The Anatomy of an Internet Scam
Have you ever received a message telling you than you’ve won thousands of kina and have to pay a certain fee to have it released? It sounds too good to be true – and it most certainly is!
The world of the internet has now opened up our doors to all sorts of scams and the format mentioned is a favourite among con artists trying to scam some money from poor unsuspecting individuals
Please Take the Poll before Reading Further
Have you ever been the victim of an internet scam?
Ali's Case
Unfortunately, a lot of people have become victims of these kinds of scams. Last year a 32 year old Dubai man, who we shall call Ali, lost US$500, 000 to three Nigerian conmen who contacted him via email and pretended to be the daughter-in-law of the late Libyan dictator, Muammar Gaddafi.
In their emails they told Ali that she (the daughter in law) had inherited millions from her husband who was killed in the Libyan revolution but the money was kept at the United Nations (UN) office in Egypt.
It went to say that she was hiding from rebels and needed a trustworthy person she could authorise to collect the money, and promised him 20% of the total sum. The man, however, needed further convincing and asked for some sort of proof that she was not lying.
The con artists replied with a scanned fake passport stating that she was married to one of the former dictator’s son. Ali fell into the trap like fly in honey.
In the effort to seem genuine and gather more information, the conmen asked him to send them a passport copy of himself to ensure that he was ‘sincere’ about helping her.
Ali then organized a trip to Egypt where he was met with a man he presumed to be from the UN who took him on a tour of their ‘office’ and then handed him two large briefcases. He was then advised to contact the ‘daughter-in-law’ to get the security access codes.
When he finally opened the suitcases, he found what appeared to be large amounts of US legal bills painted with black ink. There were two chemical containers next to them with a UN stamp and instructions to contact offices in London or Saudi Arabia.
When Ali contact the numbers provided, he was instructed to pay US$200, 000 to the office and they would help him mix the chemicals which would be used to dissolve the black in. He was also asked to pay another US$362, 000 to receive a certificate for the money.
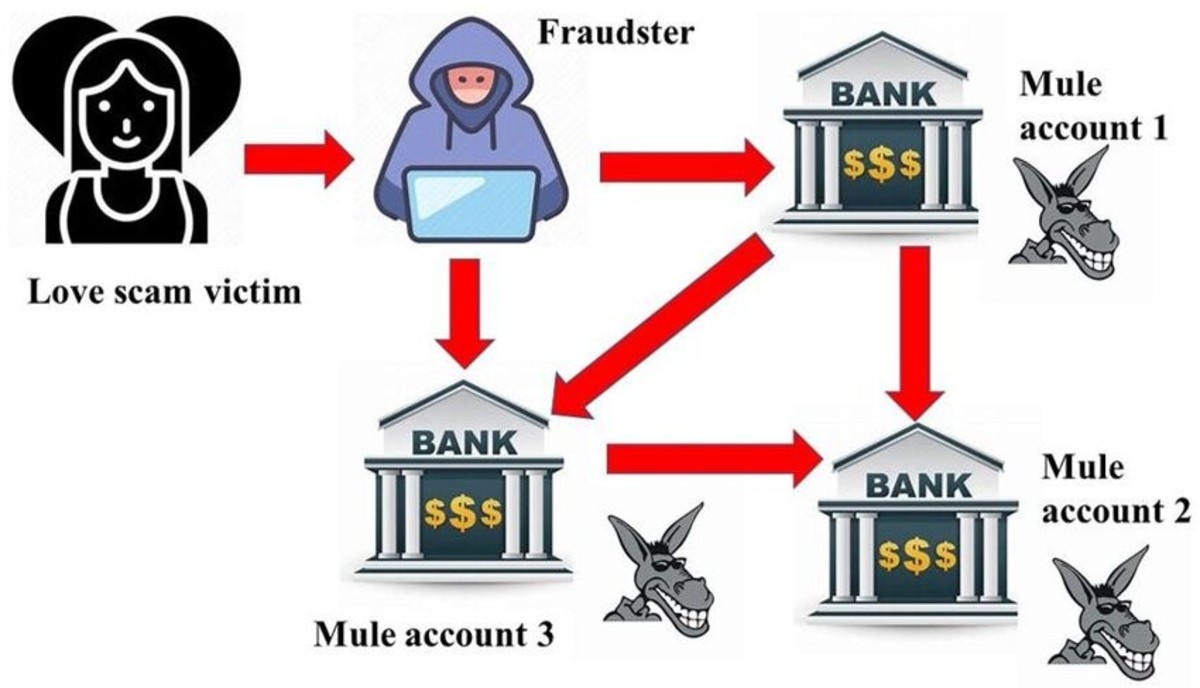
Ali paid both amounts between June and September, 2013, by electronically wiring the funds. However, he became suspicious when more money was asked of him and he contacted the local police.
