AUDITING THE INTERNAL CONTROLS; AN AUDITOR’S EVALUATION TOOL FOR DETERMINING DETECTION RISK
AUDITING THE INTERNAL CONTROLS; AN AUDITOR’S EVALUATION TOOL FOR DETERMINING DETECTION RISK
Auditing the internal controls is a well reasoned out evaluation carried out on internal control to ensure that audit risk (inherent risk, detection risk and control risk) are reasonably within acceptable range. Audit risk is the probability that an incorrect opinion will be given by the auditor (e.g. giving an unqualified opinion when a qualified opinion should in fact be given).
AUDIT RISKS AND SOLUTION
Control risk is the probability that a company’s internal controls will fail to prevent or detect misstatements that can either be caused by error or fraud. Inherent risks are those risks that are associated with the industry of the business. Detection risk is the chances or probability that audit procedures will fail to detect material misstatements that have entered the accounting system at the time of audit. This misstatement must be material in for it to justify the resources inverted in this evaluation. To assess control risk, an auditor must have sufficient knowledge and understanding of an entity, its environment and its internal control.
AUDIT RISK EQUATION
The simple equation for representing audit risk is; AR= IR x CR x DR. Inherent risk and control risk are outside the control of auditors. So, more effort is put into fixing an acceptable detection risk level and working towards reducing it. For example, if an auditor decides to set AR 0.05, and it was determined that IR is 0.90 and CR is 0.5, then, the auditor will have to determine DR thus;
AR= IR x CR x DR
0.05 = 0.90 x 0.50 x DR
Solving for DR will give: 0.1111 (rounding up we have 0.11)
Note however that DR is not the level of detection risk but the maximum level of risk that the auditor can tolerate. It can actually be reduced further by auditing more items in the financial statements.
It is the objective of every auditor to have audit risk that is as low as possible. Since it is the responsibility of management to establish and run a functional internal control, the duty of the auditor is to perform tasks that will help him or her place weight on the effectiveness of the internal control. And that is the objective of this article. Tips on how to evaluate internal controls of companies so as to be in a better position to place informed values on IR (Inherent risk) and CR (Control Risk) will be examined in this article. So, sit back and enjoy!
EVALUATION OF INTERNAL CONTROLS
The approach I will take in this article is to list the five components of every good internal control as provided by COSO (The Committee of Sponsoring Organizations of the Trade-way Commission, 1992) and provide easy way of evaluating them.
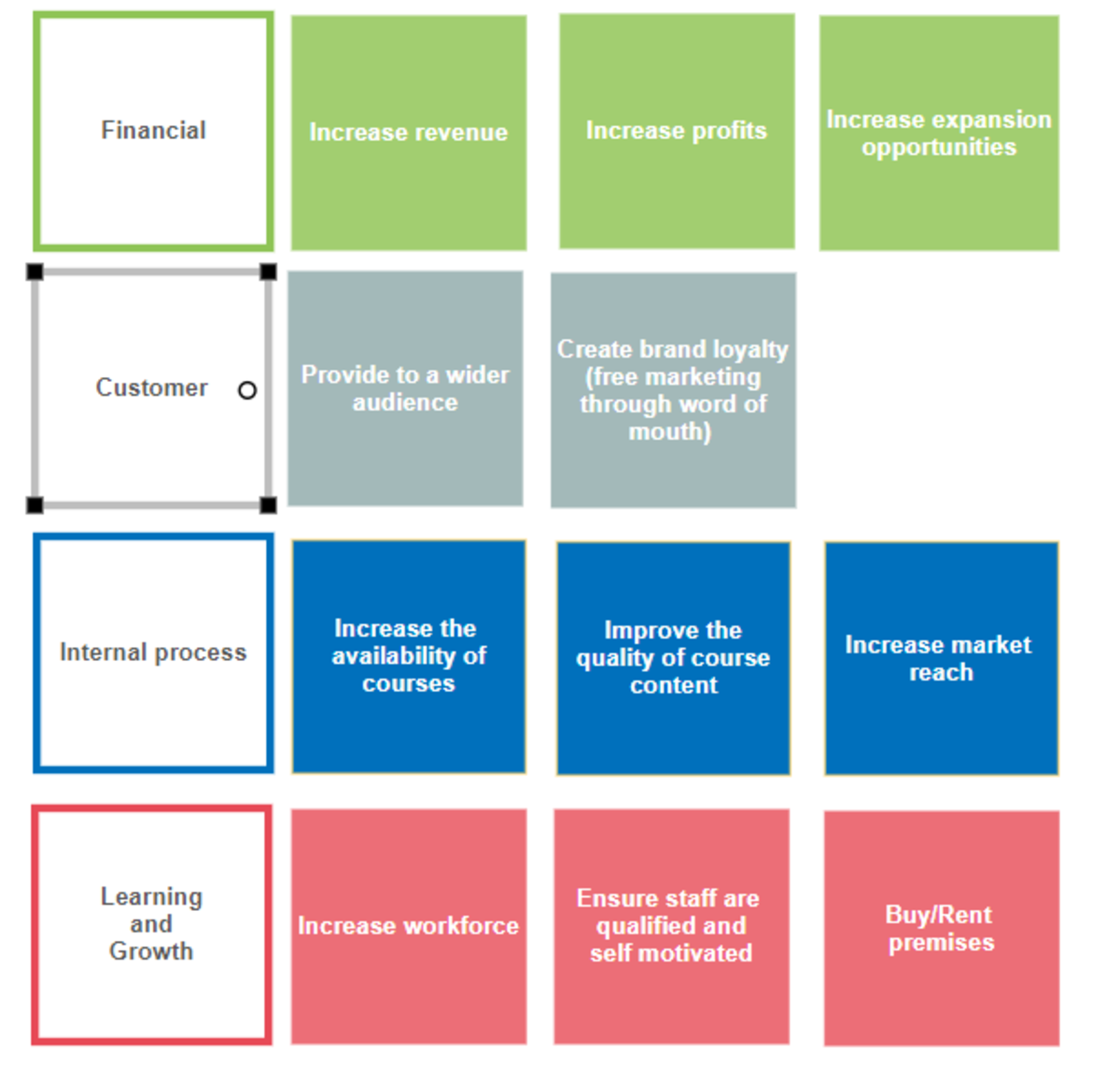
