How to increase your Smartphone security?

Smartphones and us
It is hard to imagine life without smartphones. When Smartphones were first introduced, features like calculators, calendars and notepads seemed amazing. Today people use them for all kind of reasons – calling, browsing, streaming videos, playing games etc. Our phones are getting larger in size and more powerful every year. It won’t come as a surprise if one day laptops and desk PC-s would disappear, leaving an army of these multipurpose mini-computers in our pockets. We trust them with our most precious information – personal pictures, text messages, and emails. But are they really worth our trust?
Security concerns
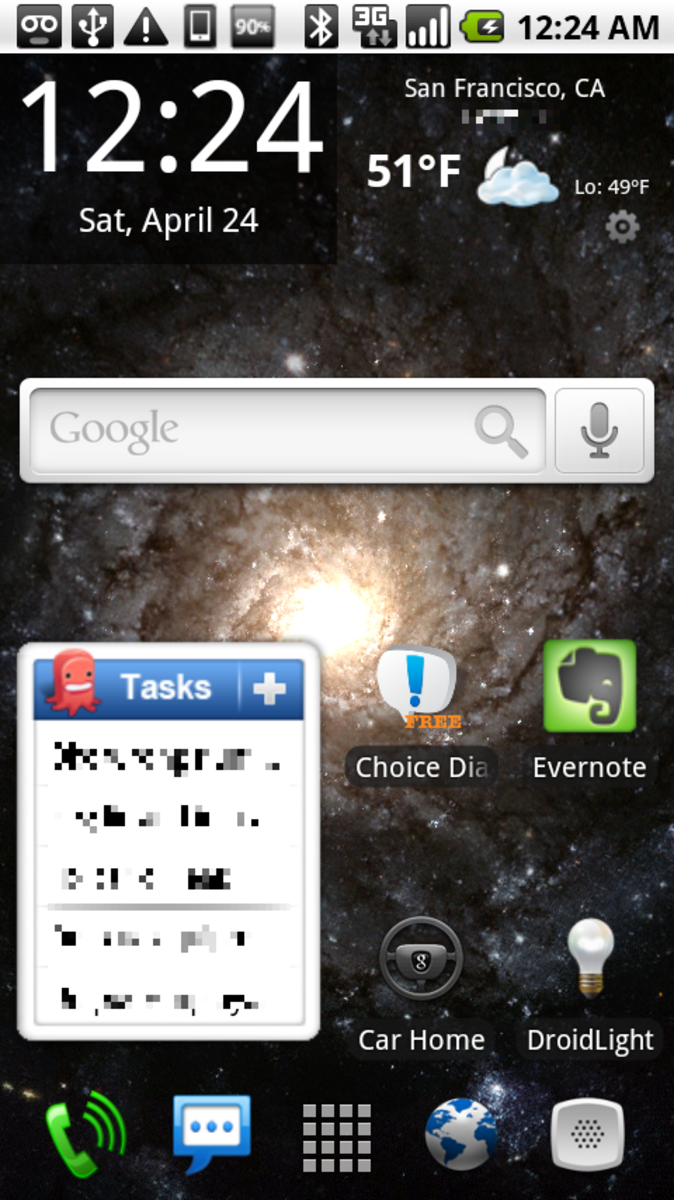
Smartphones are mini computers, even though they are not as powerful as some modern PC-s. Consequently, there is a high interest in breaking these easy-to-crack devices. The main concern is data confidentiality – making sure your personal information will not get in the wrong hands. Due to its architecture smartphones are both secure and vulnerable to malware and other threats. For example, Apple iOS offers good protection against malware attacks but is only moderately good at isolating applications. Android, on the other hand, runs applications in full isolation, which restricts their ability to inappropriately interact with sensitive systems, as well as other applications.

Human factor
Human factor is important in all stages of security threats. It is often the user, who allows certain attacks to take place and compromises device security measures. A lot of effort has been made to increase user awareness on the topic of information security. Importance of such awareness is especially high in case of BYODs (Bring Your Own Device), when companies allow employees to access network with their own devices. To name a few, issues such as attacks via wireless networks, malware and Trojans, spreading through downloaded games or stolen devices have huge potential risks. It is therefore understandable why network administrators are under high pressure in dealing with all those potentially infected devices on their network.
Phones are actually safe
Analysis of different sources has shown that Android phones are preferred much more as targets, mostly because their number of users is higher than iOS users. Thanks to sandbox architecture of Android and process isolation the risk of infection is minimized. However, users tend to compromise security by installing third-party applications like games without taking notice of information being required and accessed by particular application. We cannot realistically talk about data confidentiality until users are continuing to ignore such threats. The best advice that could be given in such circumstances – being sceptical about installing another third-party application.

Nothing is FREE
It was surprising to find out how many threats are out there that most users do not even know about. Especially popular among many users is free Wireless Internet offered almost everywhere we go. Countless smartphones connect to these networks every day without knowing of potential threats hidden behind this FREE service. Assuming your phone is by default secure creates additional problems – users often do not enable passwords or use the same password for all their accounts. In case phone is stolen there is no way of protecting the data on it.
Preventive safeguards
Preventive safeguards should be implemented in every device and any network, where information contains sensitive data, like personal pictures, passwords, bank transactions etc. These include using antivirus software, verifying every application installed, monitoring device performance and keeping system up-to-date. Ideally, risk analysis should be done in order to identify main threats for certain networks and users (e.g. in one company). Considering it is highly time and resource consuming, there is no better way than making sure only company-owned devices with restricted user rights (not allowing install third-party applications) are allowed to be used on the network.
Final note
Mobile security is a relatively new issue – smartphones have gained in popularity during last 5-7 years. However, the speed of growth and development is impressive, latest phone today will be out of date already in about 6 months. That is why security threats and attacks are only relevant to today’s mobile phones. In order to meet the challenges of future generation security issues we need to think ahead of our time and predict potential future threats.
Interested in mobile security?
- Most common attacks on mobile phones
Cybercrime is worth big money. So as people move away from using PCs and toward smartphones and tablets as their primary computing devices, digital crooks have taken note. - Mobile security threats
A mobile phone user is exposed to various threats when they use their phone. Recent research shows that mobile security crimes have grown by 261%, according to ABI Research.