A Look at the Issue of Cyberbullying in Today's Technological World

With school yard bullying, the victim is able to go home and have a safe place to get away from the bullying that happened at school. With growing technology and the use of social media, however, there is no longer an escape. In an interview with Kathleen Dunn, Justin Patchin, professor of criminal justice and co-founder of the cyberbullying research center, defines cyberbullying as “willful and repeated harm inflicted though the use of cell phones, computers, and other electronic devices or using technology to harass, to humiliate, to threaten, to tease, and the forms or types are just as varied as the technology” (Patchin, 2014). Patchin also explains that the method used to cyberbully is constantly changing with technology (Patchin, 2014).
Patchin also discusses the reasons students may cyberbully. The top two reasons that he has heard are revenge and that they think it is funny (Patchin, 2014). When a child thinks they are just joking around, it can be hard to understand the feelings the victim is having (Patchin, 2014). Some individuals have a hard time seeing that words do wound and do not realize the harm that comes from them posting (Patchin, 2014). When things are being done online, students do not think they will get caught and can hide behind the anonymity they have online (Patchin, 2014).
Patchin talks about the reason cyberbullying is so bad. It is because social cues cannot be seen when posts or comments are made online (Patchin, 2010). For instance, if a classmate comments on a friend’s picture on Facebook, the classmate may be joking, however, the friend cannot tell if the classmate is joking or making fun of him or her. For in-person bullying, the bully has to face immediate consequences (Patchin, 2010). This could be the victim crying, hitting the bully, etc., but when cyberbullying occurs, the bully does not get a response and because of that cannot see that it is time to back off (Patchin, 2010). The first two responses teenagers have when they are being cyberbullied are to first, delete the evidence of cyberbullying and second, retaliate (Patchin, 2015). When being publicly humiliated, teenagers think they need to respond back to the bully, but this is the worst thing they could do (Dunn, 2015).
