Computer viruses, trojans, spyware and worms...what's the difference?

These days there are more hazards to surfing the internet and using your computer then people would care to think about. There are always new viruses being produced, new trojans developed, new worms pretty much on a daily basis and anti-virus/anti-spyware programs can only do so much protecting you from new threats. All these threats all cause havoc to your computer and to your life but they each do it in different ways.
Computer Virus
Basically, a computer virus is a computer program that can replicate itself. Sometimes you can tell you have a virus from the "symptoms" that you will experience, but a lot of them don't do anything that let you know you have a virus on your computer. Some don't do anything but continuously reproduce themselves in the background.
In order for the virus to begin reproducing, it has to be executed and be written into memory. A lot viruses attach themselves to an executable file that is already a part of a legitimate program. When you launch the affected program, the code from the virus is also launched along with it. From there, what happens next is dependent on the two of virus types it could be
A nonresident virus is not stored directly on your hard drive. The virus remains in an executable files that will infect your computer every time the program is accessed and run. A resident virus embeds itself into the memory of your computer and is activated whenever your computer performs a specific function and continues to infect files from there. A resident virus can spread so thoroughly in your system that it could possibly even infect antivirus programs. The fact that they are in your system memory makes it very tricky to remove and some are programmed to block any attempts to remove them.
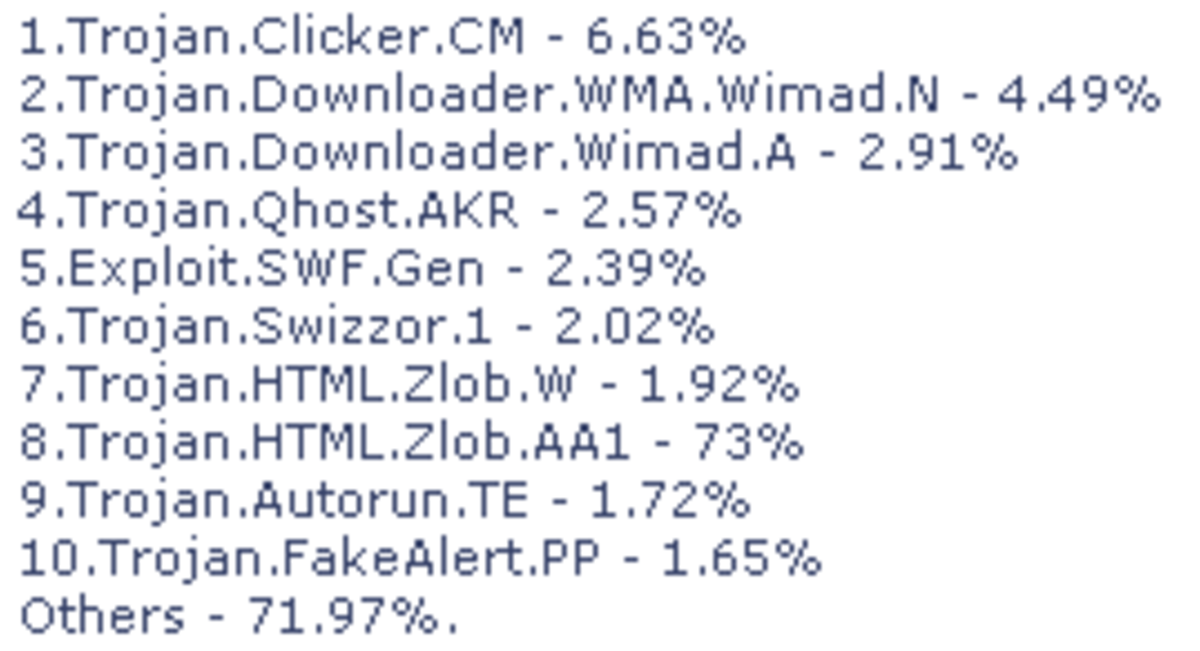
Trojan
This is a program that on the surface looks like a legitimate program but looks can be deceiving. They usually allow backdoor access to your computer to a hacker or steal your information or do other damage to your computer. Once a hacker has access to your computer, he can do everything that you can do on your computer remotely, gather any information that he wants and modify your computer any way they want. Unlike viruses, they don't make replicas of themselves on your system. Your anti-virus/anti-spyware program should be able to scan and detect these as well.
For those that like trivia, the term Trojan is derived from the story of the Trojan Horse in Greek Mythology since they appear to be harmless programs that you will install on your system where in reality they're nothing but trouble.
