There Oughta Be A Law!
For What It's Worth

Shout it out with a megaphone

Security Breaches
With the rash of security breaches we have heard about on the news where companies have not notified the public until weeks, sometimes months after they've been hacked, you would think there oughta be a law "requiring" them to do so ... or else!
It is bad enough that we hear about it after the fact. What really stings is that, as their loyal customers, they didn't think we mattered enough to let us know about the intrusions in a "timely fashion" so we could get on the ball and start being more vigilant.
Many people just pay their credit card bill each month and don't even look at the charges on their billing statements. While that's not so smart, these are also the very same people who will cry out the loudest: "Why didn't someone tell me that my credit card data was stolen?"
Believe it or not, there is a vaguely written law on the books that requires the Attorney General to be notified of all breaches that affect 500 people or more.
I guess that means if the breach affects less than 500 (unlucky) people, we may never hear about the incident to know if we were included in that number. We certainly all can't count on a personal notification.
You might ask, "Well, Rachael, what can we do, even if they did tell us about the hacking incident?"
There are measures that consumers can take as I outlined in my article "How to Protect Yourself After A Security Breach or a Hack."
While it is true that we may never win the war, but at least we can win a couple of the battles.

Chinese Hackers Arrested
In May 2014, the FBI announced that they indicted five Chinese hackers for "economic espionage" - for spying on American companies.
According to the FBI, they are only the tip of the iceberg. There are home grown American hackers, Russian hackers, Syrian hackers, Italian hackers, and Nigerian hackers with more being trained and polishing their cyber-skills every single day.
Introducing: The EINSTEINS
The original Privacy Impact Assessment (PIA) for EINSTEIN 1, dated September 2004, explained that EINSTEIN 1 analyzes network flow information from participating federal executive government agencies and provides a high-level perspective from which to observe potential malicious activity in computer network traffic of participating agencies' computer networks.
EINSTEIN 2 incorporates network intrusion detection technology to alert the United States Computer Emergency Readiness Team (US-CERT) of the presence of malicious or potentially harmful computer network activity but only in federal executive agencies' network traffic.
Similar to EINSTEIN 1 and EINSTEIN 2, EINSTEIN 3 enhances cybersecurity analysis, situational awareness, and security response and is only able to detect malicious traffic targeting Federal Government networks, but also prevents malicious traffic from harming those networks.
- quote from The Department of Homeland Security website
Department of Homeland Security To The Rescue?
The National Protection and Programs Directorate is part of the Department of Homeland Security (DHS) and they are offering the use of two of their three "EINSTEINS."
Up until now, this agency only worked with other federal agencies in providing a "situational awareness snapshot of the health of the federal governments' cyber space." I'll attempt to explain some of that doublespeak in a minute.
Now they want to get involved in helping protect private businesses against breaches, especially medical facilities and health-care providers - because they have done such a bang-up job in requiring all of them to go "electronic" with patient records.
Einstein 1 and Einstein 2
The official website language is in the sidebar but here's the plain language version.
EINSTEIN 1 is programmed to detect and collect network security information and work with the affected participating federal agency to address (not fix) the portal of the threats and vulnerabilities.
But this is only done with federal agencies who voluntarily participate in their program.
After the breach, it is up to that federal agency to share findings with the public. (Obviously they do not have to adhere to the same rules as private sector in reporting breaches to the Attorney General.)
EINSTEIN 2 is programmed to analyze and watch traffic for cyber threats and improve and share "situational awareness" with the participating federal agencies to prevent future network vulnerabilities.
EINSTEIN 2 is not programmed to locate the threat.
Its job is to identify that there is a cyber threat and help prevent it from happening again. EINSTEIN 1 collects and tells the agencies how the threat got in.
These are your tax dollars at work, folks. Does it sound like a bunch of garbage to you?
Well, it does to me.
Simplified, it takes two EINSTEIN computers to do the job that a $100 Virus Protector and $50 Malware Protector can do on one computer.
