SharePoint: When Security Permissions are too strict, Microsoft SharePoint becomes HoardPoint (tm)

Although I watched SharePoint grow up from just an infant Document Repository, I didn't get my hands dirty until the late 2003, early 2007 version timeframe Having developed multiple Windows- and web-based applications, I was completely familiar with the need for security, and working with SharePoint was no different. Microsoft Access, up until the 2007 version, had a sophisticated User Level Security model that required understanding it and planning for implementation, long before the first table, form, or line of code was ever written. Unfortunately, it was never really secure, but it kept the honest people away from harm.
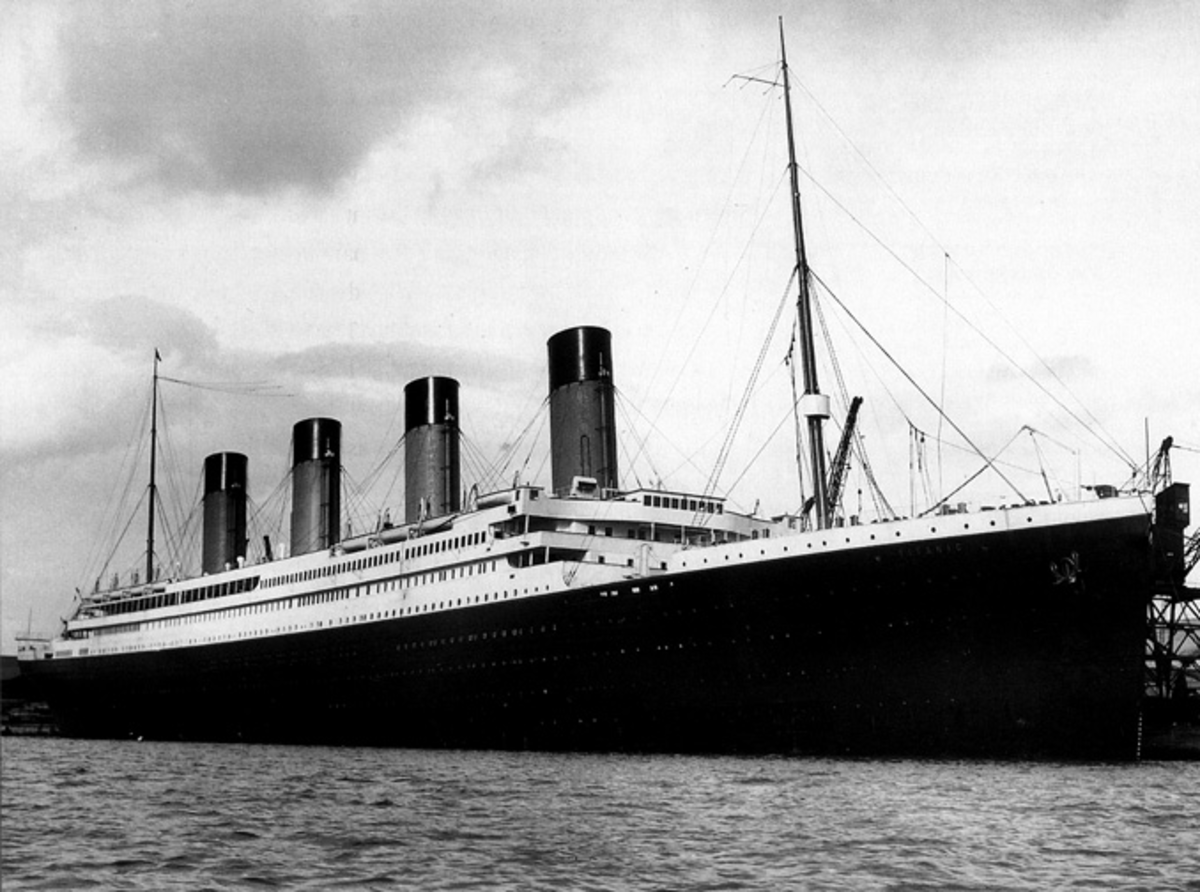
SharePoint Security is monolithic to say the least, but once you understand a little about it, then planning for it's use isn't so bad. I often refer to SharePoint as a cruise ship. Huge, beautiful, luxurious, feature-rich, and relatively safe. A passenger buys a ticket and viola, they're on the ship and crusing to their heart's content. They can wander from Isaac's Bar to Julie's Promenade Deck unaccosted and enjoying their stay. An employee is given a badge, and they may pass through the appropriate secret hallways and passages to complete their daily tasks and satisfying the needs of the passengers.
