SMARTPHONE SAFETY - 1
SECURE EVERYTHING
Smartphones these days are capable of doing almost everything a low-end PC can do, which is why the growing number of smartphone users often choose to do their work directly from their phones. The increased activity on smartphones, especially involving Internet usage, has resulted in their rapidly increasing popularity as a target for privacy and security attacks. While uninformed users might surf the Web, socialize, transfer files and pay their bills from the convenience of their phones, they leave their personal information, financial information and data vulnerable to attacks.
Mobile phone threats come in many different forms and they are becoming more sophisticated. With the source code to operating systems available, it is much easier for developers to create malicious software or find ways to tap into your phone. There have already been many reported cases of attacks on phones via open Wi-Fi access points, Bluetooth connections, and applications, so it is important for users to take preventive measures to avoid being the target of an attack. There is also the most basic threat of physical theft resulting in data loss and data leakage for which also there are preventive measures.
WHAT IS THE THREAT ?
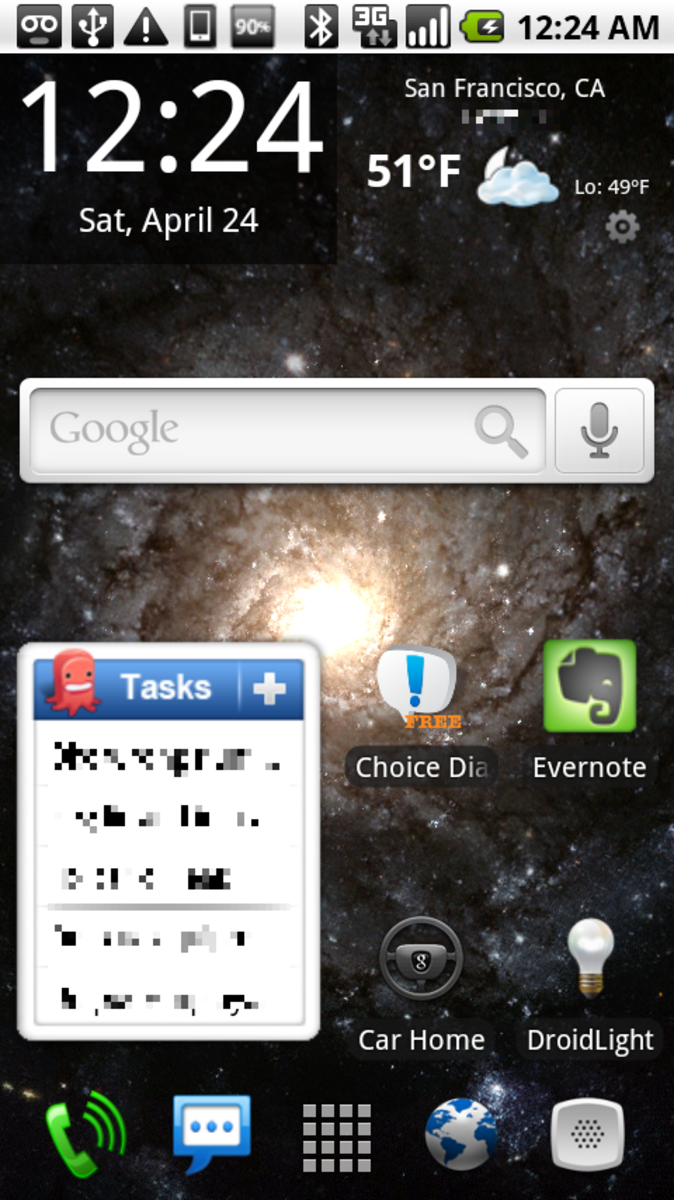
There is a range of ways to gain access to an unprotected mobile phone. Apart from open Wi-Fi networks, an experienced hacker can exploit your phone's Bluetooth connectivity, 3G access or through malicious applications. Once the attacker has access, a lack of protection or poor security settings leave your data open to a multitude of threats and attacks and the increasing use of cloud services means attackers can move through the Internet faster than even before.
The development of operating systems for different devices means the same malicious software that affected PCs can now affect your smartphone. The open nature of Android and, to a lesser extent, Windows Phone makes these OSes easier targets for viruses. Other threats include unauthorized access, increased charges through cross-service attacks, eavesdropping and SMS spamming, all of which can lead to leakage of sensitive data and information.
HOW IT'S DONE
Malware and viruses can infect a phone through e-mails, SMSs, open Wi-Fi networks and even Bluetooth connections. The greatest mode of spreading malware, however, is through applications downloads, which is of real concern specifically for Android users after a study by juniper Networks in May 2011 revealed a 400% increase in Android malware. Viruses can sometimes infect multiple files on a device and then spread across devices when files are transferred over the Internet or via Bluetooth.
Cross-service attacks are more a threat to the owner's pocket than they are to data. The availability of multiple forms of connectivity on one device means an attack carried out through one interface might give the attacker access to another. For example, an attack through your phone's wireless network interface might enable the attacker to use your phone functionality to make long-distance calls or send large volumes of messages, much like an e-mail worm that sends mass e-mails from your account.
Eavesdropping is a threat to all Internet users, irrespective of the device they are functioning from, but it is far easier for a hacker to access packets transferred between a smartphone and a server due to the lack of encryption user by mobiles. An unprotected wireless network can be manipulated to leak data packets to users other than the Intended targets.
Another method of infection is through spam SMS. While SMS spam may seem innocuous at face value, it can be quite harmful if not dealt with correctly. Most users would think the worst a spam message could do is annoy you, but clicking through to a links in an SMS could leave you vulnerable to unauthorized downloads and infection through malicious sites. Sometimes spam SMS is sent through premium charges numbers and responding to a quiz or poll can incur high billing costs.