The Dubai police then arranged a sting operation and nabbed two suspects. However, the third managed to get away.
Sadly, Ali’s case is one of so many all over the world. It is unfortunate that while the internet has made communication so much easier, it has also made it relatively easy and cheap for criminals to commit crimes. However, understanding how the scammers operate could give potential victims the knowledge needed to make sound judgement.
The Common Stages of a Scam
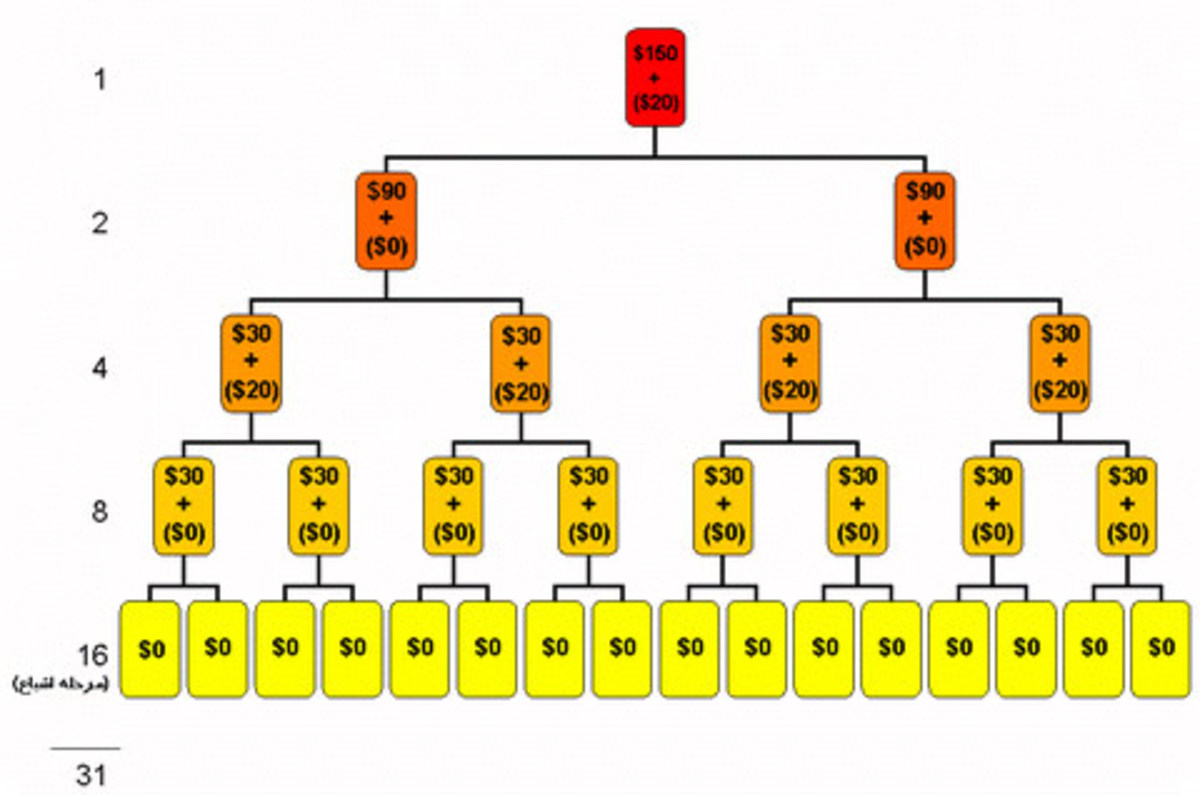
Scammers or con artists usually go through 4 common of stages, according to Hubpages writer kschang, to trap unwary victims; The Tease, The Please, The Seize and The Squeeze.
