How Has Information Technology Has Helped or Benefited the Common Man and Poor People?
Information has become reduntant!
After the invention of internet, information has become redundant. Most of the time, we are perplexed at the results of search and we are not able to select the exact information out of the millions of results. Of course, the important one is given in the top of the search or it may be seen within ten or fifteen sites of the web results. When the internet was just discovered, there was standing ovation from all people. It is really a magic that everything we want to access is available at the click of the mouse, in the comforts of the home! The senior citizens need not move away to pay their bills, order their groceries and other items. Everything is now available online in many sites. Also, the net banking enables us to pay the monthly bills like telephone, electricity, mobile and broadband charges before the due date. Prior to the invention of internet, the elders used to stand in the long lines waiting for their turn to pay. Now, within minutes, we can finish paying our bills and the computer will generate the e receipt which could be saved on the desktop. Life has become easy, thought many elders like me. But there are many risks associated with quick access to the net. First of all, the elders have poor memory. Most of the time, they forget their ID or password. Using debit or credit card online is highly risky. First of all, the computer should have virus protection software! Otherwise, many cyber criminals snoop through your machine in unimaginable ways and loot your personal and private data. If they could access your debit card or credit card numbers, there is every chance that your card may be cloned in duplicate and without our awareness, shopping on your card might take place in another country or other town! Yes, cyber criminals play havoc in the life of elders and innocents!
Hackers crack the codes illegally!

Data security in this cyber age - Risks faced by youngsters and elders!
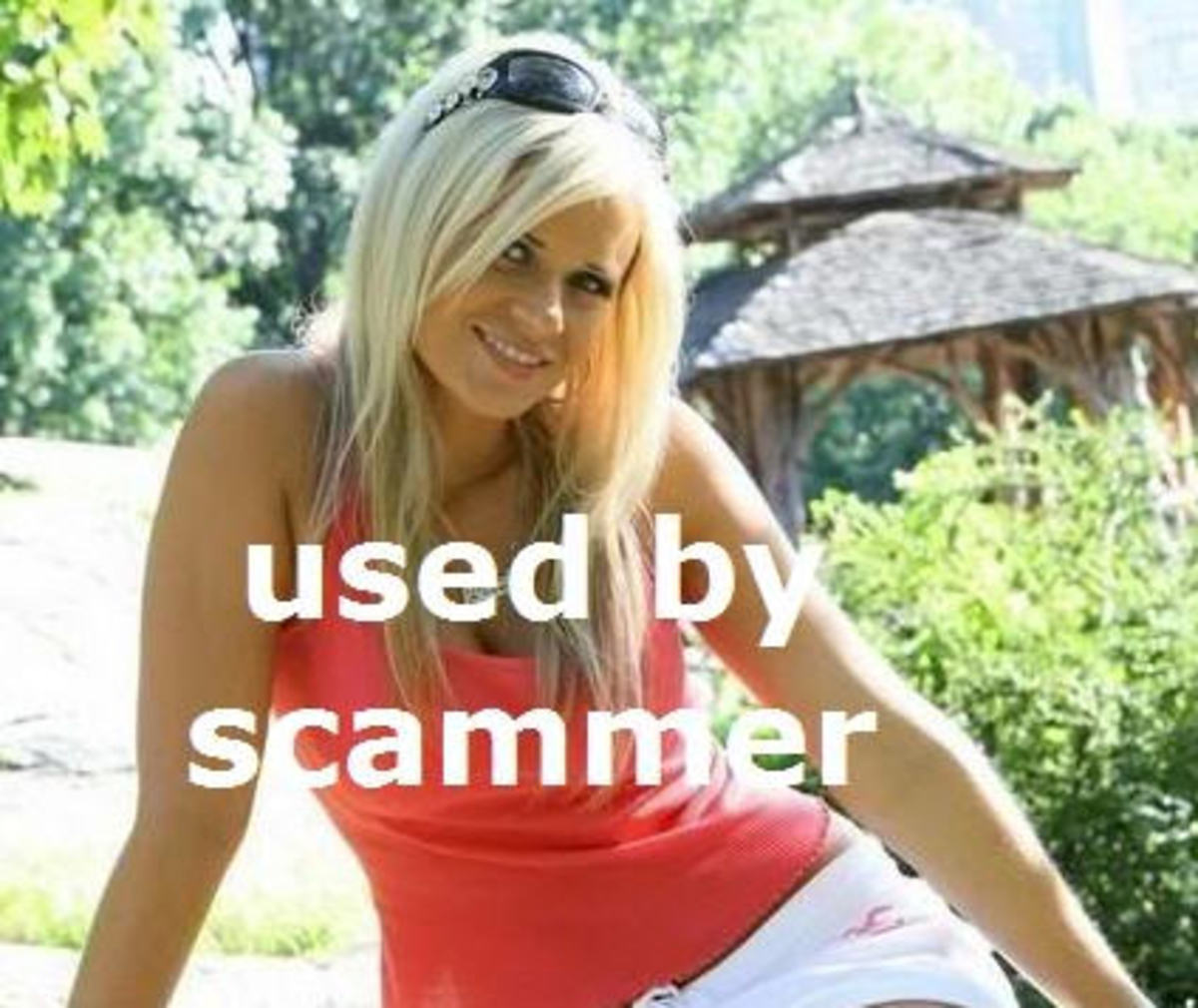
Now many countries are riddled with the problem of data security. There are financial transactions carried out by individuals, banks, corporate entities and the government. If there is any snag or loophole in security, the cyber criminals easily enter into the computers of banks, corporate, governments and other entities. This is how ‘wiki leak’ has published many secret files pertaining to other countries. We know computers are machines which run through machine language. One who is expert in codes and algorithms can break through the security ring and access the codes and create huge loss. Otherwise, they may use bots to enter into your system and erase all the information and make your computer dummy. Hence backups are essential important ways to retrieve the information if the system crashes. In the nuclear age, the topmost leader will have access to the nuclear code buttons and it is a top secret thing. Only the Presidents or Chief Executive of the country will have access to the nuke button. Terrorists are everywhere and