Stop Internet Fraud, Online Scams, Identity Theft, Social Media Risks
Most people have an endless deluge of spam, scams, fraud attempts or hoax messages in their emails every day and on the websites they visit on the internet. It seems that despite all the antivirus tools you employ and the attempts by the browser provider to block the junk some always gets through. This mean that you have to have a way of recognising it and dealing with it.
The tricksters and internet criminals are becoming increasingly sophisticated with lots of new tricks and strategies to deceive you. Some are even masquerading as Virus detection tools or system error tools, system updates or Software Upgrades. Some are very good at generating the 'look and feel' of legitimate websites such as your online bank or PayPal.


How to Stop Becoming an Internet Scam Victim
80% of emails are spam and junk
The types of Scams and attacks are summarized in the table at the end of the article.
The key to prevention is to realise that most of these scams will mostly only work if you:
- Open the email (If it looks suspicious Don't Open It)
- Open an attachment (Never open any attachment unless you are absolutely sure it is safe and reliable)
- Click on a link (Don't click on any links unless you are absolutely sure it is safe and reliable) - One method of checking is to 'right-click' on the link and look at the address. If it looks suspicious delete the email.
- Click on an ad (Don't click on ads and stop the session if ads pop-up - You don't want to be there).
- Click on an 'Unsubscribe' link (Don't attempt to deal with the scammers - just exit)
Unfortunately some scams operate directly through the browsers, from emails, from software and websites, and so you need good quality anti-virus and anti-spyware software that is up to date and you need a good firewall.
Some of the major warning signs and things to avoid are:
- Content that requests any personal details - including name, phone number, address or bank account details. PayPal and your Bank will never request this information.
- A request for money - whether it's as a donation or to release more money to you.
- Promises and offers - if you are promised money, good luck, or a mobile phone, it's just a way to get you to pass it on.
- It looks wrong or odd - if you get a feeling that something doesn't look right, chances are it's not.
Major things you can do to prevent Internet Fraud:
- Use multiple email accounts and the free ones for transactions and contact that you suspect may be unreliable. If you must sign up for services, want to receive more info, register for newspapers or domains; use a free email address from a site like Yahoo or Hotmail to create an address especially for that purpose.
- Never click to open image in an email
- Keep your Virus and Spyware prevention software up-to-date
- Keep your Browser up to date. Both Internet Explorer and Firefox are the most targeted browsers because they are the most popular. Download security updates as soon as they become available as these contain the latest patches and you can surf safely.
- Get Adobe Updates such as Adobe Reader, for PDF files, and Adobe’s Flash Player as these programs have been hacked recently.
- Beware of Malicious Ads, especially pop-ups. Malvertising, as this practice is known, can exploit software vulnerabilities or dispatch deceptive pop-up messages.Beware of Virus Alerts - A particularly insidious scam involves an alert that a virus was found on the computer, followed by urgent messages to buy software to remove it. When you click the virus is installed!
- Beware of Fake Duplicated Internet Sites - You can often tell they are fake by the URL address, but the perpetrators are becoming are well versed in making fake sites and the URLs. When in doubt, type the web address of the trusted source.
- Poisoned Search Results - don't assume that results at the top of the page are reliable. Online criminals are good manipulate search engines into placing malicious sites toward the top.
- Antisocial Media - Attackers also use e-mail, instant messaging, blog comments and social networks like Facebook and Twitter to induce people to visit their sites. It’s best to accept “friend” requests only from people you know, and to guard your passwords.
- Never, ever reply to a spam message, this includes the offered "unsubscribe" link, which actually informs your spammer that you exist.
- Don’t click any links in emails that you are not absolutely sure are reliable.
- Disguise your email address and don't put it in plain text on your Web site or as a link. Strip out periods and "@" symbols, which will prevent crawlers from identifying it.
- Before joining a list, make sure the list owner or Web master will not sell your address or display it on their site and opt out of the offers of email updates.
- If your email software allows it Preview your messages before you open them.
- Use good anti-spam, anti-adware, and anti-spyware programs. Your Anti-virus software may not be very efficient in handling spyware.
- Never use your email address as your screen name in chat rooms. It will give spiders or human email harvesters an absolute yes to a questionable email address.
- *Install a good reliable firewall.
