Spotting, Dealing With, and Responding to Phishing Scams

Overview
Over the years, the prevalence of phishing scams have increased. Today, if you check an enterprise spam/junk email filter, you will find that 80% of the load is junk mail. Where I work, we get over 30,000 emails per day. Thus 80% of that is 24,000--all junk or phishing scam emails. That is a lot! And those were just the ones that were caught by the filter. Some do get through.
To help you or anyone you know deal with phishing scams, read the rest of this article. When you do, you will learn how to spot, deal with, and respond to these scams.
Background
What is a "phishing scam"? We need to answer this question before we get too far on this article; this way, we are on the same page on what it means.
When someone is "phishing" and trying to scam people on the Internet, their objective is to steal confidential information under false pretense. Confidential information could be one or more of the following:
- credit card numbers
- bank account or financial institution passwords
- other personal or financial data
On the Internet, anyone can pretend to be anybody or any organization. An unsuspecting total computer/Internet beginner (like grandma or grandpa) has no way of knowing any better, and as such can easily fall prey to a phishing scam.
The primary vehicle for delivering these scams is email.
Spotting Phishing Scams
Spotting a phishing scam does not require you to be technically adept. You just need to be armed with the information in this article and have some common sense. OK, I can't give you common sense, but I can give you two fundamental rules to help you spot these scams 100% of the time. Take note...here they are:
- If an email offer is too good to be true, it probably is.
- Any unsolicited email or electronic communication requesting you to sign in through a link or asking for confidential information is a phishing attempt.
Have you ever seen an email from someone claiming to be from Nigeria and having millions of US dollars needing to be transferred to an account? WARNING! WARNING!! This is an example of a phishing attempt. They want your financial account information so that they can siphon off money instead of deposit funds to it.
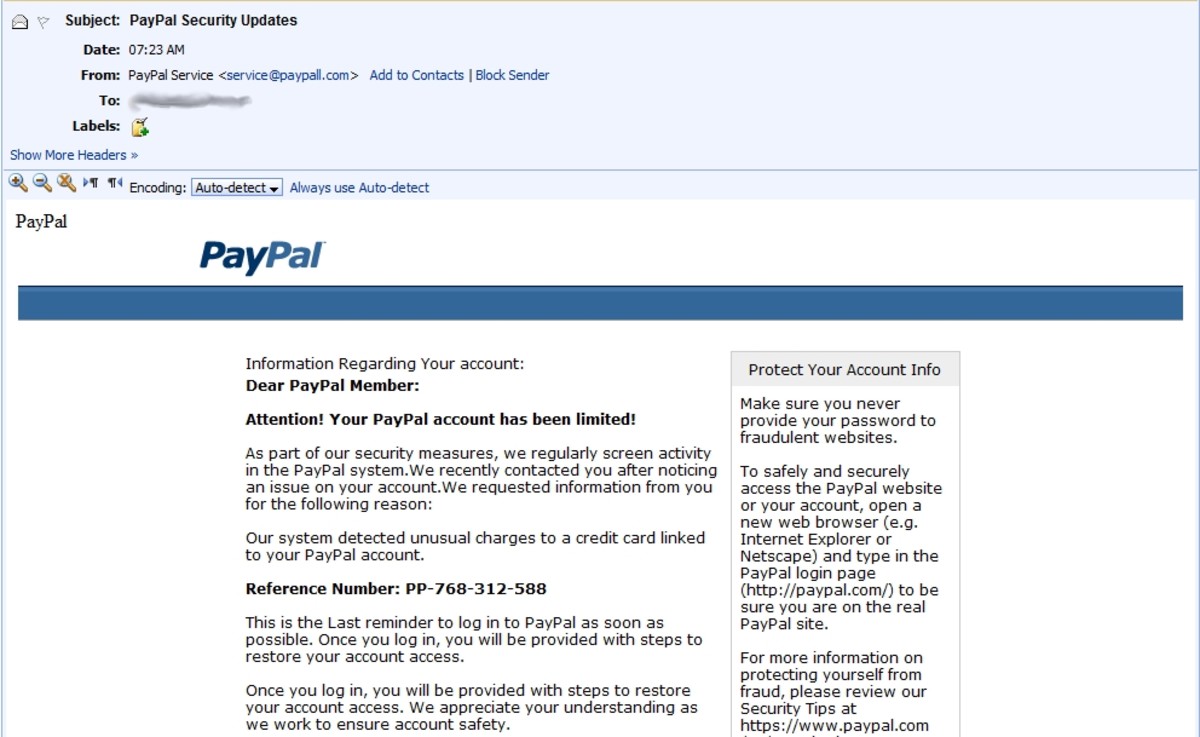
Ever seen an email from your bank stating that your account has been compromised and that you need to click a link in order to correct the problem? WARNING! WARNING!! This is also an example fo a phishing scam. In this scenario, the scammers have created a login facade that captures your bank credentials then forwards you to your bank. Don't fall for it.
OK. See if you can test yourself on some sample emails to see if you are able to apply the two fundamental rules for spotting phishing scams:
- You receive an email from a Mr. Jones who has inherited $25M USD. He happens to live in South Africa, and requests the use of your bank account in order to move his money out of the country. And for your generosity, he would give you $1M USD. Oh, how nice of him! What do you do?
- On the Internet, you do a lot of shopping using your PayPal account. Today you received a disturbing email from PayPal stating that your account has been breached. The email has conveniently provided a link where you can login and update you account information. What do you do?
- You get an email from B of A, your bank, stating that they have specials on auto loans with 0% APR. They ask you to visit their web site by clicking an image of the ad. What do you do?
If you decided all three are possible scams, you are right. Number three might be a slightly tough one, but if you wanted to check the validity of the offer, simply open a browser and enter the URL for the bank. That's it.
Dealing with Scams
There isn't much you can do to completely block junk email and scam email; however, you can take certain basic actions when dealing with them:
- Simply delete them.
- If you cannot delete them for some reason, just ignore them.
- By all means, do not respond to anyone of them. This just tells them your email address is a valid and active one.
What if You've Been Scammed Already
If for some reason you didn't get a chance to read this article before you got scammed, Then my condolences to you. Do not despair, because there are still things you can do if you've been scammed.
The Federal Trade Commission (FTC) has an article on How to Recover from an ID Theft. The provide a wealth of information on what actions you can take. One of the things you can quickly do is get ID protection from such companies like LifeLock.com or IdentityGuard.com. This will give you visibility into credit changes and credit applications under your name.
Summary
By this point, you should be very confident about being able to spot a phishing scam. And if you do see a scam, you know to immediately delete it. If for some unfortunate situation you end up getting scammed, all is not lost. Make sure to go to the FTC web site to get details of how you can recover from an identity theft.