Lean IT - How to Find the Waste in IT and Cut It
What is Lean IT?
The original seven types of waste are unnecessary transport, inventory, unnecessary motion, all types of delays, over production, excessive processing and any defects.
Lean is the concept of eliminating as much waste as possible. In a perfect world, business operations would have only muscle, no fat, only value added operations and activities. Waste in a manufacturing operation is identifiable as anything that is thrown away or reworked instead of being shipped out the door. The same waste-elimination ethos can be applied to management, office workflows and IT.
Unnecessary Transport in IT
Time spent walking to a server to check on its status instead of logging in and reviewing its performance online is unnecessary transport. Driving or flying to a site to perform software testing or hold meetings that could be done online are also unnecessary transport. Driving to a customer’s site for a problem that could be handled remotely is unnecessary transport.
Inventory in IT
Unused software licenses and hardware fall into this category. Parts sitting on a shelf that may eventually be used later are another type of waste.
Inventory can also include software project work in progress (WIP), code compilations in progress and files to be uploaded or updated. Any hardware or devices sitting in storage waiting to be assembled or configured are WIP and classified as inventory. Any personal computers or PDAs sitting on the shelf, not distributed to staff or otherwise in use are waste.

Unnecessary Motion in IT
One form of unnecessary motion is the unnecessary sending of files. This occurs when files are emailed to various users for approval instead of residing in a common repository where they can be accessed on demand. Carrying software disks back and forth and shipping servers when the software might reside on the cloud could fall into this category.
Waiting as Waste in IT
Users waste time when they are waiting for a computer to start, software to install or an application to load. Extra time spent waiting for approval to act on access requests and arbitrary wait times before action can be taken are forms of waste. Requiring system administrators stay in the office from 5 PM until 8 PM for the start of an official outage window without any work to do in the interim forces them to waste time waiting.
Another form of waste in IT is the wasted time someone spends waiting for a computer after starting with a company or waiting, unproductive, for technical support.
Overproduction in IT
More computers or servers are set up than actually required. Spending time to configure extra disk space or install memory that is not needed is also overproduction. Spending time performing tasks users could perform by themselves.
Installing software on machines that do not need it is a waste of time and money. Installing network cables that are underutilized. Running equipment and wasting electricity that is not needed is a form of overproduction.
Over-Processing in IT
The IT team spent time coding and testing enhancements that were cosmetic instead of functional improvements. Software enhancements were made when the user need had passed. Wasting time in redundant meetings rehashing requirements can be considered a form of waiting or a form of over-processing.
Generating unnecessary reports or sorting through excessive notification messages are types of over-processing. Over-processing can include adding features to software that are not part of the software’s original requirements.
Another form of over-processing in IT are the programmers and developers who waste time perfecting something that is good enough or refuctoring, making the code so complicated that you're the only one who understands it.
Defects in IT
The software fix put in place broke something else. The software release fails in a critical way and has to be rolled back. Software defects include deleting files uploaded by mistake, correcting metadata errors and finding missing files.
Another form of IT defect is when software does not meet the original software requirements and must be changed. Users installing the wrong software version and having to remove it can be considered a defect.

