Securing information on the internet, intranet and in your pocket
Public networks such as the Internet do not provide a default means of secure communication between entities. Communication over such networks is susceptible to being read or even modified by unauthorized third parties.
Cryptography helps protect data from:
- Being accessed without permission
- Provides ways to detect whether data has been modified
- Helps provide a secure means of communication over otherwise non-secure channels.
Protecting communication on the private or corporate intranet in the same manner information is protected on shared networks is important. Company security is commonly breached from internal rather than external sources.
A good heuristic is “every message sent is encrypted and signed”, this simplifies governance and compliance issues, and promotes a secure by default mindset.
A secure by default mindset should extend to all information being moved from one place to another, including moving files on USB drives and external media; an aspect often overlooked as workers take files home without encrypting and password protecting the information first. Many a USB has been lost in transit.
Goals of cryptography
Cryptography is used to achieve the following goals:
- Confidentiality: To help protect user identity or data from being read
- Data integrity: To help protect data from being changed
- Authentication: To ensure data originates from a particular party i.e. you are who you say you are.
- Non-repudiation: To prevent a particular party from denying they sent a message.
To achieve these goals, you can use a combination of algorithms and practices known as cryptographic primitives to create a cryptographic scheme.
Summary of cryptographic primitives with uses
Cryptographic Primitive
| Use
|
|---|---|
Cryptographic signing
| Digital signatures are becoming more important as the world moves away from paper documents, digital signatures provide assurances that help verify data originates from a specific party by creating a unique digital signature.
|
Public-key encryption (asymmetric cryptography)
| Performs a transformation on data to keep it from being read by third parties. Public-key encryption uses a public/private key pair to encrypt and decrypt data. Some public-key algorithms (not Diffie-Hellman^) can be used to create digital signatures to verify the identity of the sender of data.
|
Secret-key encryption (symmetric cryptography)
| Performs a transformation on data to keep it from being read by third parties. Secret-key encryption uses a shared secret key to encrypt and decrypt data.
|
Cryptographic hashes
| Maps data from any length to a fixed-length byte sequence. Hashes are statistically unique; a different two-byte sequence will not hash to the same value. Hashes are typically used to validate the integrity of files and messages, password verification (no storing the passwords in plain text), and file content identification with checksums.
|
Block Cypher
| A block cipher is a primitive often confused with hashes. Block cyphers are building blocks in public/private key cryptographic schemes.
|
* EC = Elliptical curve (description below)
^ - Largely for historical and commercial reasons, RSA created a Certificate Authority for key signing that became VeriSign.
Block cyphers and hashes, whats the difference?
Block cyphers are different from hashes in the following ways:
A block cipher has a key; the secrecy of the key is what the cipher security builds on. A hash function has no key at all, and there is no "secret data" on which security of the hash function is to be built
A block cipher is reversible: if you know the key, you can decrypt what was encrypted. Hash functions are meant to be non-reversible. Hashes used to store passwords in computer systems ensuring that even the administrators cannot view your password in plain text, remember, secure by default!
A block cipher operates on fixed-sized blocks, both for input and output. A hash function has a fixed-sized output, but should accept arbitrarily large inputs.
Summary of cryptographic primitives with examples
Cryptographic Primitive
| Example
|
|---|---|
Cryptographic signing
| Digital Signature Algorithm (DSA) and Elliptic Curve Digital Signature Algorithm (ECDSA*)
|
Public-key encryption (asymmetric cryptography)
| Diffie-Hellman (DH) , Elliptic curve Diffie-Hellman (ECDH)*, Rivest-Shamir-Adleman (RSA), DSA and ECDSA*
|
Secret-key encryption (symmetric cryptography)
| Data Encryption Standard (DES)(not used), Triple Data Encryption Algorithm (TripleDES) and Advanced Encryption Standard (AES – Rijndael based)
|
Cryptographic hashes
| MD4 and SHA-3
|
Block Cypher
| Blowfish, Rijndael, Twofish
|
Why is elliptical curve cryptography stronger than the current standard?
Public-key cryptography is based on the assumption that it is difficult to factor large integers composed of two or more large prime factors. For example users of the RSA algorithm publish the result of multiplying two large numbers together along with an auxiliary value as a public key; it is difficult to determine the exact number sand the auxiliary value used to produce the result if you have no prior knowledge of them.
New discoveries in the fields of mathematics and increased access to computational resources are challenging this assumption.
Elliptic curve algorithms make it significantly more difficult to find the initial values (crypto graphic keys) due to the mathematic nature of the algorithm used to create the keys.
Elliptic curve keys provide stronger security with small key sizes. Your bank, for example, uses a 2048 bit RSA key to secure its internet banking site, a 256 bit elliptical curve key would provide comparable security to a 3072 bit RSA public key, and with a much smaller key size allowing space for it to become even more complex.
What’s the difference between Transport Security and Message Security?
Transport security refers to the security of the communication channel; one example is
Secure Sockets Layer (SSL), you use SSL when you pay for things online, the URL
begins with https// instead of the usual http://. The secure channel is only secure between two
points, if the same message is now passed to a third point; the message is now
in plain sight and is insecure
Transport Security
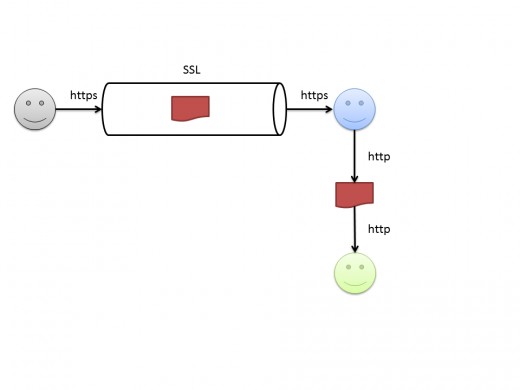
As you generally do not know what happens to messages you send after the recipient you sent them to received them, if security is a real concern message security is better suited.
Message security means every piece of information sent over any communication channel is encrypted and signed; ensuring end to end security regardless of the path taken.
How safe is safe?
It’s reasonably safe to assume any encryption method in mainstream public use can be broken by using legal or covert channels to gain access to the encryption keys.
The history of encryption indicates that methods available to the general public are many years behind those available to the governments and military organisations of the world, stronger methods are likely to remain classified for a period of time before they are available for mainstream adoption.
For short-lived information, short-lived means the information is only relevant for a limited period of time, modern encryption methods suffice.
For more durable secrets, given enough time and computational resource, it is safe to assume any cryptographic scheme can be decrypted. Currently the time dimension is long enough to invalidate the usefulness of most secrets, but the horizon’s shrinking all the time.
What should I do?
Have a conversation with your colleagues about what information is in use that’s either confidential from a legal perspective or from a competitive advantage perspective. Find out where data is stored, and where it goes both physically and electronically, is it secure?
If you design or mange distributed IT systems, could you say every message sent within the system is secure by default, both internally and externally? If not, why not? There may be simple things you can do now to prevent an embarrassing conversation later.
If you do take work home, pop it on a USB drive, zip it up and protect it with a password at the least.