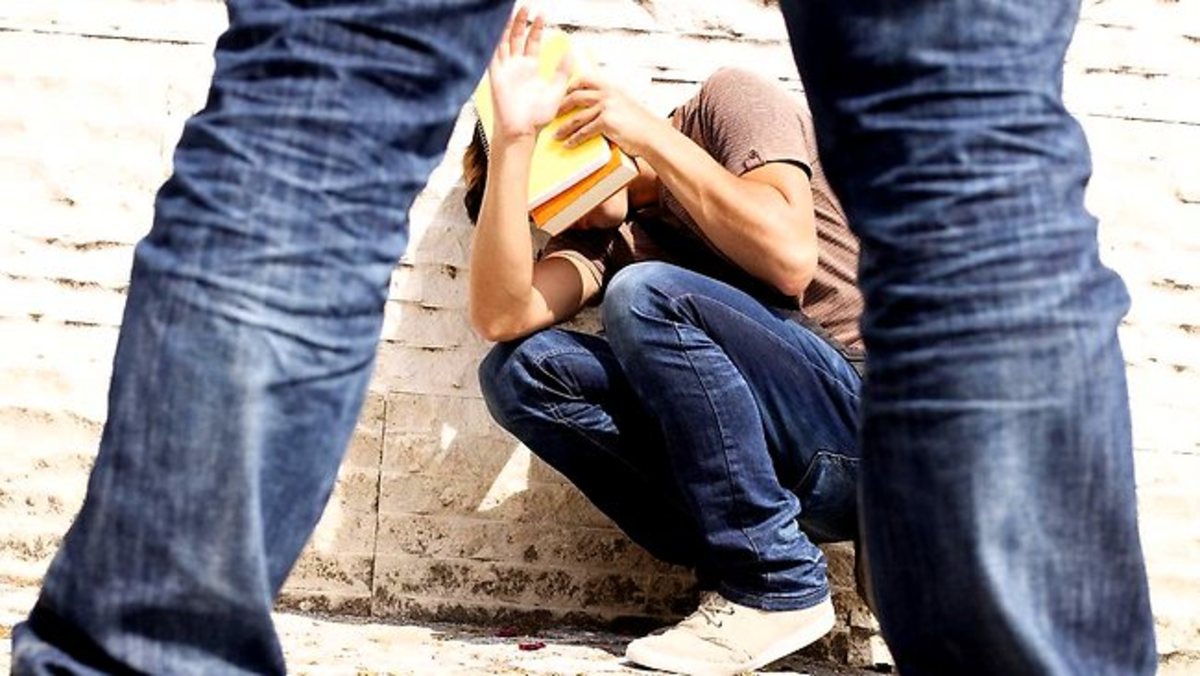
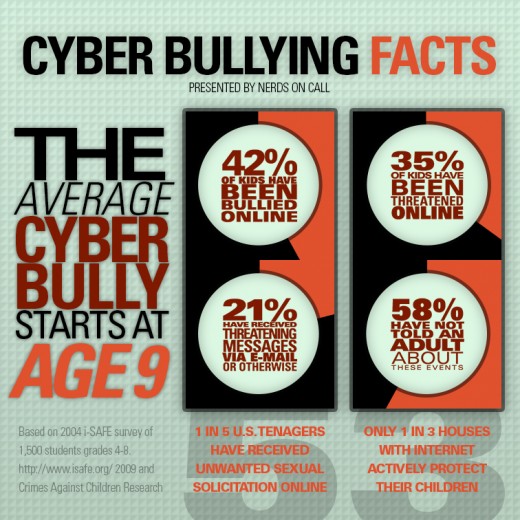
This is how real it is!
Parents Can Help
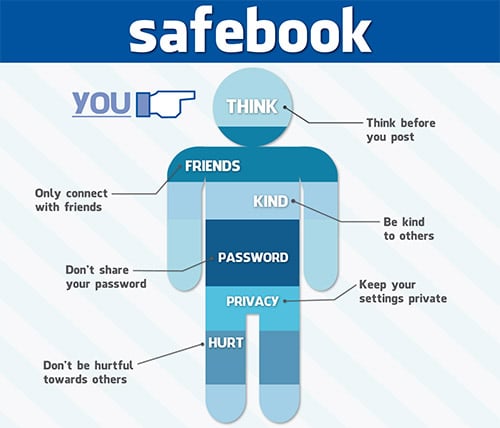
This is one reason education on the subject is important in homes and schools. One of the biggest concerns is that children know real-life rules also apply to online (Hinduja & Patchin, 2014). Rules for interacting with people in real life carry over to interacting with people online, through text messages, etc. (Hinduja & Patchin, 2014). Parents need to make sure the school can properly manage what students are doing online and knows how respond to peer harassment (Hinduja & Patchin, 2014). Parents need to inform their children that there are consequences for inappropriate behavior that is done online (Hinduja & Patchin, 2014). The consequences could be damaging their reputation, getting in trouble with the police, and getting in trouble at school (Hinduja & Patchin, 2014).
When parents model appropriate behavior for their children, this can show the children the right way to behave online (Hinduja & Patchin, 2014). Monitoring a child’s online behavior and activities, as well as using filtering and blocking software can also be important (Hinduja & Patchin, 2014). Some parents have found an internet use contract and a cell phone use contract to be helpful (Hinduja & Patchin, 2014). When there is good parent-child communication, the child feels safe to talk to the parent about issues they may be experiencing (Hinduja & Patchin, 2014). This can be helpful if a child is being cyberbullied.
Is My Child Being Bullied or Is My Child Being a Bully?
There are warning sings to look for to see if a child is being cyberbullied. While these signs do not always mean a child is being cyberbullied, there is probably an issue going on that needs to be addressed. If a child is frequently texting or calling from school wanting to go home early because they are ill or not wanting to go to school in the first place, for instance, this is a sign he or she is being cyberbullied (Hinduja & Patchin, 2015). Another sign is if a child is becoming withdrawn from peers or family or is desiring to spend more time with family rather than peers (Hinduja & Patchin, 2015). A more serious sign is if a child is making statements about suicide or the meaningless of life (Hinduja & Patchin, 2015).