Most passengers understand that there is decorum on a ship, and opt to stay in the bar, the pool, the spa, or their room. Conversely, most employees want to remain that way, and follow the standard SOP of completing their duties. But, sometimes passengers or crew are nefarious, drunk, or just plain stupid. They sneak, stray, and/or wander from the known approved passenger/employee locations and find themselves trying to enter the engine room, the bridge, or Captain Stubing's cabin. (Although, he seemed to have plenty of *ahem* "guest visits".) It is these situations where security becomes a neccessary evil.
So, the ship in it's entirety becomes the maximum scope that all groups may reside. (Outside of that scope, they're in the drink or on the dock, right?) But, each person then needs special rights to visit the other areas. The passenger can't go into the kitchen or laundry, and the employee can't swim in the pool, and neither can go onto the bridge or into the engine room.
Stay with me on this a little longer... the passenger CAN enter their room, and CAN access the safe. They CAN program the lock code, and they CAN give that code to whoever they da... deem fit, but seldom is it anyone outside their close family/friend unit.
SharePoint is the same way, Active Directory(AD) allows someone to get onto the ship in the form of the ticket or the badge. From there, micro-security kicks in and AD and/or SharePoint groups can be used as the basis for assigning the masses to things like farms, site collections, sites, libraries, folders, and/or list items. Here's a very high-level SharePoint Security Architecture Overview. Designing a good SharePoint security scheme is fairly easy, when the idea is to... actually... SHARE the content. But, much like the cabin safe, there comes a time when sharing is just not a good thing. This is the beginning of what I call, HoardPoint (tm, R, C, all rights reserved... MINE!).
Whether you work for Lawyers, Doctors, or 3-Character Acryonym Government institutions, at somepoint SharePoint becomes HoardPoint. Accounting documents can't be seen by HR and vice versa. Dr X. can't see information about Dr Y's patients. Rocky can't see what Bullwinkle found out on a particular case until it's made public. Yadda x 3.
For these types of cases, Microsoft allows for Item-Level permissions, of which they now refer to as "Fine-grained", and then they basically tell you NOT to use it.
Best Practices for using fine-grained permissions
They don't say it in the doc, but if you snoop around, you'll find that 50,000 documents is the magic number, and after that, the performance drops of the FGP Cliff. But, there are solution examples within the document that discuss heroic efforts to solve very complex setups. Seriously though, before you even consider trying one of those... ask. Ask the client what they really need. Ask them what the true extent of their hoarding needs really is. Explain to them how SharePoint works, and see if there is a viable solution within the parameters of what SharePoint offers out-of-the-box. SharePoint can handle the creation of mulitple locations to store a document, you just need to interpret whether there should be another Farm, Site Collection, Site, Library, and/or folders to satisfy the need. Help them make an educated decision, and for goodness sakes, whatever the outcome, document it and make them sign it.
If they need something more than that, then maybe SharePoint isn't the right answer, they just need a different Cruise Ship. It's hard to imagine, but I find myself saying this to more people the longer I stay in the SharePoint game. "It's SHAREPoint! It's right in the name! Read it, listen to it, SHARE it!" (I wish Sam Kinison was alive to record this sound byte for me.)