What is Software Security?
Software Security
Security means “The protection of the system against threats using both technical and administrative controls”.Security encompasses hardware, software, people and data. To effectively implement security requires appropriate controls, and these controls should implement specific policy statements that have been dictated by the requirements of the system, the needs of the organization and any legal constraints. We consider database security in relation to the following situation:
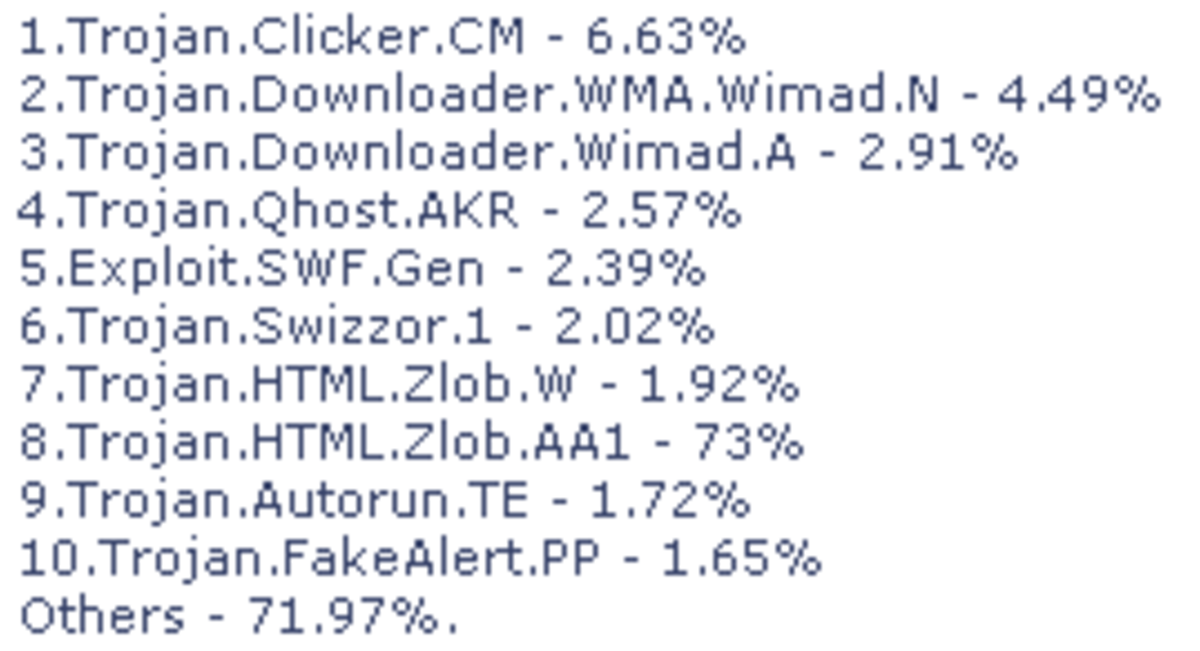
- Theft and fraud,
- Loss of confidentiality (secrecy),
- Loss of privacy,
- Loss of availability.
For security we need
1. Computer-Based Controls
2. Non-Computer-Based Controls
Computer-Based Controls
Computer-based controls those are available, in the operating system. We focus on computer-based security controls, with the assumption that we are dealing with a multi-user environment. Typically, not all of these controls will be available in the PC environment. We consider:
- Authorization
- Backing-up
- Encryption
Authorization
The granting of a right or privilege which enables a subject to legitimately have access to a system or object.
Backing-up
The process of periodically taking a copy of the database and journals (and possibly programs) onto offline storage media.
It is always advisable to have a backup copy of the database taken at regular intervals ad kept in secure location.
Encryption
The encoding of the data by a special algorithm those render the data unreadable by any program without the decryption key.
Non-Computer-Based Controls
The non-computer-based controls are mainly concerned with matters such as policies, agreements and other administrative controls, which are distinct from those that support the computer-based controls. These are:
- Establishment of a security policy and contingency plan,
- Personnel controls,
- secure positioning of equipment,
- secure data and software.
- Maintenance agreements,
- Physical access controls,
- Building controls,
- Emergency arrangements.