Book Review: Asymmetric Warfare


Asymmetric Warfare
Many people offer thoughtful theories that are often wordy and primarily founded on other theories to the point that they can’t stand alone. For a long time there were a lot of words that described the exclusive attributes of unconventional warfare or military operation other than war and non-state opponents. Roger W. Barnett does propose a theory on asymmetric warfare, and successfully puts his finger on the drop of mercury that defines it. He explains asymmetric warfare as: “those actions that an adversary can exercise that you either cannot or will not.” (Barnett, 15) Barnett teaches at the Naval War College in Newport Rhode Island. He served in the U.S. Navy where he attained the rank of Captain before retiring. While on active duty, he headed the Strategic Concepts Branch and while working for the Chief of Naval Operations, he headed the Extended Planning Branch. He has proven himself both experienced and capable and therefore a dependable source of information on asymmetric warfare.
Barnett says that, “the central concern is neither to advocate avoidance of the use of force nor to remove all constraints on the use of force” (Barnett, 22). He is of the persuasion that force should be readily available and effective to keep the enemy “honest.” In creating this state of affairs, one also makes military force unnecessary. Such a mentality is common among martial artists who are very much capable of defeating most anyone in a fight and yet seek to resolve differences peacefully. A more historical case in point is Roosevelt’s advice to speak quietly but carry a big stick.
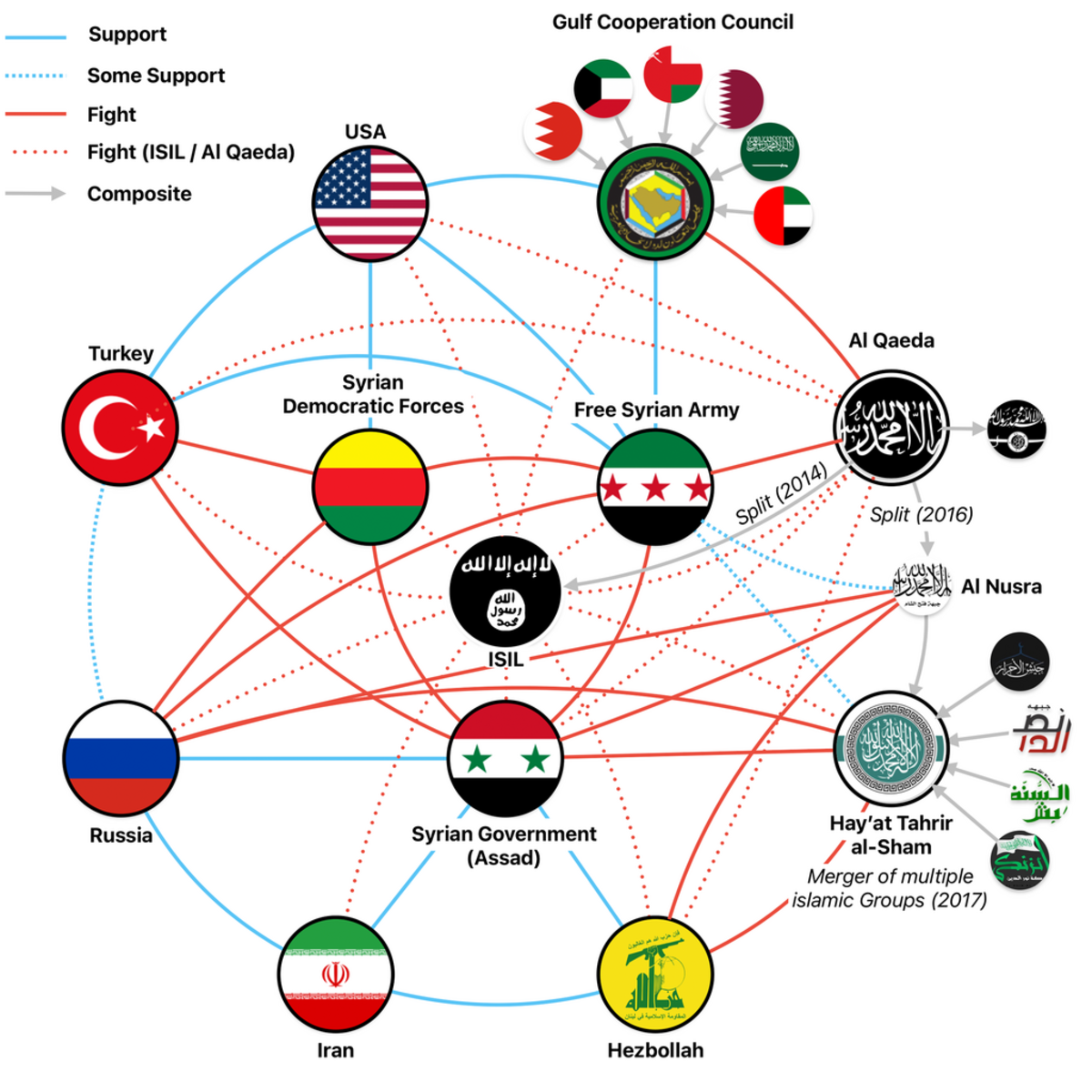
Barnett shifts away from the commonly accepted definition of asymmetric warfare, which is generally explained as opponents seeking to exploit each other’s weaknesses, and hit where it hurts (think a kick to the groin); a historically effective and common sense strategy. His theory is more comparable to hitting someone where they can’t hit back; imagine a woman slapping a man in the face. He summarizes asymmetric warfare as taking calculated risks to capitalize on an adversary’s inability or unwillingness to prevent or counter certain courses of action. For example, the U.S. could use nuclear weapons on Afghanistan, as well as Peshawar and Quetta in Pakistan, all Taliban hotbeds and strongholds. However, the collateral damage would make us perpetrators of genocide. We could start beheading Taliban and Al Qaeda commanders on Youtube.com, but that would make us no better than the enemy we seek to defeat. The thing is that while these tactics would be effective, as a nation, we will not resort to them.
