Essence of Network Security Devices to an Organization
Introduction
What does security mean? Security can be defined as a sort of freedom from dangers, fears, doubts, and anxieties. Why is it needed in businesses and organizations? Security is a crucial need for organizations to afford protection to information that is considered vital, bring control of who can access what resources and ensure that resources availability is guaranteed to the organization. Resources that could be attacked in business organizations include online services, secret ingredients, customer information, research information, employee information and login credentials among others.
Threats in networks
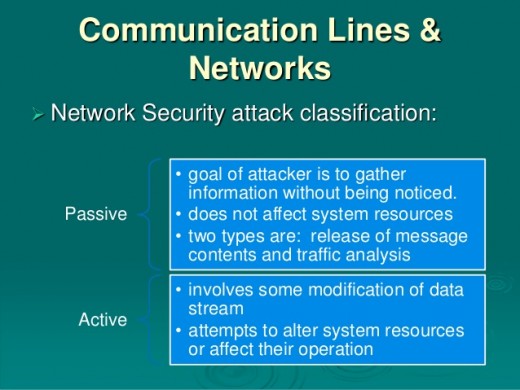
In networks, the threats that face it are theft of information, manipulation/fabrication of information, loss of data and service disruptions. Attacks could come from outside the organization or from the insiders. Common types of attacks prevalent in an organization include interception of data in transit, access to data or software in hosts by intruders, modification of data or software by intruders, running harmful or malicious software in hosts, exploitation of bugs in software, denial or disruption of services, hijacking TCP, sniffing of packets and user related problems such as lack of awareness to threats and weaknesses they introduce to security measures in place.
With advancements in technology each dawn, these attacks have been made more severe, sophisticated and difficult to protect against. These attacks once orchestrated in organizations could leave it on its knees since they leave nothing but catastrophic damages and losses. Damages could come in ways of monetary loss, human life loss, soiling an organization’s reputation and legal consequences. Organizations can, however, secure themselves from these attacks. They can do this by investing in devices made to thwart these attacks by protecting all avenues used by attackers. No given organization is immune from attacks and therefore these devices are as necessary to them as basic needs to humans.
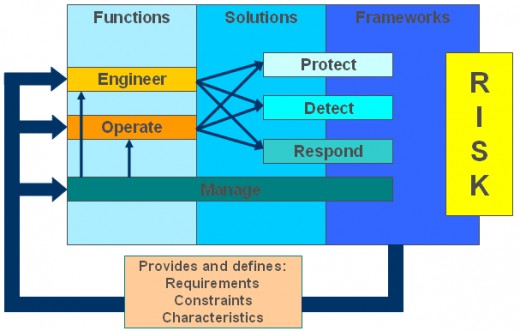
Best practises: Security program
Operating at the application layer of the firewall, proxy firewalls address use a more advanced technique of acting as an intermediary. They impersonate the recipient’s address thus receiving all traffic intended for the destination. They then inspect the traffic and decide whether to reject or grant access. If granted, the information is sent to the destination, and the reply from the destination is sent to the firewall which repackages it with it address before sending it. However, inspecting all the traffic degrades the firewall’s performance and also face scalability issues since each application requires its proxy(SearchSecurity).
Another technique used by firewalls is that of stateful inspection of packets. It involves classification of traffic by checking the port it is destined for and then tracking the traffic state in for every single interaction of a particular open connection. This technique ensures that all incoming traffic is a reply to a legitimate request made by the internal hosts. It is so effective that it can foil a denial of service attack. However, stateful inspection adds an extra layer of protection which introduces complications to the infrastructure of network security.
Next-generation firewalls have been created to respond to the rise of sophisticated applications and malware. Integrating port evasion techniques in their programs, developers of malware have been able to beat stateful inspection of their packets because it is port based. Next-generation firewalls have been developed to provide all-rounded protection. They have the capabilities used by first generation firewalls such as packet filtering or stateful filtering. They also have inbuilt integrated intrusion protection mechanisms. They can also use intelligence outside the firewall from external sources to make better decisions. They can also adapt to the rise in new threats by supporting upgrades to their knowledge base of techniques to beat threat. They are also in a way such that they do not cause service degradation (Palo Alto Networks). All in all, these features all support the fact that firewalls are essential to any organization and with their capabilities a huge burden of security of the internal organizational network is addressed.
