Most common attacks on mobile phones

Mobile devices are the next big target for cybercriminals looking to make quick cash, and according to the 2013 Norton Report, 38 percent of smartphone users have already been a victim of cybercrime.
Human factor is important in all stages of security threats. It is often the user, who allows certain attacks to take place and compromises device security measures. A lot of effort has been made to increase user awareness on the topic of information security. Importance of such awareness is especially high in case of BYODs, when companies allow employees to access network with their own devices. To name a few, issues such as attacks via wireless networks, malware and Trojans, spreading through downloaded games or stolen devices have huge potential risks. It is therefore understandable why network administrators are under high pressure in dealing with all those potentially infected devices on their network.

Bluetooth-based attacks
Security issues related to Bluetooth on mobile devices have been studied and have shown numerous problems on different phones. Despite all the defence mechanisms in place, usage of Bluetooth might result in attacks on device through the following methods
Bluejacking: an attacker sends unsolicited messages or business cards to a Bluetooth-enabled device, mostly for advertising purposes. Bluejacking resembles spam and phishing attacks conducted against e-mail users.
Bluesnarfing: idea is to force a connection with a Bluetooth-enabled device to gain access to data such as contact list, calendar, emails, text messages, pictures, videos and the international mobile equipment identity (IMEI) stored in the memory.
Bluebugging: allows attackers to remotely access a Bluetooth-enabled device and use its features, such as read phone books, examine calendar, connect to the Internet, place phone calls, eavesdrop on phone calls through call forwarding and send messages without the user’s knowledge.
Bluesmack: Bluetooth Denial Of Service (DOS) attack where the Bluetooth-enabled device is overwhelmed by malicious requests from an attacker, causing it to be inoperable by its owner and draining the device’s battery.

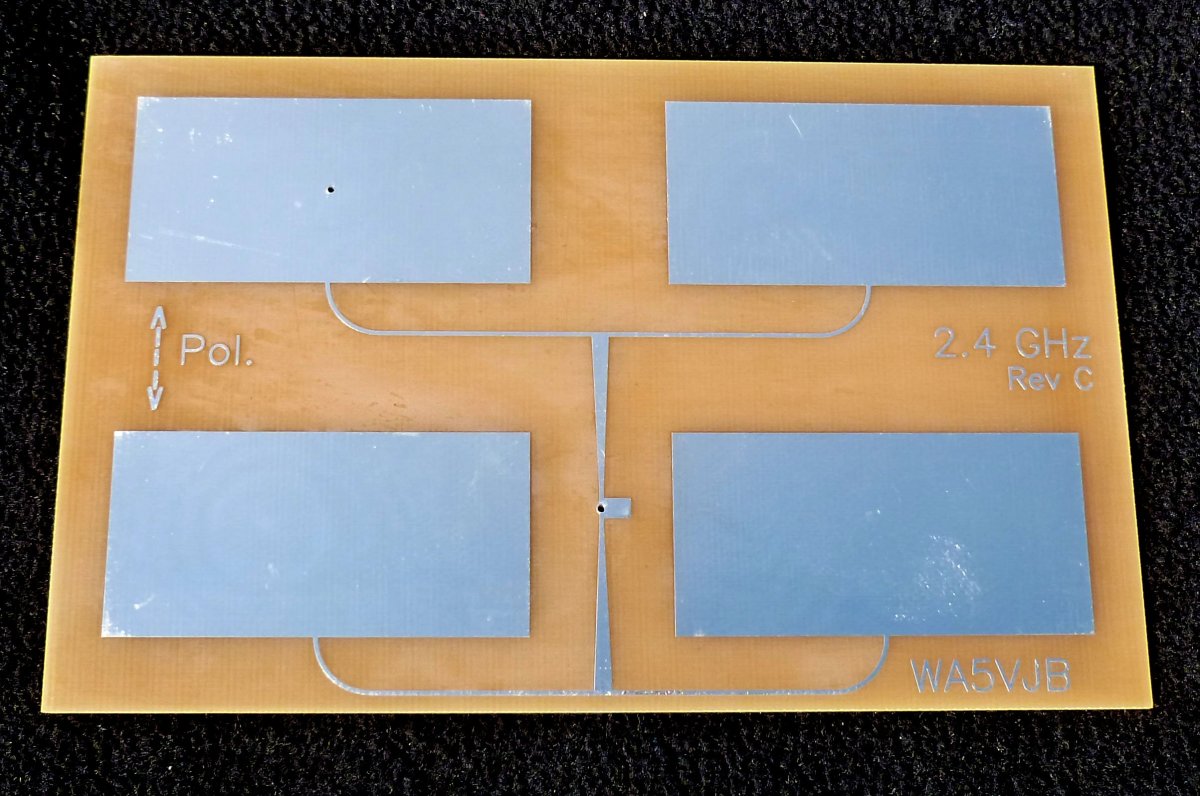
Attacks based on Wi-Fi
Initially wireless networks were secured by WEP keys. The weakness of WEP is a short encryption key which is the same for all connected clients. Now, most wireless networks are protected by the WPA security protocol. The major improvements in security are the dynamic encryption keys. For small networks, the WPA is a "pre-shared key" which is based on a shared key. Encryption can be vulnerable if the length of the shared key is short. With limited opportunities for input (i.e. only the numeric keypad) mobile phone users might define short encryption keys that contain only numbers. This increases the likelihood that an attacker succeeds with a brute-force attack. The successor to WPA, called WPA2, is supposed to be safe enough to withstand a brute force attack.
Use of Location Services
Location services are heavily used by social media, navigation, web browsers, and other mobile - centric applications. In terms of organization security, mobile devices with location services enabled are at increased risk of targeted attacks because it is easier for potential attackers to determine where the user and the mobile device are.
This situation can be mitigated by disabling location services or by prohibiting use of location services for particular applications such as social networking or photo applications. Users may also be trained to turn off location services when in sensitive areas. However, a similar problem can occur even if GPS capabilities or location services are disabled. It is increasingly common for websites and applications to determine a person’s location based on their Internet connection, such as a Wi-Fi hotspot or IP address range.

Attacks based on the GSM networks
The base technology of most cell phone networks in the world – GSM – has been known to be weak for years. Consequently, standardization bodies and equipment manufacturers have invented and implemented security features to protect cell phone users from simple attacks.
The GSM network encryption algorithms belong to the family of algorithms called A5 - stream cipher. It is implemented very efficiently in hardware, design was never made public. There are 3 different versions of A5: A5/1 a strong versions, A5/2 a weak version and A5/3 based on algorithms used in 3G phones. These algorithms can also be cracked fairly easily. By analysing the output of A5/1 for 2 minutes it can be cracked in less than a second. The weaker A5/2 algorithm can be cracked in milliseconds.

Interested in mobile security?
- Mobile security threats
A mobile phone user is exposed to various threats when they use their phone. Recent research shows that mobile security crimes have grown by 261%, according to ABI Research. - Smartphone security
We trust our smartphones with our most precious information – personal pictures, text messages, and emails. But are they really worth our trust?