Cyber-bullying in Adults?
We have all heard of bullies. They have been around in every school ever since I can remember. Back when I was in school, a long, long time ago, I remember they usually homed in on a single student and tormented that student to the point of madness. The attacks involved ridiculing, stalking, theft, physical violence and every other form of harassment imaginable used to belittle and subjugate their prey into submission. Bullies like to hang around in groups of two or more because they need an audience to reinforce their hostile behavior. Back then, bullies were usually boys.
In time, girls became bolder and just as hostile as the boys. Yes, there was an occasional fight here and there after school because someone stole their boyfriend or something of the sort but they were isolated incidences. Then girls began to hang around in groups and behaved as bullies, yet, they were not called bullies back then because it was unheard of in those days. Instead, they used the term “cliques.” These “cliques” would accost the other girl in the bathroom, after school, in the gym locker room, or anywhere they can gather without any adult interference and the attack was usually witnessed and even fueled on by spectators.
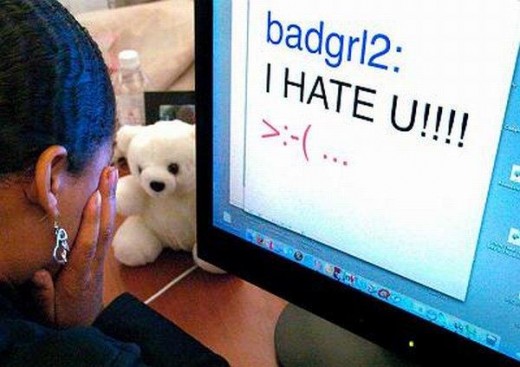
Then came new technology and a new form of bullying emerged. This new form of bullying is done in a less personal way, that is, the attacks come via e-mail, texting, phone, or the internet rather than the face-to-face confrontations. This type of bullying is called Cyber-bullying.
Cyber-bullying is by far the worst kind of bullying. The emotional and psychological damage caused is more devastating because today’s technology allows the abuser to have easy access to the victim any time they wish. It also allows the bully the ability to spread harmful information or images that can reach thousands of people in an instant by clicking only a few keys. Once the information gets out in cyberspace, the damage done is irrevocable and irretrievable. The internet has many wonderful uses but in the wrong hands, it has been known to destroy lives.
According to stopcyberbullying.org, cyber-bullying is “when a child, preteen or teen is tormented, threatened, harassed, humiliated, embarrassed or otherwise targeted by another child, preteen or teen using the Internet, interactive and digital technologies or mobile phones. It has to have a minor on both sides, or at least have been instigated by a minor against another minor. Once adults become involved, it is plain and simple cyberharassment or cyberstalking. Adult cyberharassment or cyber-stalking is NEVER called cyberbullying.”
I agree with this definition, except for the part where it states that when adults become involved, it is called cyber-harassment or cyber-stalking and not cyber-bullying. Cyber-bullying occurs in adults as well. Whether a child, a teen or an adult commits the offense, it is still called bullying. The word “cyber” is just a prefix to specify how the bullying is being done.
The maturity and behavior of the bully is always childish and maybe that is one reason the term “cyber-bullying” is pinned to children and teens. However, adult bullies behave just as childish and immature, and I feel the term fits them justly. The age of the bully has no bearing on the damage they can cause; the consequences are the same and sadly, many times the abuse has resulted in death. Therefore, age has nothing to do with it. A crime committed by a child, a teen or an adult is still a crime.
Many states have laws against cyber-bullying and when these laws were established, they were made with minors in mind in order to allow school officials to take action against cyber-bullies. This may be the main reason why the term “cyber-bulling” is not applied to adults. However, whether the bullying is done in school, at work, in person or via electronic communication, by either a child, teen, or an adult, a bully is a bully. You may pursue legal action according to the laws written for adults and use the term cyber-stalking or cyber-harassment but it does not change the fact that an adult bully using any form of electronic communication is still a cyber-bully.
Cyber-bullies can be hard to track but not impossible. Sometimes it is someone you know or suspect and sometimes his or her identity is unknown. Many times, you will see them in internet forums. You will know them because they will enter topic discussions and begin to bash a person or a group of persons whose beliefs differ from theirs. They will hide behind pseudo-names and images to disguise their identity and their attacks are relentless, always trying to prove their point and calling attention to themselves. Their attacks are fueled by their hate and when others join the attacker, it reinforces their behavior.
Just recently, I observed in a forum a cyber-bully continually attacking a Christian woman. By their interaction, I concluded this bully seemed to follow this person wherever she went on any of the discussion forums and would start the verbal attacks aimed at her beliefs. Being a Christian myself, I immediately knew what this victim was feeling; I have been there. Soon enough, others joined in on the bashing. If I can put all of this in one word, it would be HATE! She tried to ignore the bullies but they continued with the verbal assaults. When she tried to give them a reply, they went as far as calling her names.
As I read this bully’s remarks and how he tried to ridicule and reduce her to a mindless, Bible brainwashed nitwit that had no thought of her own nor any IQ, I could not help to wonder if he was just trying to hide his own low two-digit IQ by being condescending and insulting. It was then I was reminded how Jesus dealt with Satan when He was tempted in the desert. Every word preceded out of Jesus’ mouth began with “It is written” then he would quote the Word of God and that was the end of it. Jesus did not argue; He did not have to prove anything. Satan knew who was boss.
A word to my fellow Christians, Christians do not need to argue with anyone about the Word of God nor try to prove anything. It is not for us to defend or prove anything; it is for God to do that. God is quite capable you know; He does not need our help. Moreover, if you have read your bible, you know what will happen in the end.
Then how do we deal with cyber-bullies? You can do many things. Learn about the laws in your state. If you suspect who the person is, go to your local law enforcement, file a complaint, and ask them what they can do. If they are phoning you or texting you, have your phone company trace the calls and if available, use the block features in your phone. Avoid community chats and social networking sites, and most importantly, avoid posting any personal information on the internet that can identify you and your whereabouts. If the bully is cyber-stalking you, report it to the site administrator. Warn the bully that if they do not stop, you will take action. Do not engage in an argument with the bully because that will only leave you feeling worse.
Furthermore, do not let them intimidate you because they thrive on your fear. Remember they feel powerful because they are sitting behind a computer and you cannot see them. Lastly, talk to others. Sometimes in talking to others, you may learn of other ways to handle the situation. And remember, awareness is the key.

© Faithful Daughter