Help Me! I have pop-ups!
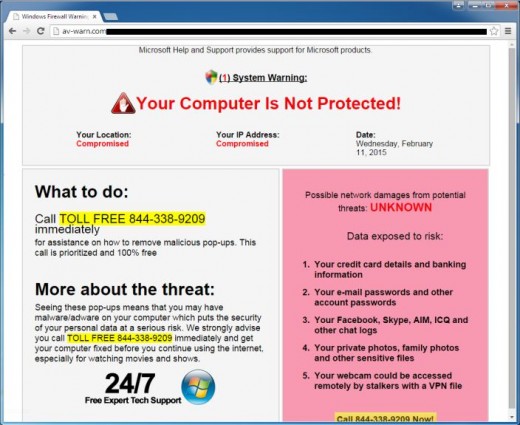
Pop-up Example
What is a pop-up?
Pop-ups are often causes from malware in your computer system. They do not always indicate a virus, and do not necessarily mean anyone has made entry into your computer. More often than not, a pop-up is an indicator that at some point you have downloaded software from the internet and installed additional software, possibly unbeknownst to you, that have made changes to your computer's settings. While this can be a pain to rectify, in most situations this type of issue can be resolved with a little diligence and some additional software downloads targeted at the problem.
Where does Malware come from?
Often, downloading programs that are believed to be trusted is where the problem begins. Downloads of Chrome Web Browser, if downloaded from a source other than Google.com/Chrome, can be one of the quickest ways to get malware in your system. Any time you download anything from the internet, you need to be sure you know what you are downloading. If possible, always use a custom install so the program will prompt you with what you want installed