The Internet is Really Really Unfair
The Internet is Really Really Unfair
Some people manage to extract a comfortable living from the Internet. Like Joe, they discover deeply buried online secrets to leverage their experience into cars and bling.
That really really rocks.
For everyone else, the Internet is unfair. Possibly the biggest unfairness is the loss of identity suffered by individuals with common names. Those of us unfortunate enough to be saddled with monikers such as "Stan" or "Bob" or "Tiger" often find ourselves digging for available online names. Our given names have been long since gobbled up by computer geeks who anticipated future trends. Unless you got in on the ground floor, finding a user name can be problematic.
The Internet is really unfair
In the interest of science and making this article longer, we contrived an experiment. Imagine a newly indoctrinated Internet user who desperately desires a gmail account. Gmail is the free electronic mail service offered by Google. Google is king of the world. Email is ... well ... you should already know that much.
Imagine that our prototypical Internet user is called John Smith. John has a comfortable identity in the real world; his friends call him "John". The credit card companies call him "Mr. Smith". He survived the trauma of Junior High School, where he was referred to as "Toilet Smith" or "Flushy" or "Porta-Potty." He passed through the crucible of the playground, arriving at adulthood secure in his name.
Earnest John surfs to www.gmail.com and begins the process of creating the email account of his dreams. His first decision requires him to compose his email address. Given that he has spent his life knowing himself as John Smith, he innocently enters an appropriate login name:
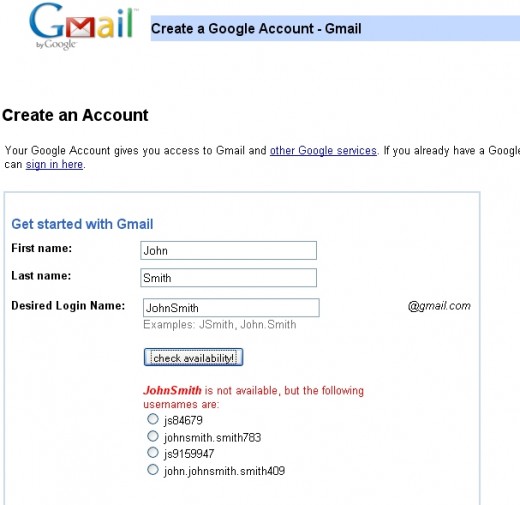
To his everlasting horror, erstwhile Mr. Smith learns that for eternity he may no longer identify himself as John Smith. Google politely proffers several new identities:
- js84679
- johnsmith.smith783
- js9159947
- john.johnsmith.smith409
Our hero John recoils in horror. His identity has been folded, spindled, and mutilated into lexicographic concoctions recognizable only by other computers. In order to join the Internet revolution, John must reinvent himself into something unpronounceable.
What's truly disturbing is the consideration that a Google employee was paid to write the software that composed these suggestions. For a corporation with a corporate motto of "Don't be evil", they might provide better name-composing support. Unfortunate John Smith finds himself burdened with the onerous task of concocting an email address that will follow him for the rest of his life. Ever the good soldier, John takes a crack at a new name:
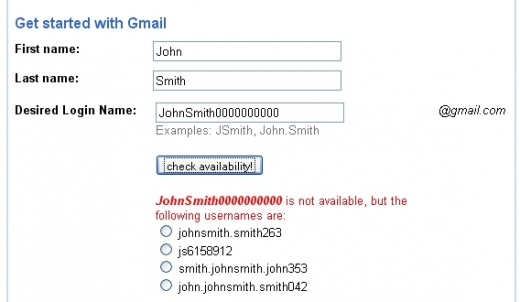
Crikey! JohnSmith0000000000@gmail.com has already been registered. How many John Smiths are out there?
Feeling himself regressing to his painful childhood, our John Smith steels himself and tries one more possible login name:

John is now faced with good news and bad news. On one hand he has found an available email address. On the other hand he faces another lifetime of teasing and long-suppressed playground flashbacks. On the third hand (this is a thought experiment) he will spend hours explaining his new email address to friends and family. Whatever ID he chooses will become his online persona until we all get wireless devices implanted in our foreheads.
Conclusion
We conclude that we are stuck with a really really unfair Internet. Perhaps the government can do something about it. A Department of Homeland Identity could be legislated into existence. Cubicles populated by well-meaning bureaucrats would toil endlessly to bring fairness to email address assignment.
It could happen.