- HubPages»
- Technology»
- Internet & the Web»
- Viruses, Spyware & Internet Security
New Computer Scam Alert: Your Computer Has Been Hacked?!

"Warning" Message
After Window 10 Anniversary Update last year, my laptop has run into many problems: first, Norton Antivirus Program incompatible issue causes Window to crash (luckily I found the solution to that on my own), and then a few months ago, after an automatic window update around November 2016, my computer suddenly gets very slow. The desktop was brought up fairly fast, but afterwards, it takes about 10 minutes for any program to be active, and another 5-10 minutes for internet to work properly. Before my PC can start working, I had already wasted about 15-20 minutes. Comparing to the old, reliable Window 7, this so-called much improved Window 10 has brought me tons of trouble since its debut. Adding to the list of headaches, on the eve of Chinese New Year (January 27, 2017), my internet suddenly froze, and I got a message on the screen telling me my PC has been infected with a spyware & virus. I was urged to call the number listed.
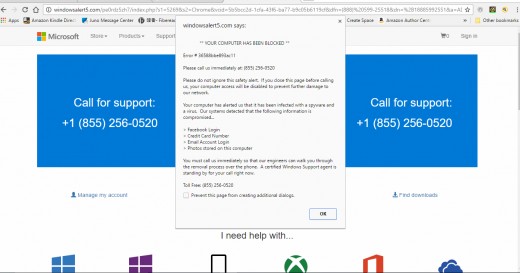
The “Error” message as follows:
Please call us immediately at (855)-256-0520
Please do not ignore this safety alert. If you close this page before calling us, your computer access will be disabled to prevent further damage to our network.
Your computer has alerted us that it has been infected with a spyware and virus. Our systems detected that the following information is compromised…
- Facebook Login
- Credit Card #
- E-mail Account Login
- Photos shared on this PC
You must call us immediately so that our engineers can walk you through the removal process over the phone, a certified windows support agent is standing by for your call right now.
Virus Alert Message
Close Encounter With A Real Hacker
The “Error” message seems to confirm my worst fear. So I follow the instruction and call the number.
After 5 or 6 rings, a man with heavy Indian accent picks up the line. He claims to be working for Microsoft. His name is David Williams, and he currently locates at North Carolina. I tell him my situation. He asks me to press “Window Key” and letter “R”. The “Run Dialog Box” pops up. He tells me to type in some kind of command, and download “GoToAssist” onto my PC. (GoToAssist is a cloud-based service that enables the user to access and control remote computers and other Internet-connected devices in order to deliver technical support.) He says he can use my mouse and keyboard to move around my network and seek out the “Hacker” and collect information on the files that were hacked into.
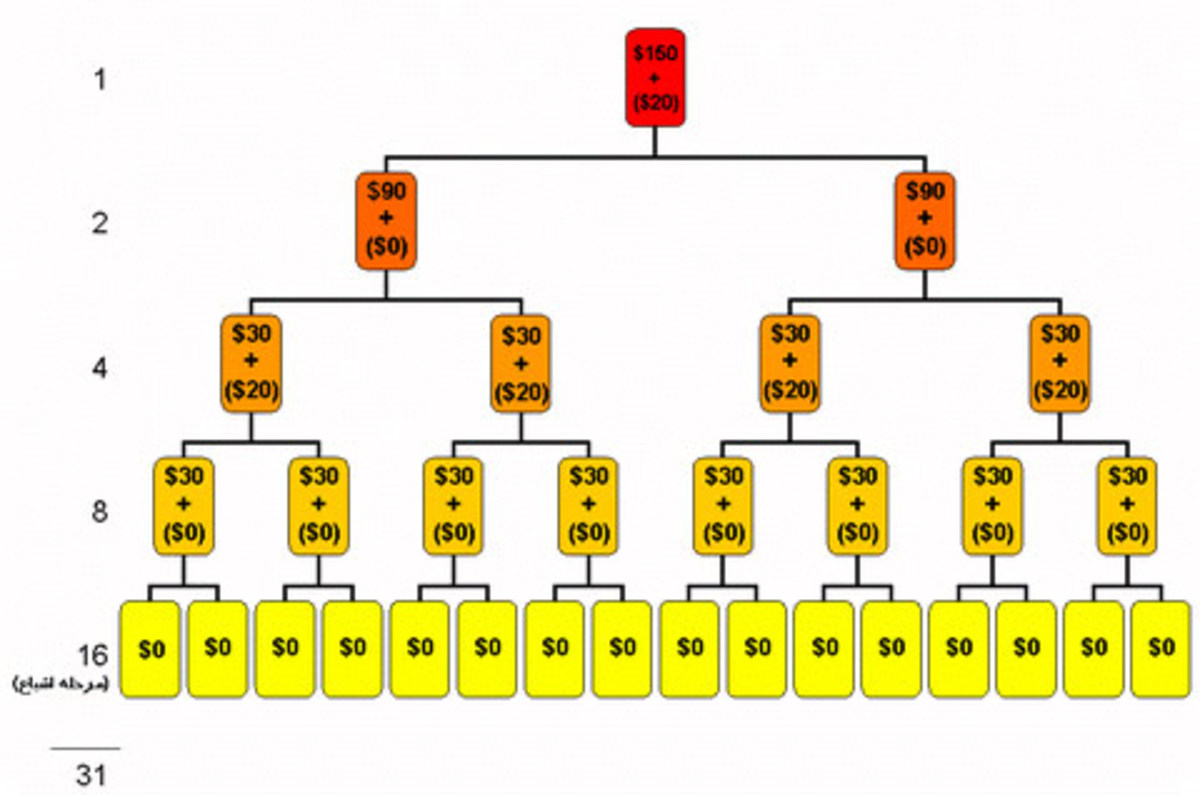
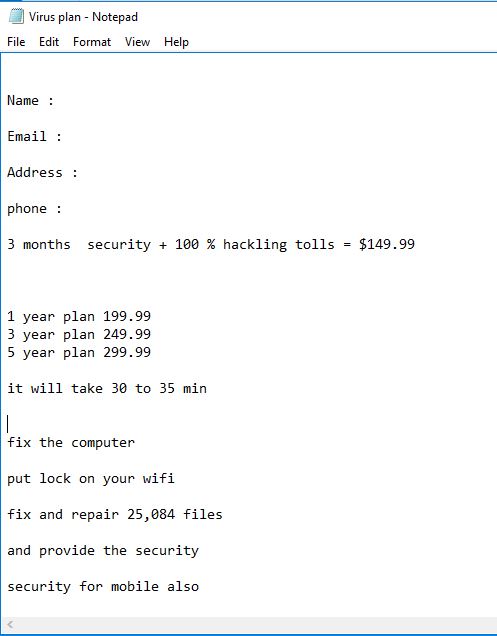