on your machine. Also, make sure you read through the terms of service, as newer programs tend to hide the malware permissions in the terms of service for the software you are intending to install.
MalwareBytes
Now that I have Malware, what do I do?
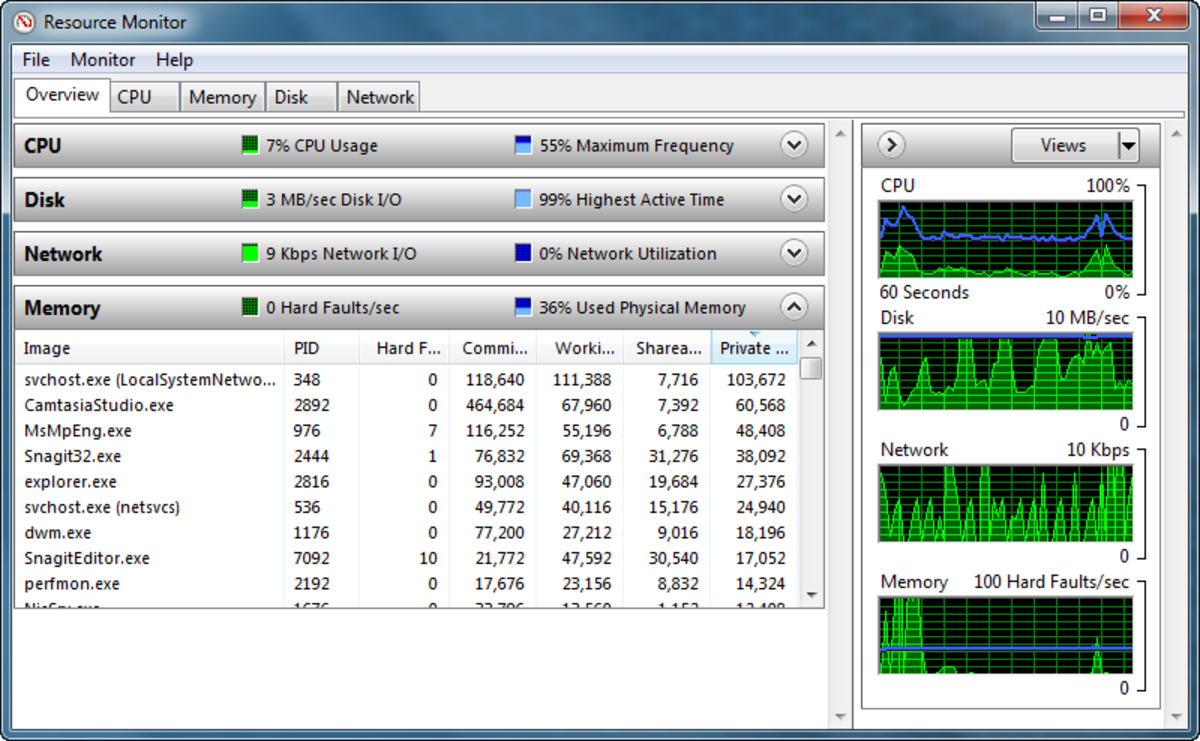
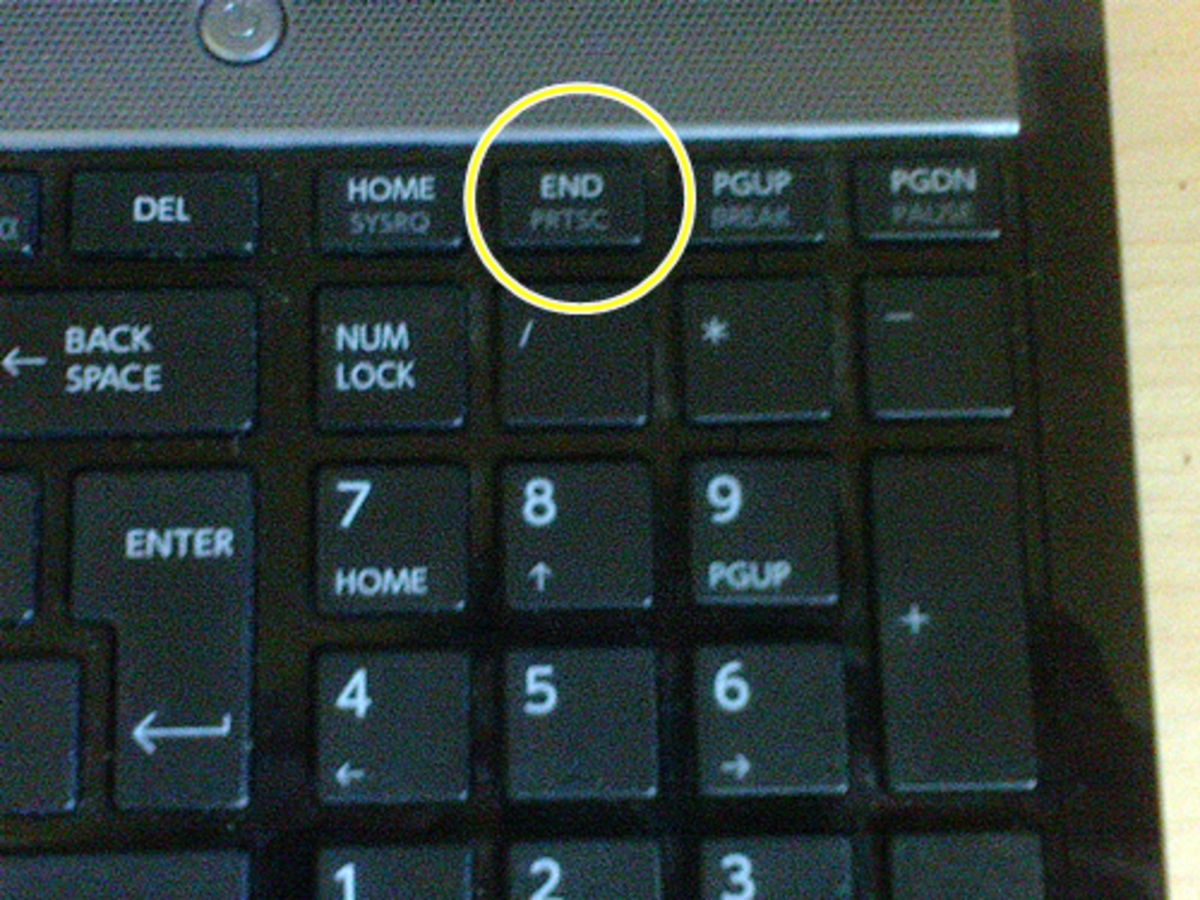
The first thing you should do if you notice malware in your system is to hit CTRL+ALT+DEL and end-task any program that you do not recognize or that is being overcome with malware. Often, end-tasks of internet explorer, Firefox, or Chrome, or any other browser you are having the issue with, will buy you enough time to execute the next step.
Secondly, you will want to enter into safe mode on your computer. If you are able to navigate your system, pressing and holding the SHIFT key while you restart the system will bring you to the recovery environment. From the recovery environment, selecting "Troubleshoot">"Advanced Options">"Startup Settings">"Restart" will get you where you need to be. I highly recommend safe mode with networking, option F5, as you will need to download a program to your computer and run it.