With all the technology available (not to mention our tax dollars), why can't our government step up their EINSTEINS to be more pro-active and actually FUNCTION like a computer instead of masquerading like one?
It is no wonder there are so many breaches in government and health care networks.
After all these years, with only participating FEDERAL agencies as members in EINSTEIN programs, where does that leave everyone else?
It doesn't take an EINSTEIN to figure it out.
We are in the same place we have always been - on our own.
Many states have a system or laws that itemize steps to notify consumers of data breaches.
But there are states who have no laws on their books to require them to notify consumers at all.
One way, but certainly not the only way, any of them will come into compliance is if there are strict penalties for failure to notify consumers within 24 to 48 hours of the breach.
The Government Thinks Cyberinsurance Is The Solution
The Department of Homeland Security thinks that among other benefits, cyberinsurance will protect the companies against lawsuits from the public.
According to one online columnist, cyberinsurance can include the following coverage:
- company costs for data breach notification to customers
- protection from liability due to employee breaches because of illegal use of consumer data
- providing free credit reporting benefits to customers
- protection against third-party claims for class action lawsuits.
Cyberinsurance doesn't do a thing to beef up their security. And it does nothing to aid the average consumer.
If anything, cyberinsurance will make hacking more profitable to the hacker because insurance covers the company's butts. The hackers will think it is a free ride since everyone's bases are covered.
Hacking will be viewed even more as a victim-less crime.
If EINSTEINS become involved in the private sector's security and in regulating cyberinsurance, one can only cringe at how long it will take and how well it will perform.
When the healthcare sector was ordered to make all their medical records electronic, they were given attractive monetary incentives (thousands of dollars) to become compliant within 24 months or else be fined. In other words, they had to be bribed to do it.
Between employees taking work home with them on flash drives and laptops being left in car trunks, the breaches have increased a thousand-fold.
And those are just the breaches the public is told about.
One can only imagine how much each company in private sectors will be paid to ready their network systems for cyberinsurance compliance. If the EINSTEINS are overseeing any part of this, it's not going to be pretty.
It's going to be expensive.
Target Security Breach