Common attacks warranting the need for security devices
a. Attackers finding way into the organization’s network
The use of internet brings unadvertised threats to an organization. Using outgoing and incoming traffic from the internet, attackers can do lots of harmful things. First, they can retrieve what is being transmitted. Secondly, they can manipulate information in transit, they can also fabricate their information and send it instead of the real information, and they can also terminate communications between two parties. All the mentioned can be done if the network being used is unsecured. This had been a major concern for the organization before the invention of hardware and software that could be used to curb all of these threats, firewalls.
Firewalls are used to filter traffic flow between the organizations secured intranet and the internet. The intranet is the trusted and secured network in an organization, and the Internet is the global interconnection of networks, and it is entrusted and unsecured (Barbie). Firewalls protect users in an organization from external threats. This is by limiting or inhibiting their computers from external access while at the same time permitting secured communication with the outside world. All traffic must pass through the firewall whereby using several techniques; it decides on which traffic to allow and which one to reject.
Firewalls use several techniques to enable them to decide on what to accept and which one to reject. One of the early ways it used this is by using access control lists. Access control lists are rules that read the headers of packets to read the IP addresses and find out whether that IP address is in the list of the trusted ones, if not, that packet is automatically rejected. The merits of ACLs is in their scalable nature to quickly add and remove IP addresses and their high-speed performance. They can however not read more than the information in the headers of packets and therefore solely not completely secure since the technology exists to forge packet header information to appear as from a trusted source.
Another firewall technique is the use of application filtering or website filtering. It is a simple technique which grants or rejects access based on the particular website or application being requested or sending replies. In its knowledge base, the firewall sets rules to allow traffic only from given URL addresses that are trusted. All other traffic is rejected.
b. Intrusion into systems
Using viruses, worms, and hacking techniques, attackers can force their way into a system. Examples of ways attackers could intrude systems include scanning of ports, indexing of web servers, fingerprinting the OS, using ping sweeps and attempts of denial of service. Administrators needed some sort of a system to prevent successful intrusions into systems. Software and hardware counter measures were developed to bring an end to this. These counter measures were Intrusion Detection Systems (IDSs) and Intrusion Protection Systems (IPSs).
IDSs are tools that are developed to monitor, detect and warn about activities in a network that are considered suspicious (Webopedia.com). Intrusion detection systems only identify whether there are attempts being done to break into a system and then warn about such suspicious activity. They do not stop the attack from happening; they are therefore useful if corresponding counter measures are in place to the attacks they detect. By reviewing data about network traffic, IDS identifies attacks, exploits probes among other vulnerabilities. IDS use intrusion signatures, these are known characteristics or behavior patterns of viruses, malware or hackers. IDSs can be installed at different points in a network as application software or hardware appliances/devices.
Intrusion detection systems (IDS) can be categorized into different ways. They include the following:
• Anomaly detection and misuse detection: Under misuse detection, the IDS gathers information and analyzes it compared to a database containing multiple signatures. Under anomaly detection, administrators define a normal state of the network and use it as a base to identify anomalies
• Reactive and Passive systems: The IDS just detects, writes in a log and gives an alert in passive systems while in reactive systems, it goes on to react to the detection by adding to the firewall rules to reject traffic from that given source.
• Host-based and network-based IDS: Host-based IDSs are mainly software in host computers to monitor and stop malware installation attempts and even monitor administrator activities such as changing system files. Network-based IDSs are mostly hardware appliances installed at several points of a network to analyze traffic in a network.
It is worth noting that IDSs are not the same as firewalls neither can they serve as their replacements in the organizations. This is because firewalls not only look for intrusions but they effectively stop them using various techniques. On the other side, the primary goal of IDSs is to detect and warn about intrusions. However, there do exist intrusion prevention systems that stand up to the challenge of stopping intrusions. Intrusion Prevention Systems follow up IDS notification that there is an intrusion with attempts to stop that threat. IPSs can also automatically prevent well-known signatures of intrusion and also unknown attacks using its database of generic behaviors of attacks.