- Be sure you know who the seller is before you purchase goods on line.
- Never give any one details about your credit card over the phone or on forms. Always use PayPal, 2CheckOut etc., which are more secure and can debit you credit card without you giving someone the details.
- Be weary of businesses operating with free email addresses. Well developed and reliable customers will have their own domain name in their email address, and not a free one.
- Check your credit card statements meticulously and regularly.
- Always take your time making a decision and don't be rushed into a dodgy deal.
- Stay informed and educated about the most recent computer identity theft trends and methods.
- Exercise extreme caution when you download free software from the internet. Download it from trusted websites that operate a no-spyware policy.
- Be wary of ‘free’ programs that might be paid for by advertising.
- Be wary of ‘free’ programs that offer to install additional programs during the install process.
- Check the licences for programs you download from the internet to make sure that you aren’t giving permission for adware to be installed on your computer.
- Be careful about the websites you visit. Avoid tisky sites because these can also install spyware.
- Beware of so-called spyware removal programs many on these are traps.
-
Use anti-spyware software
How to Prevent Identity Theft
- Destroy private records and statements and other documents that contain private financial information.
- Secure your mail. Empty your mailbox quickly, lock it, or get a Post Office box so criminals don't have a chance to snatch credit card details.
- Never let your credit card out of your sight. Beware of credit card skimming? Always keep an eye on your card or, when that's not possible, pay with cash.
- Know who you're dealing with and check by ringing the company.
- Take your name off marketers hit lists and say no to telephone marketing.
- Be extremely defensive about giving out personal information such as drivers license numbers etc.
- Memorize important numbers – Never leave passwords and PIN numbers in places where others can find them (i.e. desk at work, tote bag, or wallet).
- Avoid Social Media Scams such as Chain Letters, Cash Grabs, Hidden Charges, Cash Offers, Fake links to personals pictures etc. which are Phishing Requests, Hidden URLs - beware of shortened URLs and fake URLs.
© janderson99-HubPages
Types of Threats and Scams
Type
| Action and Threat
|
|---|---|
Botnet
| A botnet is a network of compromised computers that have been compromised with malicious software also known as zombies. Botnets are lead to click fraud and denial of service attacks.
|
Browser Hijacking
| Malware that lurks in the web browser (e.g. Internet Explorer and Mozilla Firefox) and changes how and what a browser displays while a user is on the Web.
|
Click Fraud
| Click fraud is the act of producing clicks or impressions that are of no benefit to the advertiser. It uses other computers to inflate the number clicks on ads.
|
Counterfeit Payments Fraud
| Fake cheques; money orders; Paypal payments
|
Financial Fraud
| Includes a variety of scams: romance schemes; advanced fee scams; charities fraud; debt elimination; investment frauds; job scams; Nigerian Schemes; Ponzi and Pyrami schemes.
|
Hacking
| Hacking includes gaining illegal entry into a PC system to carry out illegal dealings exclusive of using his factual individuality.
|
Keystroke fraud
| This is where an unsuspecting computer user; usually at an Internet cafe; has all their keystrokes recorded by a stealth program.
|
Malware
| Is a form of hostile; intrusive; or annoying software or code that is generally transmitted online and includes: Adware -displays unwanted ads; Backdoor - method of bypassing standard authentication procedures to allow virus etc. in: Bot - performs automated tasks online such as click fraud; Rootkit - Programs designed to hide the presence of other forms of malware; Trojan horse - gives cyber-criminals unauthorized access to that computer; Virus - A computer program that infects a computer and self-replicates without the consent or knowledge of the computer�s owner.
|
Money Laundering
| Method of enticing "money mules;" who are used to funnel money and bypass international controls.
|
Online Advertising Fraud
| The scams seek to defraud advertisers by imbedding in computers and using them to generate fake ad clicks.
|
Pharmacy Fraud
| Masquerades as online drug supplier but doesn't deliver.