Child Aspirations
Children will be answering their mothers about what they want to be when they grow up:
"I want to be a doctor!"
"I want to be a lawyer!"
"Doctors and lawyers work too hard. So I want to be a hacker!"
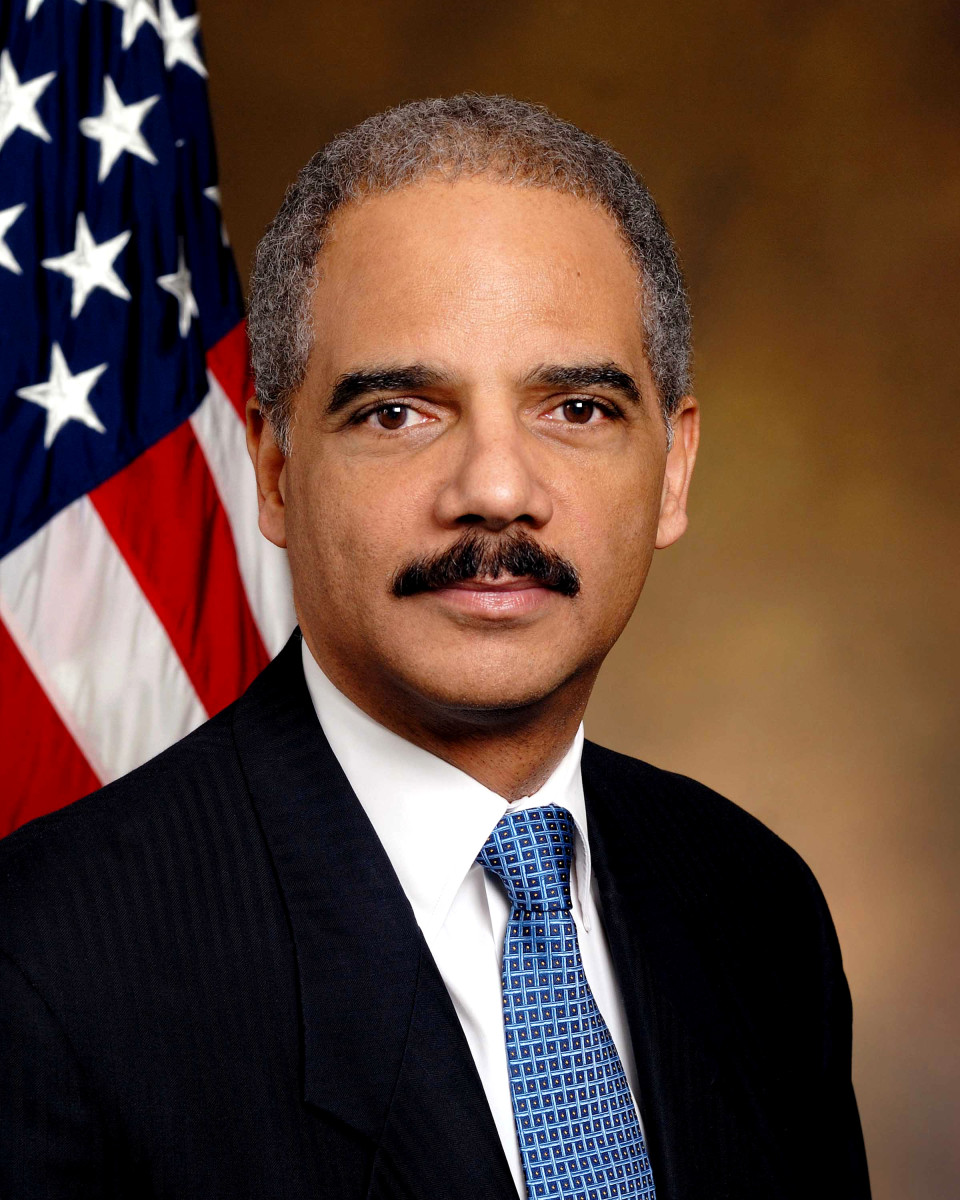
The Attorney General, Eric Holder
Since all breaches affecting over 500 consumers must be reported to the Attorney General's Office, Eric Holder, the present Attorney General, published a press release on February 24, 2014.
In it, he urged Congress to create a "strong, national standard for quickly alerting consumers whose information may be compromised by cyberattacks."
You can read the entire press release at the United States Department of Justice website.
Today is July 7, 2014.
It's only been a few months since his February press release as to what the American people "need." It just goes to show you, no one listens to him either.
If companies are not held accountable for delaying reporting time to the Attorney General and US Secret Service, the public will always be in the dark about breaches and the extent of them.
It's not fair.
Playing Devil's Advocate
What if .... President Obama, Mrs. Obama, Vice President Biden, Mrs. Biden and at least three Supreme Court Justices all had their personal identifying information hacked from their tax returns and put in the wind.
I chose tax returns because we can't rely on their credit card data being hacked due to the fact that these are people who don't really PAY for anything with the perks they get.
So maybe if their data was accessed from their tax returns, maybe then the squeaky wheel will get the grease.
Maybe laws will change and actually be enforced.
It really shouldn't take someone high up on the chain of importance to be affected by a breach for things to change in this country.
But I think it needs to come to that for any significant changes to go into effect.
My Two Cents: Size Doesn't Matter
I think any company who is aware of a breach or hack who does not notify the public within 24 to 48 hours of the incident should be fined $1000 per affected consumer PER DAY. (Fine to be adjusted per inflation!)
Regarding the law mentioning only if 500 or more consumers are affected: I think maybe companies feel since the present law is so laissez faire', that they don't need to take breaches seriously enough to notify the public.
So, I would like to see the "500" part deleted from the law.
500 people or 5 million people, size doesn't matter. We are all affected in some way by a breach.
We are real people, not just numbers on a credit or debit card.
Chime in with your two cents by leaving a comment.
© Rachael O'Halloran, July 7, 2014
© 2014 Rachael O'Halloran