The Seven Best Smartphone Security Tips

More and more people are adding smartphone use to their daily lives. With business and personal smartphone use becoming ever more common, individuals who own smartphones are at a similarly elevated risk of being targeted by identity thieves and hackers -- even with a mobile antivirus program running. Fortunately, these suggestions can help ensure that your smartphone does not become a liability to your financial or personal safety.
# 1: Enable Remote Phone Access
No matter how careful you are, losing your phone or having it stolen is always a possibility. Fortunately, this can be nothing more than a minor inconvenience with a little planning and advance preparation. It is possible set up pre-installed feature on some modern smartphones that allow you to disable use of a phone should it get lost, to track the phone down by GPS and even to wipe it clean of personal data should recovering it prove impossible. Other smartphones will not include these features initially, but a variety of apps are available that you can install to accomplish the same purpose.
# 2: Remember to Back Up Data
It is common knowledge today that any important pictures, papers and other files on a computer should be backed up regularly. Oddly enough, this knowledge often does not seem to extend to files stored on a smartphone. However, for many people, a smartphone is a means of storing and transporting many of their most important such files. Backing them up could mean the difference between an inconvenience and an irreplaceable loss. when you lose your phone or suddenly need to replace it. If your cell phone did not already contain a backup feature when you purchased it, installing an app to handle this responsibility should be at the top of your priority list.

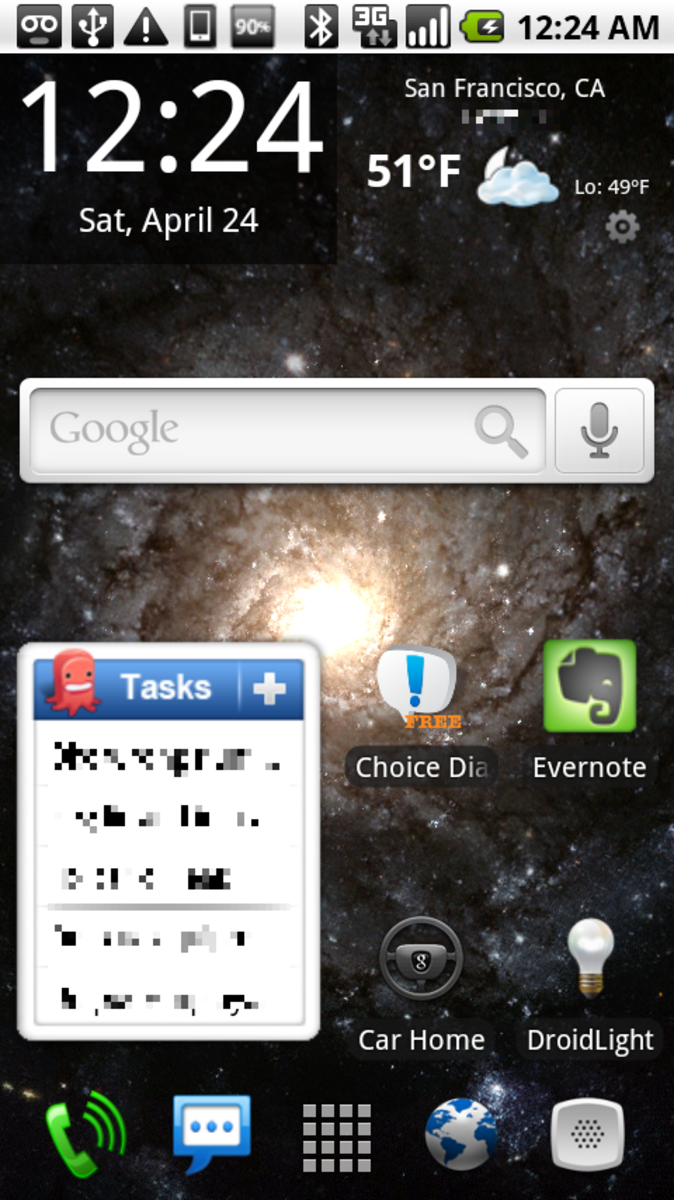
# 3: Lock Your Screen
Some type of screen lock feature is already built in to most of today's smartphones. Of course, whether based on a pattern, a numerical code or some other security device, these lock screens usually would not be enough to prevent an advanced identity thief from accessing your phone's data eventually should your phone be stolen. However, enabling your lock screen is still a wise precaution simply because it can help deter more casual hackers, who tend to prefer unsecured phones.

# 4: Avoid Public WiFi Networks
Taking advantage of an unsecured public WiFi network can be tempting, particularly if you do not have unlimited data included in your smartphone service plan. Unfortunately, your phone is particularly vulnerable while connected to this type of network. At the very least, you should avoid using a public WiFi network while you perform any financial transactions or similarly sensitive activities.

# 5: Only Root Secondary Phones
Many electronics gurus enjoy tinkering with their cell phones to allow them to accomplish more than they were originally able to do, a process known as "jailbreaking" or "rooting." Unfortunately, this generally requires you to disable the security protocols the manufacturer originally built in to the phone, making it a much more tempting target to a hacker or identity thief. That is not to say that you cannot enjoy this hobby, but rather that you should leave your primary phone alone and only tinker with spares or backups that contain no sensitive information.
# 6: Only Install Verified Apps
You can take every possible precaution to protect your phone, but installing one unsavory app could leave you a victim regardless. You should generally avoid installing apps from a source your phone does not recognize to minimize the possibility of your phone becoming infected with a virus. Apps that you install from your phone's official app provider, like Google Play for Android phones or the App Store for iPhones, will already have been checked for safety.
What type of smartphone do you prefer?
# 7: Wipe Outdated Phones
Lastly, when you replace your smartphone, do not just throw away, sell or donate your old phone immediately. First, check it for memory cards and delete any files you still have on it, then run the factory reset program to wipe it clean. Some identity thieves specialize in tracking down old phones and rooting through them to find a treasure trove of private information; do not allow yourself to become their next victim!
© 2015 CJMcAllister