- HubPages»
- Technology»
- Computers & Software»
- Computer How-Tos & Tutorials
Backup solutions and disaster recovery strategies for small business
Introduction
In the event of data loss or a catastrophic event such as a natural disaster or terrorist action, in order for the company to return to a state where business can be conducted as quickly as possible, a backup plan and a disaster recovery strategy must be in place. Not having such strategies in place and regularly tested could result in a significant monetary loss or even result in the closure of the company in the event of a significant disaster.
Backups
Backing up data and ensuring that the backups are securely stored is critical to ensure that in the event of a catastrophe or a file / folder restoration request, data can be restored. It is a critical part of any company’s IT strategy and small businesses are no different in that respect. A backup strategy should cover any data without which a company could not function either in the short or long term or the loss of which could cost the business money. Some important considerations include:
- Backups should be held in secure location such as a safe
- Backups should not be stored onsite
- A restoration of backup data should be occur regularly to ensure backups are fully functional
- Servers should have their System State backed up (please refer to the below link for further details
http://technet.microsoft.com/en-us/library/cc785306(v=ws.10).aspx
Within a small business, it may not be necessary to use backup tapes or backup software, it may be sufficient to backup to DVD or other removable media. The most important aspect of a backup schedule is that they are performed regularly, validated and securely stored off-site.
Cloud Computing
Cloud computing is an alternative to traditional backup options. It has several advantages including that the data is readily available in any location that has internet connectivity, as well as its cost effectiveness. There have been concerns expressed regarding cloud computing with respect to security breaches and a perceived loss of privacy. Serious consideration should nevertheless be given to the advantages of cloud computing for small businesses especially when coupled with Software as a Service (applications are installed and accessed remotely, eliminating the need to install, configure and maintain applications) due to its cost effectiveness and flexibility.
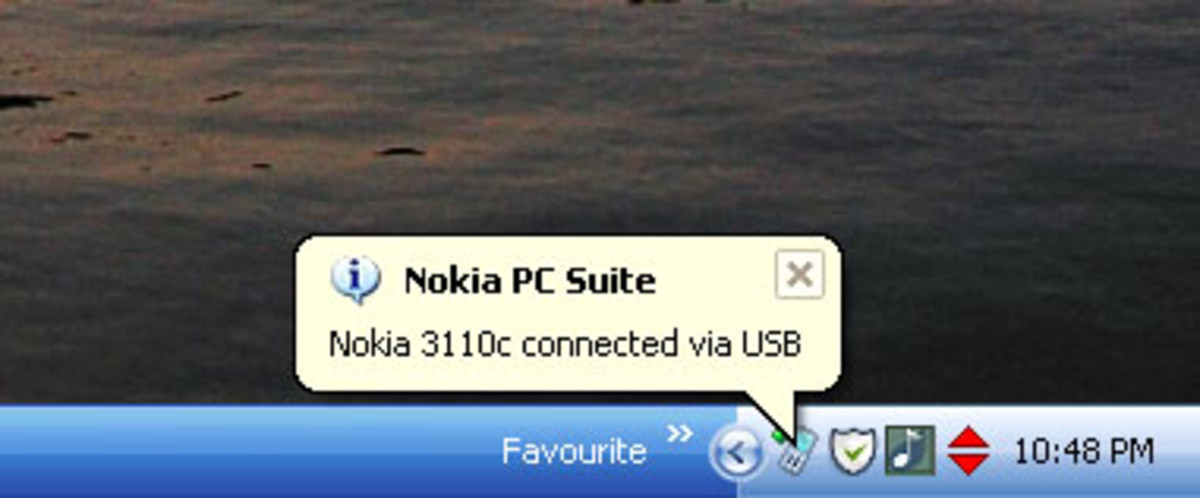
Shadow Copy
In firms with servers running Windows Server 2003 or later, Shadow Copy can be implemented on shared folders. Once implemented and configured, Shadow Copy will allow users to restore their own files in the event of file loss, corruption or if the file is accidentally overwritten. Although it requires some configuration to set up, it is significantly easier and more cost effective for users to immediately retrieve old versions of a file compared to restoring them from backups or having the employee recreate the lost work. When a user wants a file or folder restored using shadow copy, they simply right click and select Previous Versions as shown below. The user can then open files to find the one they would like to restore and then restore it simply and quickly.