There are many constraints that force America into an asymmetric position by tipping the scales to favor the insurgents and terrorists that we combat today. Barnett covers the operational, organizational, legal and moral constraints, as they exist in U.S. and for Americans abroad. Furthermore, he goes on to discuss the impacts of and remedies for these constraints on the political situation
The constraints that the U.S. imposes on itself in an attempt to maintain its image in the court of public opinion and the world stage should be reviewed and limited because we are tying our own hands knowing full well that we’ll be walking into a massacre yet again. In his concluding statement, Barnett states that, “When the defensive use of force, however, is clearly called for, U.S. decision makers and practitioners of the employment of military force must be granted at least a level field of operations and the ability to reduce the risks that must be run” (Barnett, 156).
Asymmetric Warfare is written in a slightly elevated language that requires the reader to have a diverse vocabulary or a good thesaurus readily accessible. There is a hint of a “know-it-all” tone. Other than that, the vibe is very much pro-American, though it does have the attitude of a frustrated patriot when Barnett starts to talk about the constraints that American has created for herself, causing so many problems as we continue the Global War on Terrorism.
This book is useful to newcomers and old salts in the intelligence field as it challenges contemporary thinking and the commonly accepted opinion of what asymmetric warfare is. The general definition of asymmetric warfare seems insufficient when compared to this writing, which should be read in conjunction with other works on the matter for the sake of comparison. It would probably be most beneficial if it were read early on in one’s studies of insurgencies, after the reader has a grasp of conventional opinions and definitions, but before they become stuck in their ways and unwilling to entertain new ideas.
This book provides an unconventional approach to unconventional warfare that provides some mental stretches for people who have preconceptions about asymmetric warfare and offers up a new theory that seems to be very much valid. The nearly half page of footnotes at the bottom of most pages indicates that Barnett did his homework and put a great deal of research into developing and supporting his theory. Asymmetric Warfare is term that is often used as an empty buzzword. Barnett succeeds in giving it meaning through thorough analysis of U.S. strategy and offers advice on how to effectively counter the strengths of asymmetric opponents that make it so effective against our conventional forces.
Bibliography

Should you be interested in more