Intrusion Detection Systems and Intrusion Prevention Systems are essential to every organization because they stop threats of buffer overflows, software bugs among others that are employed by attackers. They can be set up as software and as hardware devices in the organizations network.Their value is not substitutable and needs to be present to always tirelessly be on the lookout for an intrusion.
The last DoS technique is a smurf attack. This technique employs the use of an IP ping, which is a request by a host to the receiver echo back the message to the source host. Attackers can forge a source IP address and broadcast a ping request. As expected, all the machines in that network reply to the victim. The high number of replies overloads the victim, the real holder of the IP address.
DoS attacks are particularly very dangerous as they can potentially put out a system for good, that is, permanently. However, lucky enough for organizations there are techniques used to thwart these attacks. One of them is by use of ingress filtering. The source IP of a packet is inspected ad if it arrives on an interface that lacks a route to the packet, the packet is dropped. This is effective in preventing smurf attacks and teardrop attacks. To prevent against SYN flooding, SYN cookies are now used in the OS of the server or in a device at the edge of the network. An example of such a device is a Cisco Guard. They keep track of the incoming TCP connections reducing chances of SYN floods. Also, there is the use of reverse proxies which crushes incoming traffic into fractions thus reducing the chances of the network being overwhelmed (Weiss). The final strategy is that of deploying firewalls that monitor the incoming and outgoing traffic thus preventing attempts to flood the network by use of illegitimate traffic.
c. Denial of Service (DoS) attacks
In denial of service attacks, the attackers disrupt or inhibit traffic flow in a given system. This deprives systems the services they ought to receive or offer. When this is extended to several systems being used to hit sole targets, it is referred to as distributed denial of service. This type of an attack targets servers, users, routers and network links among others. DoS attacks cause a temporary or permanent cease of operations.
DoS attacks can be carried out using different techniques. First, attackers can use buffer overflow. They send traffic to a destination address more than what the data buffers was designed to handle. This immense quantity of traffic overpowers the buffer capabilities thus causing it to crash.
Another technique is by use of SYN flooding. During the initiation of a session between the server and a client in a network, several session establishing packets are sent with an SYN field used to identify the sequence used in a message. Attackers can send numerous connection requests within a short time and fail to reply with ACK (acknowledgment), this leaves a half-open connection. After a reasonable amount of time, that connection is dropped. However, using the power of multiples, attackers prevent the legitimate connection requests from being processed and sessions being established.
Another DoS attack technique is teardrop attack. The size of frames used to transport packets in different network media varies, for example between Ethernet and Wi-Fi. When a frame is too big to be transmitted to the next router, it is broken down into fragments which are assembled at the destination. Attackers being aware of the fragmentation process know that the fragment packet has an offset at the beginning of the first packet to aid the reassembling process. They, therefore, insert a confusing offset value in fragments following the first one, and since the receiving system is not planned to handle these, it can crash.
d. Packet Sniffing
To send a packet to a destination using Ethernet, one includes in the wire the MAC address of the destination so that all other hosts in the network ignore the packet. Other is actively listening for collisions of packets they have sent on the same wire. A packet sniffer listens with different intentions of monitoring the traffic that is being transmitted over the network. Information transmitted in clear text is easily viewable. Usernames and passwords can easily be retrieved by the intruder. Packet sniffers could capture sensitive information about the organization also such as its secrets and researches. In the wrong hands, this information could be used to bring down the organization.
To the salvation of the organization is encryption. Encryptions transform plain text into a coded cipher format. It becomes unable for anyone else to make sense of this data unless being the holder of a key that is used to decrypt the text. Another way is by using IPsec that can provide confidentiality at the network layer.
Conclusion
In conclusion, numerous threats face an organization, and it is every organization’s nightmare to be attacked and have to deal with the consequences of not securing its network. Fortunately, hardware and software solutions have been developed to reduce the chances of this from ever happening. Organizations must, therefore, ensure they have these network security devices and mechanisms enabled on their networks.