- HubPages»
- Technology»
- Computers & Software»
- Computer How-Tos & Tutorials
How to remove Skypee virus (creates unnecessary shortcuts) on a computer
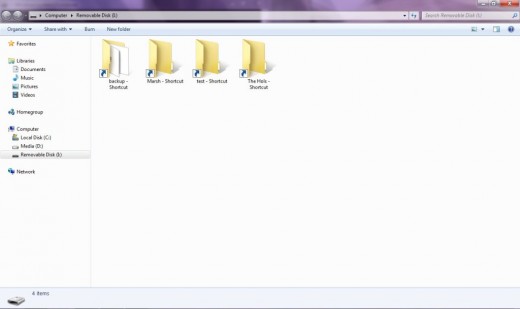
Skypee virus written in C, is a virus which affects your data on storage devices. It makes the data hidden, and replaces the data locations with the document shortcuts. Otherwise, as people claim, it fills your storage devices with shortcuts.
The virus is meant to disturb the user and make them uncomfortable using their computer. However, it has some effects on your computer, for example overrunning your CPU, by running in several instances on the background.
I have come across several computers with the problem, especially around institutions, cyber cafes, and other computer user hives.
Manifestation (form) of the virus.
- The virus, as I said is written in C, and takes the form of an application named “Skypee”.exe. A name which later has come to be changed into many, on many viruses taking the same form as the presiding.
- It manifests itself into ones storage device once the storage device is plugged into an infected computer. This is the reason why it replaces many files on your storage device.
- It is located on several locations on your computer, in order to do away with them you have to full scan your computer, preferably at startup.
When a user clicks on a shortcut created by the virus, it redirects to two locations, the application, and the data location. Therefore clicking on the shortcuts on several instances can cause your computer to be slow and freeze, probably even crash.This also allows it to spread across the computer making it hard for the user to remove it.
Spreading of the virus from one computer to another.
- The virus is spread though the users’ removable media.
It is highly volatile, as when the user inserts a removable media into an infected computer, the virus immediately integrates itself into the device and edits the data on it.
If the user runs the shortcuts on the removable media, the application integrates itself into their computer and writes on the hard disk partitions on his device every time they run the application.
If the user does not remove the application in time therefore, it could fill their computer with enormous number of shortcuts.

How to protect your computer from the virus.
There are two ways you can prevent your computer from the virus infection:
- Using smadav software.
- By not running the shortcuts.
Using smadav software.
- Download smadav software from the internet.
- Scan the affected disk and fix the problems found.
- Open the unnamed folder, that was hidden and run your files.
Smadav software is a software that deletes all .ink files and reverts all the hidden folders from hidden to non-hidden. Therefore, it deletes the virus from your storage device and shows all the hidden files. Making it possible for you to run your files without running the virus.
By not running the virus.
- Open your windows explorer, and press ALT key.
- Click on the tools bar, and select folder options.
- A new window should appear. Click on the view bar.
- Find and select the option to show hidden files.
- Now, insert the infected device on your computer, and open the hidden (faded) folder.
- You should be able to view your files on the location. Move the data from the device, and format your device.
If your computer is already infected with the virus, you should download Avast antivirus and boot scan your computer as a whole, the antivirus will find the antivirus and prompt you to delete the files infected.
Summary.
The virus is a very disturbing application, do not underestimate its damage on your computer.
To avoid such infections on your computer make sure you always scan your computer with a proper antivirus regularly and only trust proper antivirus software.
Also, do not go collecting, and downloading data from sources you are not fully familiar with.

![How to Remove Kaspersky Password Protection? [Easily Recover] How to Remove Kaspersky Password Protection? [Easily Recover]](https://images.saymedia-content.com/.image/t_share/MTc2Mjk3NDcwOTAzNTkyMTI2/how-to-remove-kaspersky-password-protected-easily-recover.png)