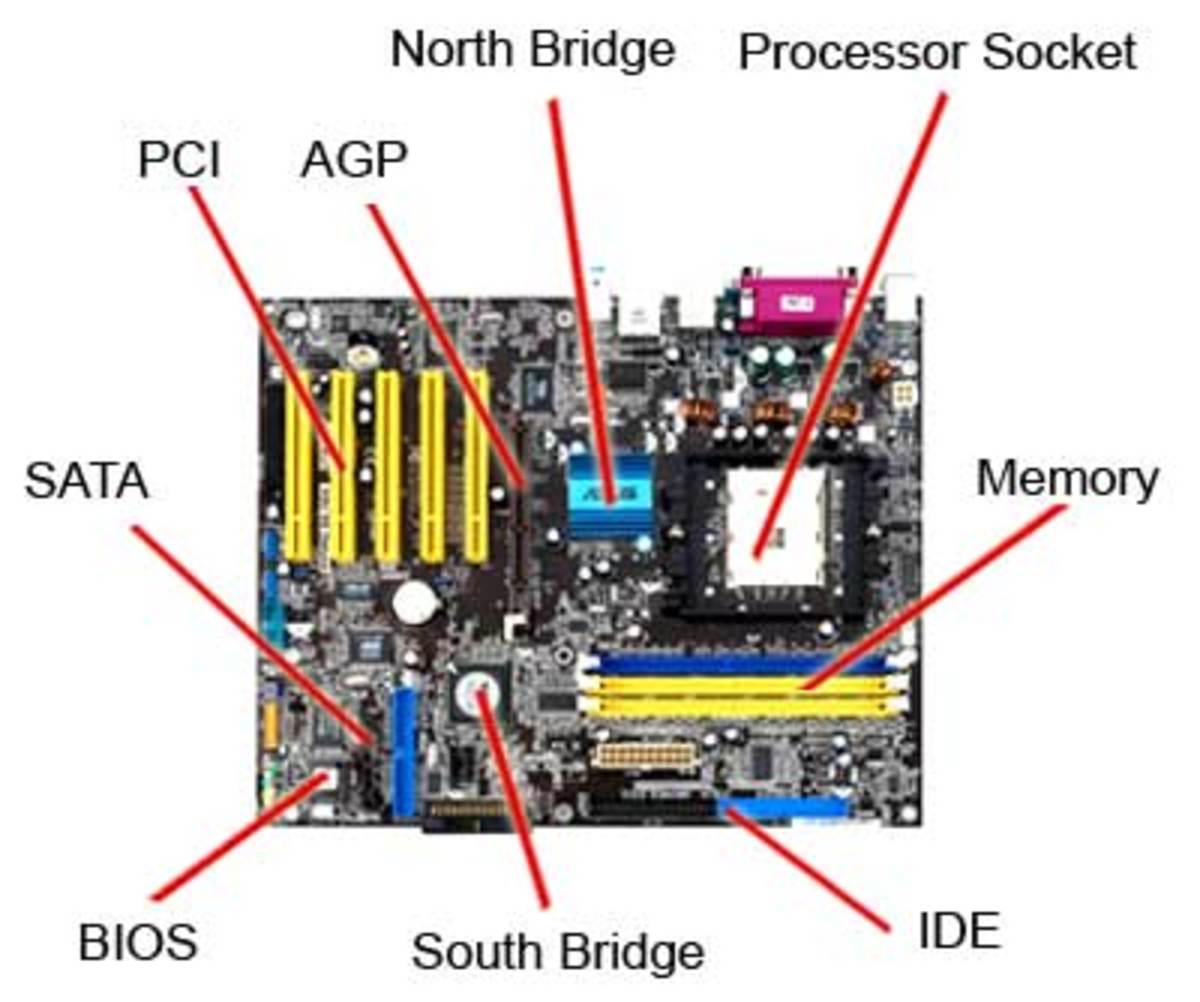
Preventing unauthorized users from accessing data means creating a password for everything. You can create a password lock form the very instance your PC starts up by setting a BIOS password.
The next step is the operating system for which you can create different user accounts, each with its own password. You can even lock and hide specific folders and files so that they cannot be run, copied or transferred without a password.
To create a BIOS password, you must enter the BIOS setup before your OS can load. When you boot your machine, the screen will display a series of diagnostics along with which there is an instruction to enter the BIOS setup. This is most commonly done by pressing [Del] or [F2]. In the BIOS setup, there is security tab, which gives you the option to set a user password so that your system requests for password authentication before loading your operating system. After setting the password, remember to change the BIOS settings to prompt for a password every time machine is started. You will find this in the BIOS features setup menu.
You can also use security software that enables you to lok specific files and folders. Top Lang Software have created a program called File Lock 6.1, which gives you the ability to lock files, folders or entire drives. You can also hide files and folders from your file explorer and you can even lock your CD/DVD drives. Using such a tool, you can prevent your data from being copied or stolen form your personal machine.
Create Backups
There is no telling when or how your files might get corrupted; either due to a software malfunction or physical damage to your hardware, so it is best to take safety measures by creating backups of your data. You can either use the ever growing space on cloud servers for your backups or simply save multiple copies of files on different drives. For creative backups of large amounts of data, however, you might need to use certain backup software. PCs from established manufacturers like Lenovo, HP or Dell often come with their own security suites with a backup feature. If you do not have such a suite, you can use software like EaseUs Todo Backup or Cobian Backup, which come with options for creating backups of specified folders or entire drives. Some backups software also give you options to encrypt data and compress files to reduce the size of your backup drive or folder.
Get a Good Security Suite
The best form of protection from viruses or malware is a reliable antivirus application. Most security suites these days come with a variety of services bundled into one; from virus protection to spam blockers, so good security software can help you protect your PC in many ways. It is also wise to invest in the full, paid version as the free once sometimes come as a limited time trial versions have some features blocked. It is also important to make sure your software is up-to-date. Antivirus programs are regularly updated with the latest virus database and fixes for loopholes, so configuring regular updates is very useful.
Encrypt Your Data
If you are going to transfer or exchange valuable or sensitive data fro your machine either over the Internet or via external storage, you want to ensure that it cannot be accessed by third party users. In such cases, you should use encryption software to protect your data.
Microsoft bundles Bitlocker to Go with certain versions of Windows 7 and can be used to encrypt data on your PC and removable drives. Although the software is available only with Windows 7 Ultimate or Enterprise, the encrypted files can be read even on Windows Vista or Windows XP operating systems.
You can also use truecrypt, Which is a free. multiplatform open-source file encryption program. Truecrypt allows you to encrypt files by creating a folder on your drive and placing sensitive documents within the encrypted folder, or you can encrypt entire partitions or storage devices such as a USB flash drive or a portable hard drive. The program uses multiple encryptions algorithms and stores encryption files in a TrueCrypt encrypted volume on your storage device, which is identical to a normal folder, making identifying encrypted files almost impossible.