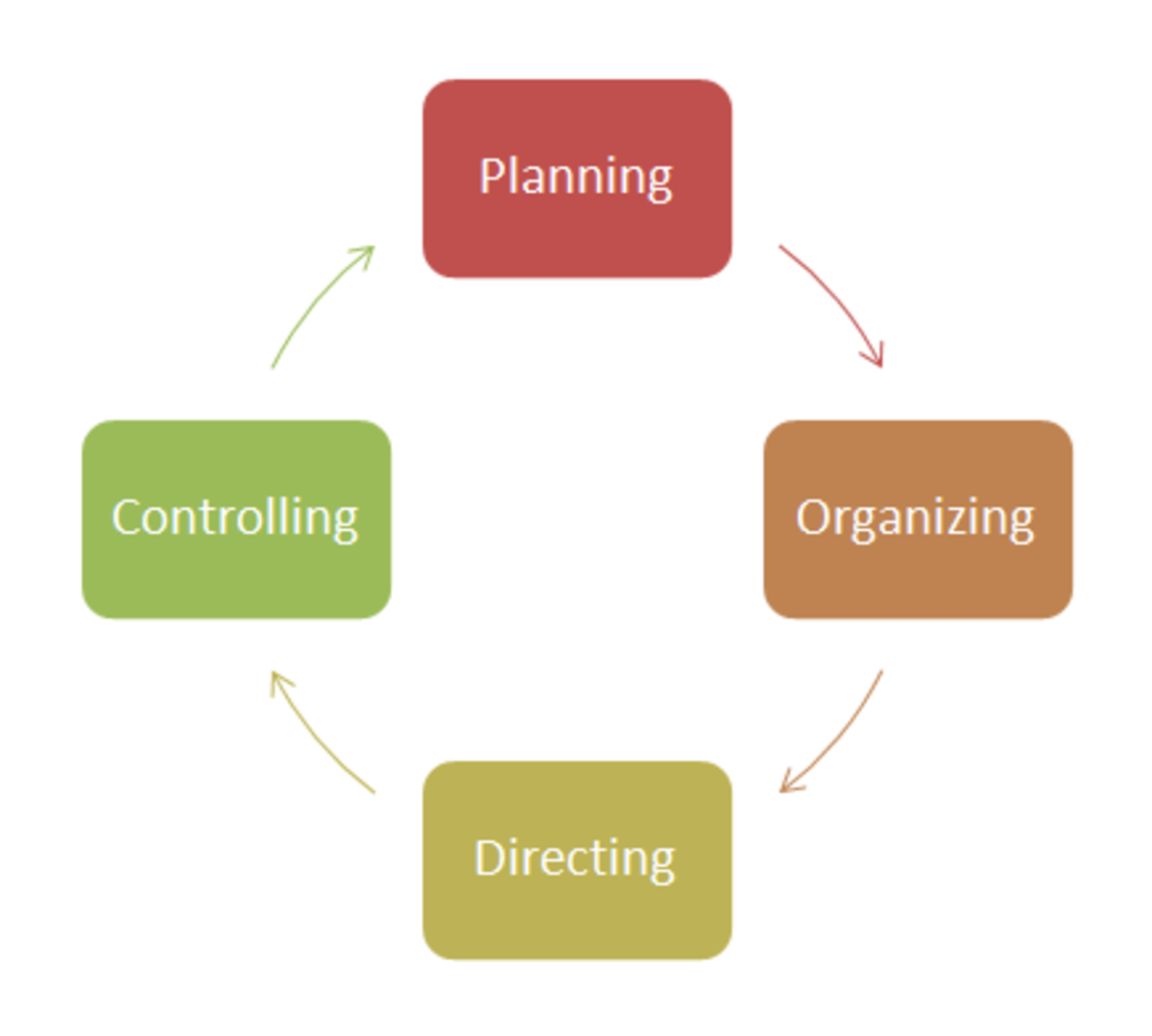
Implementing Lean IT
There are obvious forms of Lean IT, eliminating waste from an IT department. Replacing all servers and hardware with more energy efficient versions is one way. Aggressively consolidating servers and eliminating hardware is another.
Lean IT can be implemented in plain sight or in forms that are non-obvious to the user. Adding personnel so that user calls are answered quickly or cross-training staff so that reliance on a single expert is decreased can be considered Lean IT projects. However, there are less obvious ways of implementing Lean IT.
- Workflow exceptions can be handled in short, simple loops with human approvals and routings, instead of following a spaghetti-like routing based on a number of criteria and decision points.