Internal controls is the collection processes enforced by people (board of directors, management team and other members of staff) with the aim of getting reasonable assurance that the company’s objectives will be achieved. The objectives of companies are in the following broad categories
- Reliability of financial statements
- Effectiveness and efficiency of operations
- Compliance with applicable laws and regulation.
Internal controls aim to ensure that company’s objectives are met. What internal controls set out to achieve are collectively called control objectives/goals. One way of evaluating internal controls to see if it is effective enough to reasonably guarantee that control objectives are achieved is to have a look into the components of internal controls and how management reacts to the challenges that they provide.
COMPONENTS OF INTERNAL CONTROLS
Components of internal controls are listed and explained below:
- CONTROL ENVIRONMENT
Control environment is the basis of every other component of internal controls. It is the architecture of the internal controls. Issues concerning; behaviours, ethics, competencies, loyalties and integrity needs to be addressed here. Of what benefit will a comprehensive system of internal control be if it is not implemented? The control environment sets the tone that ‘people’- the principal agent of internal control- will dance to. Auditors should review the following documents in order to get the true picture of the control environment of the internal controls.
Þ Management’s statement of philosophy
Þ Entity’s code of conduct/work etiquette
Þ Internal audit manual
Þ Human resource policies/evidence of candidate’s background check
Þ Organizational structure
Þ Job description manual (both formal and informal)
Þ Financial reporting manual
Þ Disciplinary action handbook, etc
Note that all these are geared towards gaining an understanding of –people- in the system. An auditor should not place much reliance on an internal control operated by inexperienced accounting staff or that is characterized by high level of staff turnover. Auditors should also have a close look at the reason for the sack of employees. It could be as a result of the employee refusing to comply with the implementation of improper accounting policies/procedures desired by the management. Get as much information you can get from the audit committee as possible.
- RISK ASSESSMENT
Risk assessment is central to the success of every business venture. Auditor should ensure that management is using the best management practices to; identify risk, estimate their significance and likelihood of occurrence and manage the risk. The adoption of the enterprise risk management framework is a good yardstick to use. Note also that it is still the responsibility of the management to carryout risk assessment. The auditor’s duty is just to gather enough information regarding risk assessment so that he/she can reasonably estimate the weight to place on IR and CR.