Spyware
This is software that gathers information about you without your knowledge and sends this information, without your consent, to the individuals that wrote the software.
There are four different types of spyware: system monitors, trojans, adware, and tracking cookies. Generally, spyware is used to track and store your movements on the web and throwing up pop-up ads in your face all the time.
While spyware is used to monitor what you are doing on the internet, it could potentially collect any type of data that it wanted including your user logins and bank account information. Have you ever opened your web browser and it didn't go to your homepage but somewhere else completely? Spyware is responsible for that too.
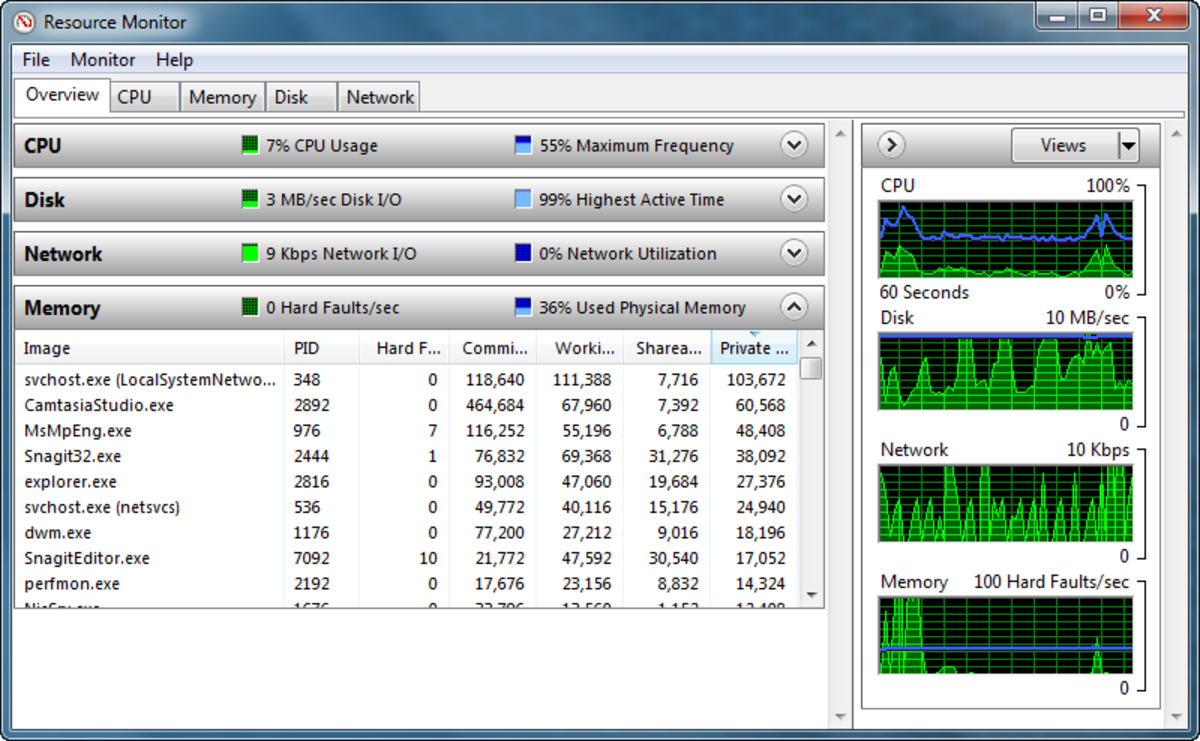
If you have spyware on your system, you'll notice that its performance generally gets worse and can get to a point where, the computer is so slow it's almost unusable. Spyware can disable firewalls and reduce your browser security settings which makes your system more susceptible to further infections.
Anti-spyware programs are vastly available for download and a lot of anti-virus programs have added anti-spyware features to their existing products.
Worms
Worms are standalone programs that replicate themselves so that they can spread to other computers. It uses a computer network network to spread itself to others. You would typically install a worm by unknowingly opening and email attachment that contains the executable script. Once on your computer, they spontaneously generate additional emails that each have a copy of the worm. Worms almost always cause some kind of damage to a network, even if it's nothing more then consuming a lot of bandwidth.
Anti-virus and anti-spyware programs are helpful in detecting them but they must be kept up-to-date since, like viruses and the like, new ones are always being made.
Always remember that even if your anti-virus and anti-spyware programs are up-to-date it is possible to be infected. If the virus/trojan/worm/spyware is released before the company can figure out how to remove it and you download/install/open an email with one of those in it, there's nothing your program would be able to do to help you.