He then visits several websites: “advanceddiidentityprotection.com/downloadnow.asp”, “geek_typer.com”, pulls out a snapshot of a guy that looks like a criminal (a middle-aged, bearded white male, with curly long messy hair), and tells me this is the hacker. Furthermore, he shows me a list of files that the hacker “hacked” into. He even identifies the Hacker’s exact location, which is somewhere in the state of OH. This sounds more and more real and serious. I demand him to send the hacker’s information to the authorities, so that the “Hacker” can be captured and prosecuted. He says he will do that once I purchase the security plan he offers. However, if I refuse to pay, he will not send the Hacker’s information to the authority. I ask him how much his service will cost me. He opens up my notepad, tells me to key in my “Name”, “Address”, “E-mail”, and “Phone #”. Below that, he lists 3 plans: 1 year $199.99, 3 years $249.99, 5 years $299.99. I ask him whether he has something that will solve my current plight. He says he also has 3 months-plan starting at $149.99, and for safety reasons, he won’t accept credit cards, only take my bank account information over the phone.
Hacker's Offer
My Battle With the Hacker
I tell him, I need more time to think about it, or shop around for a better deal. He gets nervous, informs me not to trust others, saying some repair shops might put a virus on my PC and not really fix it. He also claims the problem I’m having has nothing to do with my PC, but my Network. The “Hacker” hacks into my entire network, puts a virus there. Unless I obtain a security plan from him, the problem will always exist. Fearful the whole thing might be a scam I suggest that I will call him back the following day. My proposal sets him off. He gives me the ultimatum: if I don’t buy the service from him now, he will have no choice but kill my PC to prevent further damage to the network. He further states that his phone has been ringing off the hook and many people try to reach him to get help (but all I hear is silence on the other end). He says he’s been wasting lots of time on me, and urges me to give him my answer at once.
The threat alarms me, he just said the problem is the network not my PC. So killing my PC to save the troubled Network does not make any sense. I point out to him that he’s holding my PC hostage. This time he gets really mad and drops his act, “I’m going to kill your PC right now, so you will lose everything in it and never be able to use it again!” he roars and hangs up the phone. Right away, he starts typing some kind of command in the Run Dialog Box. Sensing the severity of the situation (the whole thing could be a scam and the guy with strange accent might be the true hacker) I quickly take back the control of my own computer, close all programs and shut down the PC and internet so that he cannot execute his threat.
