Understanding Private IP Addresses and a lesson Spamhaus should learn
I recently had a customer who runs an internal mail server get blacklisted by Spamhaus.org.
That's usually because some internal machine has become infected and has managed to bypass all the defenses we put in and found a way to send spam email out. That's not easy, but they had apparently pulled a very ancient box out of the dust bin and hooked it up to the network. It must have done something exceedingly clever, because we block everything at the router except the mail server itself from using mail related ports, but nevertheless, the evidence was plain: Spamhaus had blocked their IP, so something had gotten out.
However, we didn't find this out immediately because I was a little careless when the customer informed me of the block. Because we had been through this before in the past, I told him to just type his mail server IP in at Spamhaus and that they would give him specifics. Once he knew what the actual problem was, he could ask them to unblock his address.
He called me back an hour later to tell me that Spamhaus said his IP was not blocked.
I was a bit surprised, but not totally. It is possible for this to happen. I really should have been more insistent right then, but, as I said, this customer had been through this type of thing previously, so I thought he knew what he was doing. I also foolishly assumed that Spamhaus had better software in place than they do.
The upshot of all this is that I arrived on site to examine the problem two days later. That's two days where the customer had to suffer annoying blocks. Here's what happened:
Private vs. Public
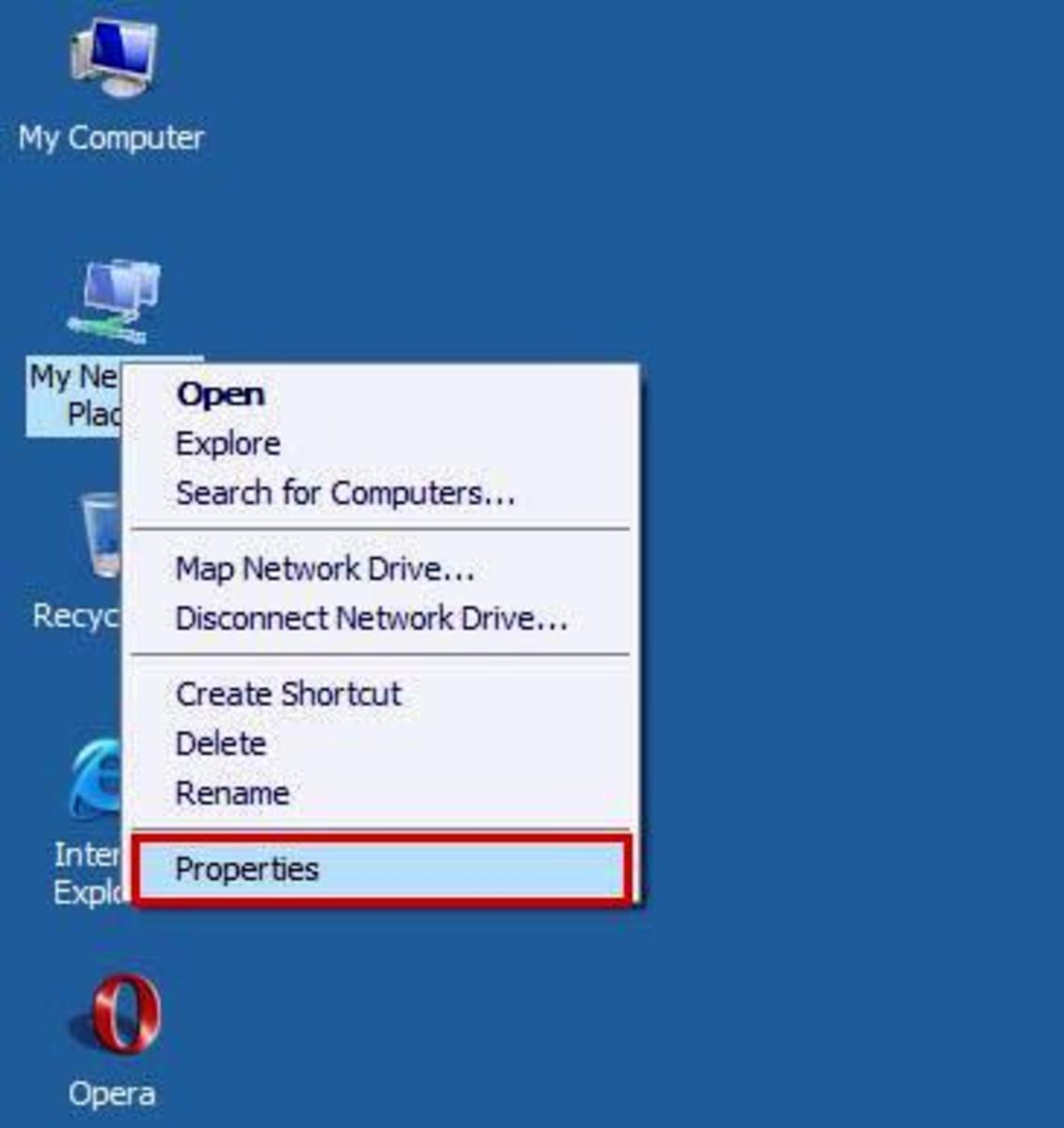
When my customer visited the Spamhaus Blocklist Removal Center, he typed in what he thought was his mailserver IP address: 192.168.2.120. That IS the address, but it is the internal, private IP address. What he should have put in is the public IP address - the address of the MX record for his domain.