there are cyber criminals within terror network. Hence at no time, terrorists should have access to the nuclear arsenal or security code! The world is fragmented with leaders who oppose each other. No country remains in isolation. Hence even a small country has many big brothers protecting the country, in case of war. Hence no country could take unilateral initiative on nuke war against even a smallest country! If nuclear war is triggered mistakenly, the entire world will be burnt to ash in no time. For the sake of welfare of human community, even a erratic leader should not commit the mistake of war against any country in the present internet age. We boast that the world has become a global village! But the benefits of net have not seeped into the poor villagers and they are ignorant as before. Hence, the government must ensure reach of all welfare schemes to the farthest poor in the country. It is solely the responsibility of government and telecommunication managers of this world. We already reap the negatives of free access to any site by youngsters, children and foolish adults. Girls easily fall prey to the fraudsters in social web sites and they divulge their personal details without any apprehension. Each day, we are watching in the media, the havoc played by the criminals on the life of young innocent girls and children. The number of suicides due to illegal games is on the rise. Though they have arrested the brain behind such illegal games, anyone could download the program to meet his doom. Hardly one percent of the educated population get any benefit through the net. The remaining 99% waste their precious times in frivolant talks with unknown people, responding to unknown surveys, revealing all your personal information etc.
Methods used by cyber criminals.
How certain policies of government breach the privacy of common man?
Why there is such a hue and cry on Aadhar implementation? All our personal data, address, phone number and mail address along with finger prints and iris is incorporated in the card. When the criminals could break into heavily guarded servers of financial institutions, cracking on Aadhar database is a child play for the code breakers. Without being aware of the seriousness, the government is fighting its case in the Supreme Court for Aadhar. Despite warning from the court, the government widen the use of Aadhar in many ways. Though the initial idea is to prevent pilferage of ration items, preventing the middleman from looting the poor in delivering their dues, the implementation of Aadhar ensures that the subsidies reach the correct person through his bank account. The aim is no doubt laudable but in the interest of covering all, the government has not thought of security of data base. Such type of lapses may help the cyber criminals and terrorists. We have to safeguard the personal data of all the individuals and this responsibility lies with the people who manage the Aadhar!
Though information technologists may boast the many achievements in the field, it is sad that the poor downtrodden has not benefited in any manner through these new inventions!