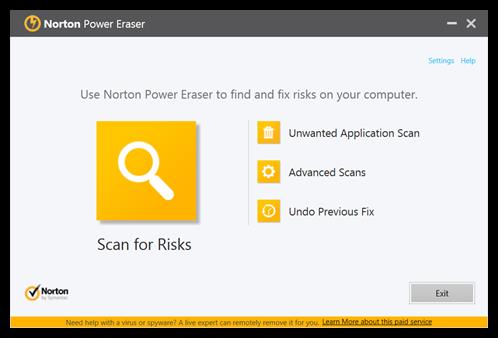
The next day (after a night of combing my thoughts), I remove the software he puts on my computer, delete some unnecessary or questionable old software, perform “disk cleanup”, run antivirus scan, finally to be sure, I download and run “Norton Power Eraser”- no virus is found. After doing all that, I notice straightway my PC gets a lot faster and no more pop-up “Error” message blocks my internet. I research the incident on the web. Sure enough, what I had been thru indeed is a scam (others have experienced the same ordeal on the same day). Luckily, the last minute, my intuition saves me from being swindled.
"Virus Warning" from another Hacker
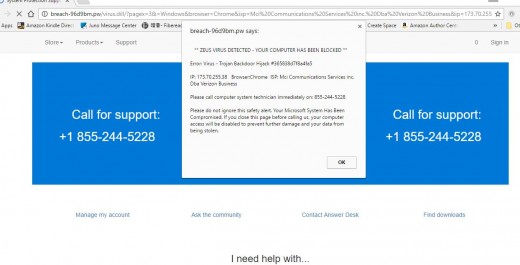
Windowsalert5.com says call Microsoft --- Scam!!!
- windowsalert5.com says call Microsoft - Virus, Spyware & Malware Removal
windowsalert5.com says call Microsoft - posted in Virus, Spyware & Malware Removal: Hello, Today while surfing a look at 19 forbidden islands to travel to, linked through yahoo, I suddenly had the site replaced with a warning from Microsoft and
Norton Power Eraser
Scam Warning Signs:
- Be careful of “facebook” alert message. For at least two weeks, every time I check my facebook message, a warning notice would automatically pop up, asking me to confirm my location. In the past, I only need to confirm once, but strangely, the message keeps coming up every time I use facebook. Now that I think of it, a hacker might have found a security hole in “facebook”, using it as a bridge, and tricking the unsuspecting user to allow the hacker into their network, disable the internet.
- The so-called “on-line technician” identifies himself as David Williams (a pretty common “American” name), yet he holds a strange foreign (Indian) Accent.
- He claims he’s working for “Microsoft”, but his company’s website indicates “Microsoft Partner Network”. It’s misleading because of the word “Microsoft”. However this company has nothing to do with the real Microsoft Company.
- He’s able to seek out the “hacker” and gets his name, picture, even location in a matter of a minute, yet he claims he does not know my current position, and he keeps asking me personal questions like what I do for living, where I live, what school I go to etc.
- He claims the “Hacker” hacks into my network. The slow response of my PC is due to the hacking, and my PC works perfectly normal. Even if I purchase a new PC, the same problem still exists. Purchasing the security plan he offers is the only way to solve the issue (and his Security Plan includes: place a lock on my Wifi, fix and repair over 25000 files, provide security for mobile devices). Ironically, after I refuse to comply, he threatens to “kill” my PC (that should give you the red flag—he is actually the scammer. A professional technician would never make such threat.)
Free Virus and Spyware Removal Tool - Norton Power Eraser
What to do when you are “attacked” by a Hacker?
- Remain calm: do not call the phone# provided by the “Error” message. Close the web page by right clicking on the active Web Browser icon on the task bar, select “Close Window” or end the task by using “Task Manager”(Press Alt + Ctrl + DEL).
- If you’re “Hacked”: Delete the spy software on your PC. Go to “Control Panel” on your PC, select “Program” (uninstall a program), find the software the Hacker just installed onto your PC click on “uninstall”. Use the same method to delete other useless old software that might post security threat (example: Java™ 6 Update17, or other old version of Java.)
- Run “Antivirus Scan”: run a quick scan to remove possible threats, for hard to detect Viruses, Run “Norton Power Eraser” (It is a free tool that can be downloaded and run to remove serious threats from your computer.)
- To improve PC’s speed and performance: run “Disk Cleanup” on your PC (it will delete unnecessary files, free up space and speed up your PC.)
To download “Norton Power Eraser” for free, go to:
How to remove a virus from your computer! - How to remove Malware - Windows 10 Free & Easy
Final Words:
Behind every bad incident, there is a good lesson learned. This shameless hacker teaches me to remain calm under a horrible threat, use my mind and trust my intellect, and most importantly, have the confidence, courage and wisdom to solve the situation. For all the knowledge I receive and lessons I have learned:
Thank you HACKER for giving me this wonderful Chinese New Year present- Be Brave, Be Smart, and Never Give In To Threat!!!
I have a strong feeling that the year of “Fire Rooster” is going to be adventurous, fruitful and rewarding.
If you think this Hub is helpful, please share it with your family and friends. Scam like this might happen to anyone, anywhere. Be prepared before it happens to you!
Always Meet A Challenge With A Smiley Face