- CONTROL ACTIVITIES/ACTIONS
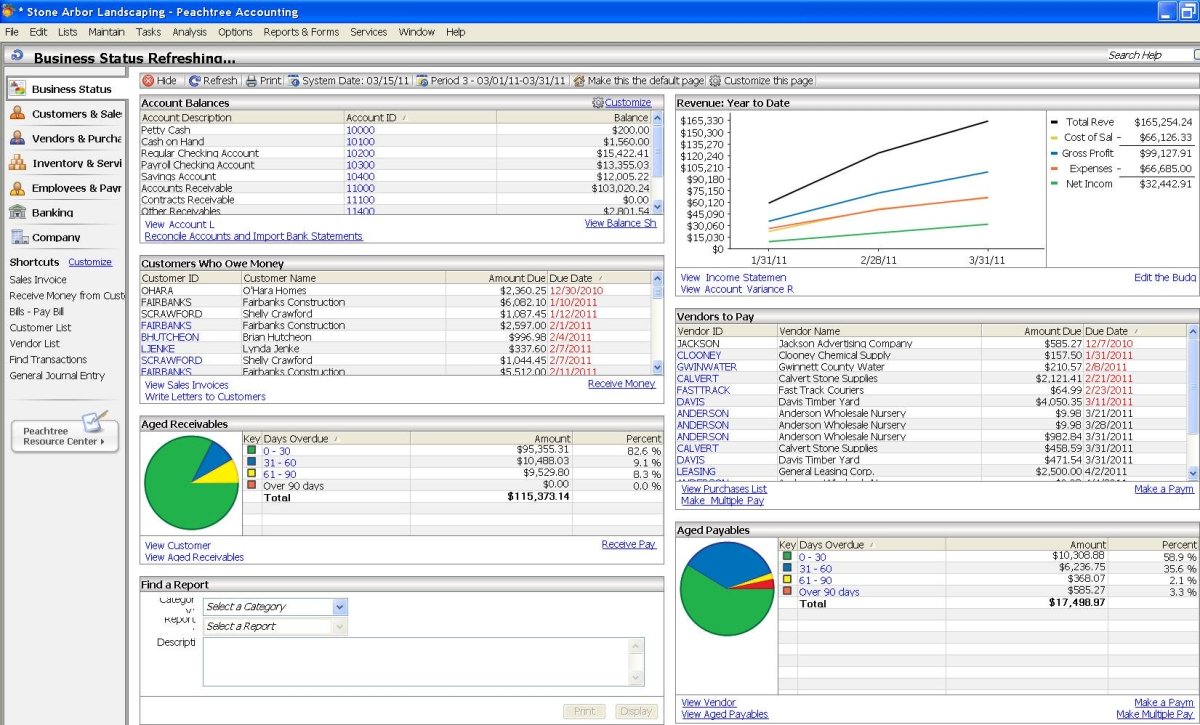
One of the objective of carrying out the exercise of risk assessment is to enable management establish control measures that will counter the negative effects of the already identified risks. Control actions can either be computerized or manual it does not matter. What matters is that their objective is to ensure the achievement of management’s objectives –which includes; prevention detection and correction of errors and frauds that would otherwise enter and flow through the financial statements. An activity that prevents frauds and errors before they occur is preferred. Examples of control activities includes; segregation of duties, physical controls, performance reviews, computer controls, arithmetic controls, etc. as an auditor, you must be satisfied with the level of controls activities in place in a client’s system of internal controls.
- MONITORING
This is an ongoing evaluation of controls that management must to still be true to their assertion that they have good internal control as required by the SOA (Sarbanes Oxley’s Act 2002). Note that this does not include the regular management and supervisory control activities that employees perform in their normal day to day activities.
- INFORMATION AND COMMUNICATION
The information and communication component of the control objectives is so important that management must not do without it. The importance of communication and information in any system cannot be overemphasized. Remove information and communication and watch the world economy collapse. This explains why information sector of every economy thrives more than most other sub-sectors.
CONCLUSION
It is a well known fact that the best way to prevent, detect and correct fraud, errors financial crimes and theft is to have a good system of internal control in place. As the pressure on auditors to lend more credibility to information continue to grow, the need for auditors to reduce their audit risk increases. This audit risk is a function of Inherent risk, control risk and detection risk. Making good estimate of IR and CR will help auditors get a reasonable figure for DR which will act as a compass to the achievement of the desired audit risk.
To your successful auditing career!
- auditingauditor.com
Useful links for auditing resources. - auditors and auditing
Auditing and auditors has recently been assigned a new role by the unseen hands of business reality and challenges that is continually changing. Auditing and auditors new role is necessitated by the...