The Tease – the first stage involves some sort of attention grabber and usually includes a sad or complicated back story.
In Ali’s case they used the ‘maiden in distress’ tactic seeking help from a ‘knight in shining armour.’
The Please – the next stage includes ‘pleasing’ the mark by letting him or her know that they will be rewarded for their help. In most cases it involves monetary rewards. However, other forms of rewards have been recorded
This was the case when the ‘daughter-in-law’ offered Ali 20% of her million dollar inheritance. The promise of riches has always been a strong point of reference for scammers.
The Seize – this stage involves scammers putting potential victims at a point where they commit to the con. It also longest and probably most complicated stage of the process.
I believe this happened when Ali tried to verify if the ‘daughter-in-law’ was for real and asked for proof. It was a confirmation that he was buying into the con. They then reemphasized this when he flew out of his comfort zone and into Egypt.
The suitcase filled with what appeared to be US money was also a primer to get Ali to go all the way. The seize stage ended when he finally made payments to the scammers.
It is often at the stage that victims become wary of what is happening and usually stop communication with the scammers or contact and report the matter to local authorities.
The Squeeze – this is an optional stage but it’s when scammers become greedy and try to get more money from their victims as was the case with Ali.
The second payment he made of US$362, 000 was a squeeze. This is also the stage when most scammers are caught.
When Ali reported the matter to Dubai police, they encouraged him to keep in contact with the scammers knowing they would still try to squeeze him. It worked.
Triggers to Indicate a Scam
As scams come in myriad forms, it is best to keep in mind that there will always be something off with scam emails or messages. Here are some triggers that you should be on the lookout for:
- Unsolicited. If you receive unsolicited messages asking for some sort of help in return for large financial rewards then most likely it’s a scam.
- Informal contacts. I’ve noticed a number of scams that claim to be from Multinational Corporations but use free internet mail or the address is located in a country where the headquarters shouldn’t be.
- Personal information. Whenever an email comes asking for your personal information, red flags should go up. The commercial banks in PNG recently announced scammers were email their clients asking for personal details.
The banks explicitly noted that they would never ask for personal banking details. Why should they? They are already privy to that information.
Sources
- Four Common Stages of a Scam (internet or not) : tease, please, seize, squeeze, using mystery shoppi
Do you know the four stages of a scam? They are "tease", "please", "seize", and optionally "squeeze". Learn how they work on your risk, cost, and reward perception. - List of confidence tricks - Wikipedia, the free encyclopedia
- Nigerians con victim into paying more than $500,000 in email scam | The National
A man paid more than half a million dollars to three Nigerian men who claimed over email to be the daughter of Muammar Gaddafi. - How to Spot Scam Text Messages (SMS)
Some way you can tell if you have received scam text messages.
Who You Gonna Call? Scam Busters!
Now, if you ever receive a message that sounds a bit dodgy then forwarding it to the local authorities is the best thing to do.
If you are at the initial stages of the con then the best thing is to terminate all communication with the scammers. And if you partially swallowed the bait and already sent some money they keep in contact with the scammer and immediately contact local authorities.
I hope these tips help you be more aware of a con and please leave comment before you go.