What different types of malicious software resides in program memory

Malicious software or sometimes called malware is a type of software application that has been specifically written to launch an attack against an individual computer or a network. The purpose of this malicious software is to try to gain unauthorized access to the systems, and cause damage to the system or steal confidential information, or even financial information. Examples of code attack includes viruses, Trojan horses, worms, logic bombs, spyware, and adware.
Virus.
A virus is a self replicating program that copies itself into an executable file on the PC, and then spreads itself using the executable, when the user runs the program. They will have no idea that they have activated the virus if they don't have an upto date anti virus program. A computer virus is created for the main purpose of destroying data, or sometimes just causing a nuisance. If a virus is to work or infect a computer, it must first load itself into the system memory. When the host executable file is run, the virus code is also executed and destroys users data or critical system files. Sometimes they virus will wait until a specific time or date before properly activating itself. There are some variations of virus too.
Boot sector or bootstrap virus
This type of virus Infects the first sector of the hard disk. This part is used for booting or starting up the computer. The boot sector virus will start as soon as the computer is turned on.
Parasitic virus
This type of virus Infects executable files or applications on a PC. The infected files actually remains intact, but when the file is executed, the virus runs first. If the infected computer is connected to the network, the virus might have been written to travel from one computer to another and then infect every computer on its way. A virus can also infect data which is stored on a floppy disk, hard disks, or even on network storage devices.
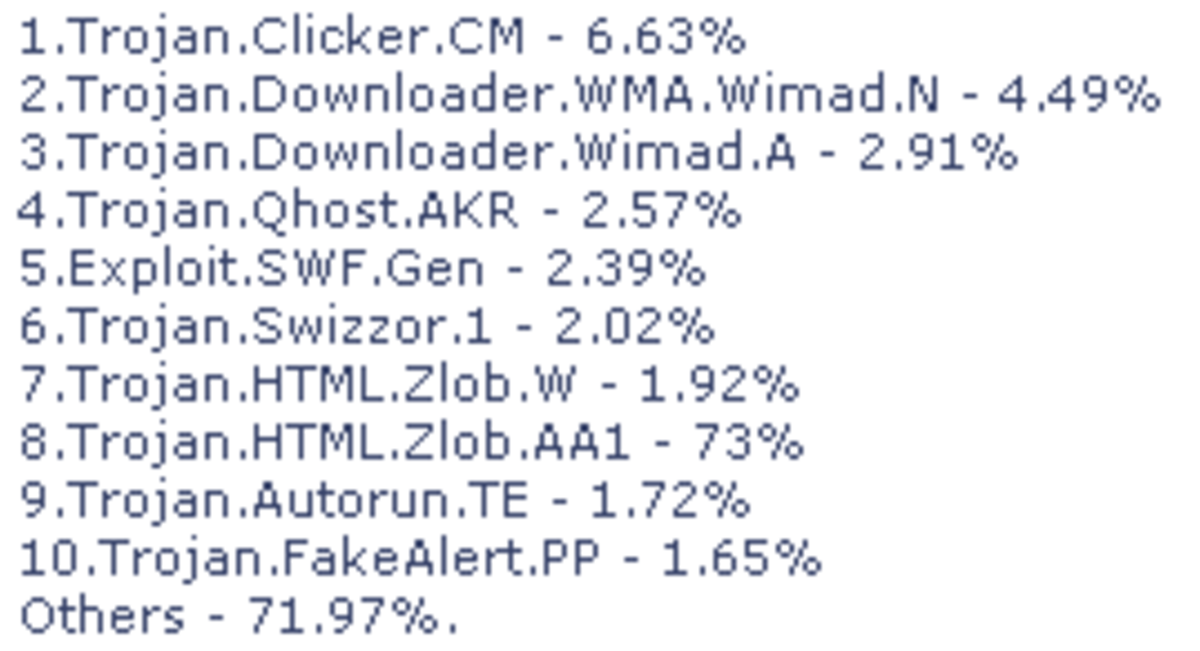
Trojans.
A Trojan horse, or sometimes just called a Trojan . A Trojan virus is a malicious code that is embedded inside an application. They are popularly hidden among keygen applications from torrents. The application will look useful or interesting and harmless until it is executed. Most of the Trojans contain code that is will gather information secretly about the user. These Trojans are often just called spyware, and appear as pop-up windows on a user’s computer screen. Some Trojan Virus are written to allow the user’s computer to be controlled remotely by the attacker, without the user even knowing this.
Worms.
A worm is a type of computer virus that does not infect executable or applications. Instead a worm will reside in the active memory of the PC. This type of virus usually keeps scanning the network or pc for vulnerabilities and then it will replicate itself onto other computers using the security holes that it finds. The effects of worm virus are difficult to spot, until the entire systems or network resources are consumed by the virus. The most common type of worm is an email worm virus that uses email addresses from your contact list to spread itself.
Spam.
Email spam, is quite simply junkmail that fills up your mail box everyday. These messages come from every corner of the globe, and are usually selling a particular health product. Spam emails come to you if a spammer gets hold of your email address and you will forever more, receive these unwanted updates. Spam is very well protected against if you are using one of the big email supplier companies. However occasionally the odd spam message can creep through into your main inbox. Spam is sometimes used to also help spread a number of the virus too, through the use of attachments.
Adware.
The term adware is used for software that will display adverts on your PC. Adware appears as a pop-up window normally on your computer screen. These adverts will appear when the computer is connected to the Internet, and will show up as a change of your homepage, or a new toolbar, or loads of pop up windows with offers. They are not always dangerous, more really annoying, however, if you have enough pop ups, your pc can crash.