|
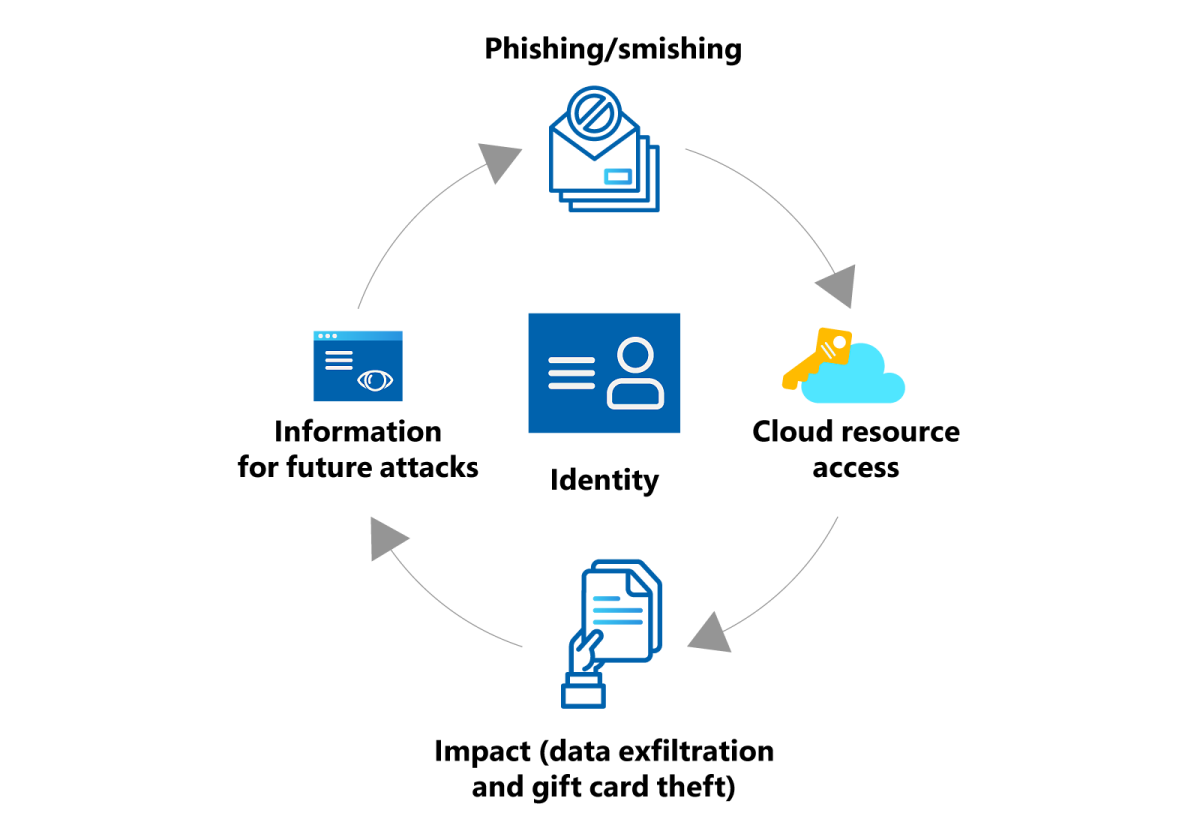
Phishing
| Uses spam or pop-up messages to deceive consumers into disclosing or 'updating' their card numbers; bank account information; social security numbers; passwords; or other personal information by masquerading as Internet service provider bank; online payment service; or even a government agency.
|
Pyramid Schemes
| Involves payment for recruiting new participants into the scheme while failing to deliver products or services.
|
Software Piracy
| Software piracy is the unauthorized copying or distribution of copyrighted software often with embedded malware.
|
Spam
| Refers to the sending of unsolicited bulk email. Spam email traffic is estimated to account for approximately 80 percent of all email traffic.
|
Spoofing
| Uses a false or shadow duplicate of a real website or email in a way that misleads the recipient. It redirects network traffic through the shadow page allowing the spoofer to acquire personal information; such as passwords; credit card numbers; and account numbers.
|
Spyware
| Spyware is software that collects personal information from your computer without your knowledge; including the monitoring of keystrokes to get your log in details. It can also redirect you to sites other than those you type into the address box of the browser
|
Sweepstakes and Lottery Fraud
| Offers of wins on lotteries that request your contact details
|
Virus and Worms
| A virus is a program that can cause minor to extreme damage to your computer and use your Internet connection to spread itself to other computers-usually those of your friends and family. A worm is similar to a virus; however; a worm is self-contained and does not need to be part of another program to circulate itself.
|
© 2010 Dr. John Anderson