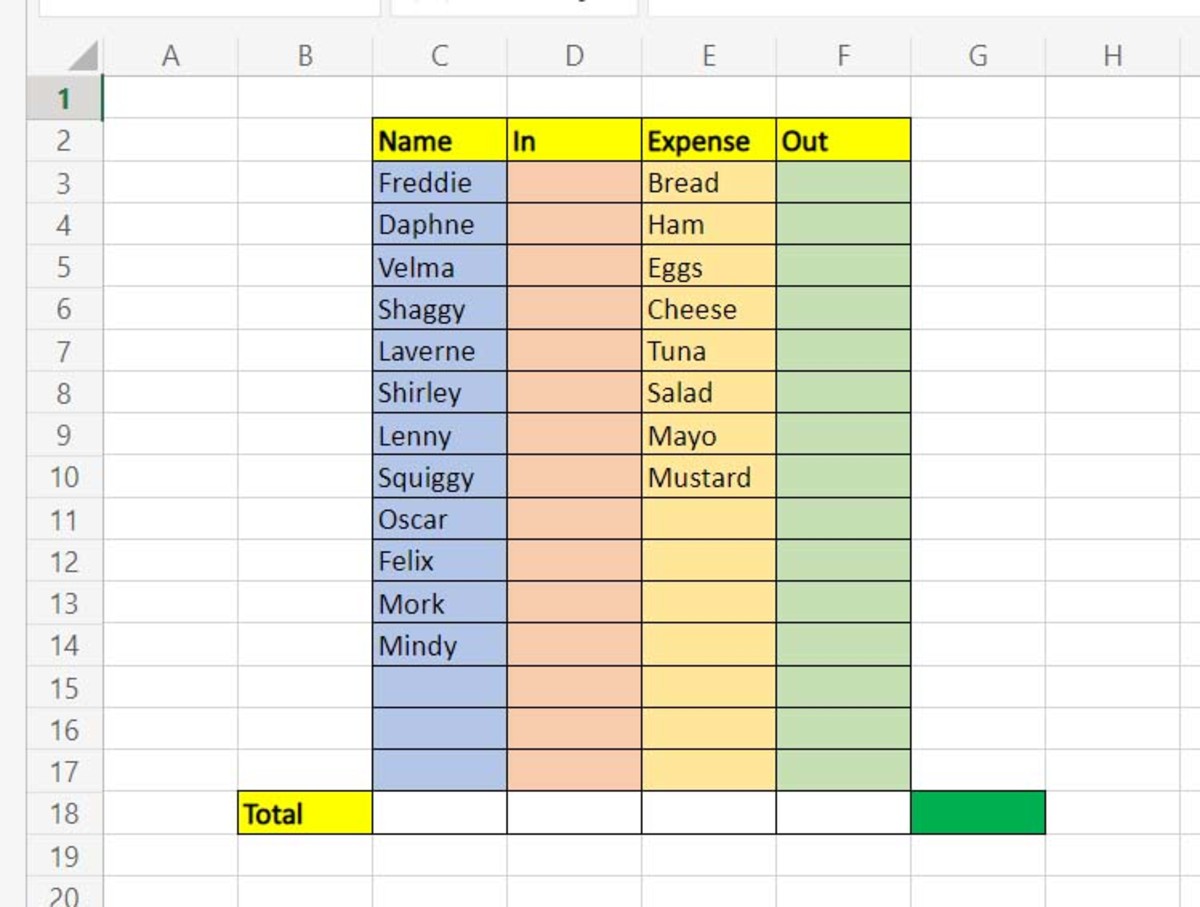
Once you are in safe mode, navigate in your browser to malwarebytes.org, and download MalwareBytes Anti-Malware program to your system. Allow the system to update then run a scan. While the scan is running, go to control panel, internet options, and go to the advanced tab and reset your internet explorer. I also recommend opening up an elevated command prompt and entering the following command: Netsh Winsock Reset. Once this is done, it should tell you that the catalog has been successfully reset, and you will need to reboot your system. By this time, your MalwareBytes scan should be complete. Remove anything that is found, and reboot your system. Upon rebooting the system, you will be back in standard mode.
Back to Normal
At this point your system should be back to normal. You may need to reconfigure some settings after resetting your internet explorer, but overall your system should be working. I recommend running one more scan with MalwareBytes Anti-Malware, and if that finds anything remove it. If you continue having problems, you can download and run HitMan Pro. If you activate the free license for one time use, it is good for thirty days, and should be long enough to do the removals you need to do.
If after running all of the anti-malware programs you are still having problems, it is time to consider calling in IT Professional. The malware on your system could have corrupted your user profile, or corrupted your operating system on the unit. In some situations, replacing your hard drive may be necessary to recover from severe infections.
Keeping Safe in the Future
Once your system is operational again, the important thing is to keep it that way. Regular backups to either cloud or external storage should be done to prevent catastrophic data loss of important files. Keeping your system up-to-date with the latest security patches, as well as running an up-to-date anti-virus with anti-malware component is important.
Remember that not all downloads are dangerous, but all should be treated as such. Downloading programs and files from file sharing sources like bittorrent sites is one of the best ways to reinfect your system, and is also often illegal. Running an anti-malware program on your system directly after download can help prevent recurrence of issues, but abstaining from the activity that caused the issue to begin with is the safest practice.
Tell Us What You Think!
Have you had malware on your computer?
© 2015 MelissaVsWorld