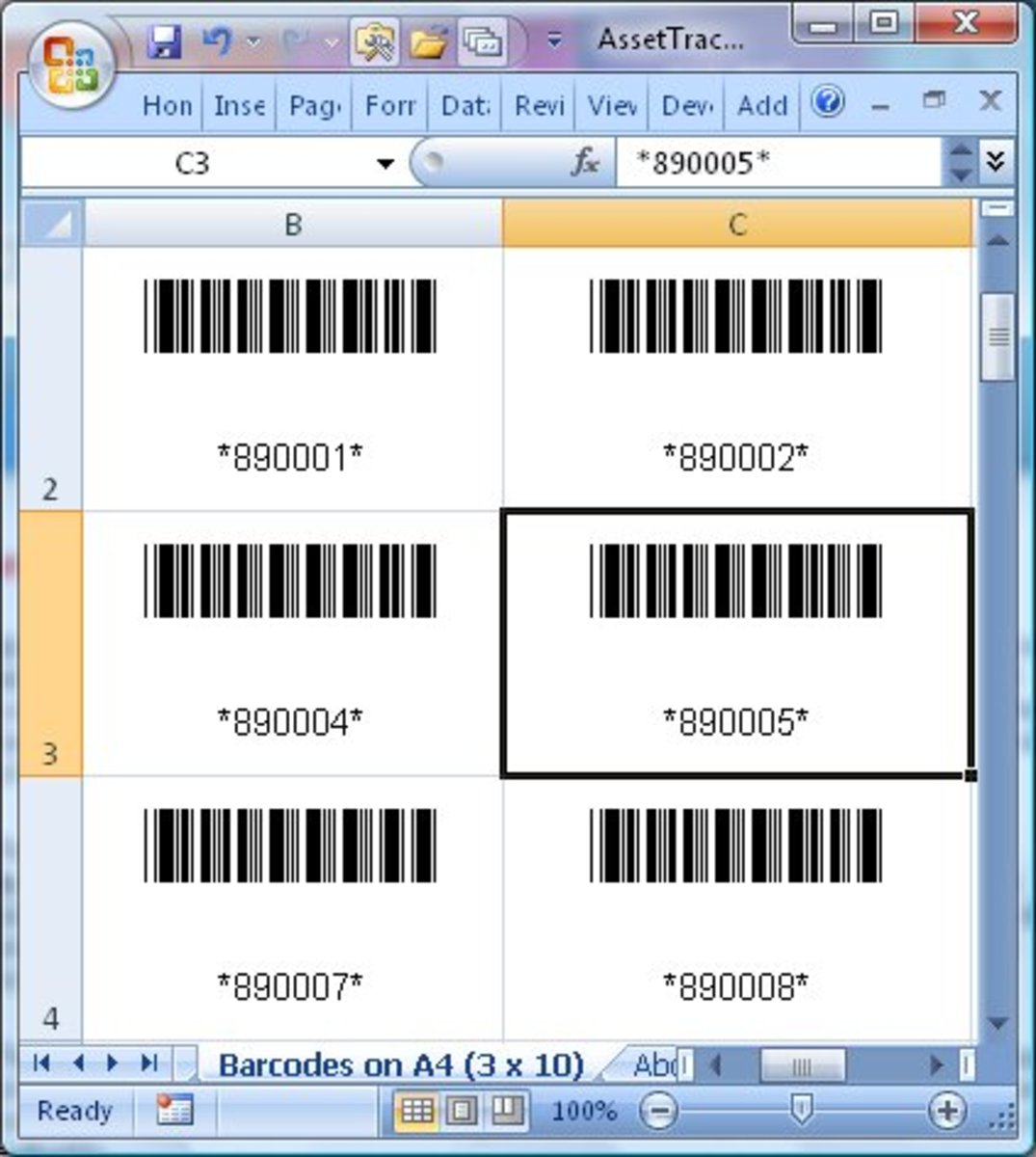
- Software installations could be set up as a matter of an installation request and then pushed silently to the user's machine per pre-determined criteria and/or a license manager's approval.
- Simplify and standardize help desk processes so that users have a single point of contact or method to request help, be it a phone number or web form. Users are then transferred to the correct subject matter expert or called back by someone with the skills to help.
- The use of virtual machines simplifies software upgrades. Only one software executable, the one on the server all application users share, needs to be upgraded.
- Devolution of authority to configuration managers or team managers for managing access for general employees simplifies the process of getting access and typically speeds it up. Using the local manager for this task takes the help desk out of this loop and prevents endless circling by IT staff trying to receive permission of the local manager to add permissions to an employee's account.
- Standard website designs and online forms improve a new employee's learning curve and IT's job in maintaining them.
- Setting a software tool baseline forces business leads to plan to abandon an old tool when selecting a new one for adoption. Maintaining a baseline number of software tools prevents their proliferation, making IT support more difficult while employees are forced to learn more tools to do the same job.
- Regularly scheduled maintenance windows make it easier to set software upgrades for dates that won't impact users, since they already expect an outage. Regular maintenance window also eliminate the hassle of trying to schedule outages for necessary patches with multiple stakeholders.
- Automate user computer backups to eliminate the need for users to initiate it. Using a standard software application to automate backups also simplifies IT support's monitoring of backups.