Please click on the link to my Introduction to setting up Shadow Copy http://robbiecwilson.hubpages.com/hub/Guide-to-installing-and-configuring-Shadow-Copy-for-Windows
Disaster Recovery
In the event of a catastrophe or disaster the ability of your business to trade may be severely impaired or even halted. To ensure that this does not happen or that any impacts are significantly reduced, a disaster recovery plan is essential. To better understand the connotations of disasters or catastrophes, an impact assessment should be completed outlining the risk and the likelihood of all possible scenarios no matter how unlikely ranging from localized power outages to widespread terrorism. Once the risks are better understood, a disaster recovery solution for your business can be outlined. There are a number of key aspects to any disaster recovery solution
- Creating the solution: all aspects of the business must be involved in the creation of the disaster recovery plan and must communicate their needs in the event of a disaster so that these can be covered in the plan itself.
- The solution must be regularly revisited by all aspects of the business to ensure that the solution continues to meet the needs of the business. Specific people should be assigned the responsibility of ensuring that the solution remains current and that regular testing takes place.
- Regular testing should occur at least twice a year and any shortcomings or failures must be immediately addressed. A disaster recovery plan that does not work is as bad as not having a plan in place at all.
- When a disaster occurs, a number of staff must be specified as being responsible for invoking the disaster recovery solution including initiating calling trees to ensure that all staff are notified.
There are many ways of running disaster recovery for a small business quite cheaply and successfully in the event that a disaster should occur.
- Arrangements could be made with hotel(s) that a small conference room be made available at short notice as an office. This could be done with more than one hotel in a different location to provide additional redundancy. The hotel would cover the networking, telephony and office space, leaving the business to provide any computer equipment required (this could also be stored on site).
- Another method is to rent space at a datacenter. This can include a set number of PC’s available at very short notice, configured and ready to be used. This is typically more costly depending on the number of spaces required, but the space is dedicated and manned typically 24 by 7 by 365.
- Software as a service (SaaS) can also form the basis of a disaster recovery strategy. Using SaaS, applications are accessed remotely, enabling the applications to be available from anywhere with a stable internet connection. If the ability to access applications from anywhere with an internet connection is also allied with the storage of the company’s data in the cloud, then this gives a company a great deal of flexibility in a disaster. There is a typically a monthly fee for SaaS, but this frees the business from installing, configuring and supporting the software hosted.
Battleboxes
A “battle box” can be compiled and stored in a secure location(s) to ensure that the business can continue in the event of a disaster. This can be used in conjunction with the solutions above, especially in a disaster that runs longer than a few days. The “battle box” should contain:
- A full backup of your companies data
- Copies of any documentation or paperwork your company relies on
- Each department should provide all its essential procedures and policies
- Enough stationary and equipment to run a small “version” of the office
- Enough laptops to run the business in the short term
- Mobile phones with SIM cards
- Any software required by the business
Conclusion
With an educated staff and an effective and regularly tested and updated disaster recovery plan, a company should be able also to cope with anything thrown at them and to continue to prosper in any situation. If you have any suggestions or comments, please feel free to leave them in my comments section.
Alongside a backup and disaster strategy a comprehensive IT security policy should be implemented to ensure that your companies IT infrastructure is as secure as possible. Setting up such policies is covered in my hub
Good luck with your business, thanks for reading. Please feel free to leave comments!





![How to Remove Kaspersky Password Protection? [Easily Recover] How to Remove Kaspersky Password Protection? [Easily Recover]](https://images.saymedia-content.com/.image/t_share/MTc2Mjk3NDcwOTAzNTkyMTI2/how-to-remove-kaspersky-password-protected-easily-recover.png)