While the above signs show that a child may be the one being cyberbullied, there are also red flags that show when a child may be the bully. If a child appears overly obsessed with popularity or continued presence in a status or social circle, for instance, that is a warning sign the child may be the bully (Hinduja & Patchin, 2015). Also, if a child quickly hides his or her device or switches screens when a parent is close by, that is another warning sign (Hinduja & Patchin, 2015). When a child becomes defensive about what they are doing on their phone or computer this can be a sign as well (Hinduja & Patchin, 2015). For instance, if the child is laughing excessively, but will not tell his or her parent what is so funny.
This is a great resource that can help you learn more about Cyberbullying and what you can do!
What Can I Do?
When a parent or educator believes there is a cyberbullying incident occurring, there are some guidelines to follow in order to handle the situation appropriately. It is the parent’s job to make sure the child feels safe and to thoroughly investigate the situation (Hinduja & Patchin, 2014). A mistake some parents make is banning access to social media or taking a child’s cell phone away (Hinduja & Patchin, 2014). This does not address the underlying issue, and it can make the child feel like he or she was in the wrong (Hinduja & Patchin, 2014). When necessary and appropriate, a parent or educator should contact the police (Hinduja & Patchin, 2014).
One of the first times felony charges were made in a cyberbullying case can be seen in a case in Florida. Two girls were arrested, ages twelve and fourteen, for third degree aggravated stalking felonies after a twelve year old girl jumped to her death (Ashbrook, 2013). This is new territory for cyberbullying, and some people called the charges unprecedented (Ashbrook, 2013). If convicted, the consequences could result in having to go through anger management, probation, and sanctions to keep them from social media (Ashbrook, 2013). The girls, however, were not convicted and the charges were dropped.
After hearing about the above case from the sheriff Ashbrook interviewed, it was a turning point for me when it came to thinking about cyberbullying. I had no idea cyberbullying caused such real tragedies. At least one out of every five middle and high school students are victims of cyberbullying (Hinduja & Patchin, 2015). The cyberbullying research center has many cases of cyberbullying and unfortunately from the many I have heard and read about, most end in the victim committing suicide. With such a devastating outcome to cyberbullying, my thoughts were that there should be more preventative measures taken in schools and stricter laws regarding cyberbullying.
We need AWARENESS
A few measures that could be taken in schools include internet safety education programming, adding a formal contract to the school’s policy handbook regarding cyberbullying, educate the community, use peer mentoring, and teach students about bullying and how all forms are unacceptable (Hinduja & Patchin, 2014). The students should know that even if the bullying occurs outside of school, if it is a disruption to the school environment, it is subject to school sanctions (Hinduja & Patchin, 2014).
When it comes to legislation and case law, in January of 2015, forty-nine states had laws in place for bullying prevention (Hinduja & Patchin, 2015). These laws refer to electronic forms of harassment, cyberbullying specifically (Hinduja & Patchin, 2015). With that being said, not all states formally criminalize cyberbullying, but some actions of cyberbullying already fall under existing criminal or civil legislation (Hinduja & Patchin, 2015). A few examples of these actions include stalking, harassment, defamation of character, and intentional infliction of emotional harm (Hinduja & Patchin, 2015).
It Can be Helped
We know that cyberbullying is a dangerous form of bullying, as it is quickly spreading with the growth of new technology and the all-consuming use of social media and networking. Cyberbullying is different than schoolyard bullying, and thus needs addressed accordingly. There are ways to prevent and respond to cyberbullying as well as red flags that can be used to identify if a child is the victim of a cyberbully or the cyberbully. As technology growth increases, so do laws that protect those being cyberbullied. With that being said, we need more. Help to raise awareness and protect our children!