We'll see in a minute that while it might be understandable that my customer made this mistake, Spamhaus never should have. Their website software should have known he had erred and should have told him that instantly. Let's see why I say that.
Here are the private IP ranges:
- 10.0.0.0 throuugh 10.255.255.255
- 172.16.0.0 through 172.31.255.255
- 192.168.0.0 through 192.168.255.255
You can't use the beginning or end of a range. That is, if you are planning to use 192.168.2 addresses, you cannot use 192.168.2.0 or 192.168.2.255 for a computer or printer. The first is reseved to refer to the network itself and the last is a subnet mask.
I don't want to get into subnetting here because it can get very confusing. If you are a home user or a small business, you are unlikely to need to worry about that.
Those are addresses you can use inside a private network. They cannot be used on the Internet - they will not route. Your Internet router has one or more true, public IP adresses that are not in these ranges and part of its function is to translate your internal addresses to public addresses. You'll here that commonly referred to as "NAT" or "masquerading" (purists will argue about precise meaning and say it's probably "DNAT" - they are right, but that's not important for most of us).
That's why I say that Spamhaus should have recognized the error. A mailserver can NOT have a public address of 192.168.2.120 - that is obviously an internal address.
Try This
Find out what your machines addresses are. First, go to WhatIsMyIP.com. That will show you your public IP address. Next, ask your computer what its IP is.
Here's how to tell with Windows: do Start->Run and then type "cmd" (on older systems type "command"). That opens up a "DOS box", or "command window" as we old geeks call it. In that box, type "ipconfig". You'll get back something like this:
Windows IP Configuration
Ethernet Adapter Local Area Connection:
Connection-specific DNS Suffix:
IP Address....................: 192.168.2.4
(and more, but it's the IP Address we want)
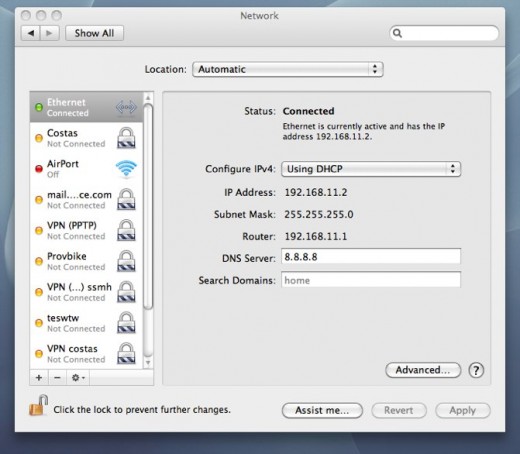
You may also know how to get that from the Windows interface. Similar information is available on Macs - you might open up Terminal and run "ifonfig en0" or use System Preferences to examine your settings.
Warning: If your computer network shows the same address as that WhatIsMyIP site, you are directly connected to the Internet and that is usually a very unsafe condition for a home computer.
What really happened
When I typed in his public IP, we got back confirmation from Spamhaus. Following the provided link gave us very specific information.
This IP is operating (or NATting for a computer that is operating) the "sendsafe" bulk emailing malware. This software is exclusively used for sending "Nigerian 419"/"advance fee" frauds or phishing attempts.
Sendsafe works by acquiring userid and password (usually stolen) for a valid email account on a mail server. Then, a machine compromised by sendsafe (in this case your IP) makes a SMTP connection to that mail server, authenticates with the compromised email login credentials, and proceeds to send Nigerian 419 scam emails.
One way to look for this is to look for authenticated outbound SMTP connections from this IP address either on port 25 or port 587. This particular detection was of a SMTP connection made from your IP address to IP address (removed for confidentiality).
In some cases it turns out to be a SSH login account (with a weak or compromised password) used to proxy inbound connections to outbound SMTP connections. Check your SSH logs for logins from unusual places (such as Nigeria).
A recent case turned out to be a copy of "Mass Sender" (aka "Advanced Mass Sender 4.3"). This appeared have been installed via some sort of remote desktop connection (such as RDT or VNC), and operated by the remote desktop connection. The criminal had gained access to the remote desktop connection via stolen/cracked/keylogged userid/password. First check Windows Installed applications (eg: Control Panel => Add or Remove programs...) and see if anything unexpected is there.
On a NAT, it could be any windows computer on your LAN. Examining your firewall logs for remote desk top connections from outside may help identify which computer it is.
In this case, it was "Mass Sender 4.3". If you find anything like that, delete it. Then, to make sure it doesn't happen again, secure your remote desktop connection as tightly as possible. Close the firewall to that port if possible. Change all passwords etc.
In other cases it appears to be a virus infection that may have disabled your Anti-Virus software. If you have Anti-Virus software, make sure it's operational and up-to-date.
That's very helpful. They also gave us the time the spam was last seen, which was five days back. My customer immediately remembered briefly putting up that ancient box on that day.
I remained concerned about how this box had bypassed our defenses. It should not have been able to send direct email out on those ports as those are blocked by the router for all machines except the actual mailserver. It might have used the internal mailserver (using credentials found on the machine), but I found nothing in the logs there.
Oh, well. I asked the customer to keep checking Spamhaus every week just in case the virus had managed to spread, but after six weeks, there has been nothing else, so I'm reasonably confident it has not. I also asked him to not resurrect five year old machines that should have gone to recycling long ago!
Do you know someone who should be reading this? Click the Share button below to send it to them easily or to post it to Facebook or Twitter.