Hack Report: P F Chang's China Bistro and Subsidiaries
Published June 29, 2014
by Rachael O'Halloran
IMPORTANT UPDATE: July 1, 2014 and August 5, 2014 at end of this article.
Data Breaches = Hacked Accounts

Notifications
Lately, I have been losing a lot of faith.
Oh, not in God .... just in people and technology. I'll tell you why.
There have been companies who reported to the Attorney General or who have been notified by the United States Secret Service that they have had a "data breach" - in other words, they've been hacked - but they choose to wait a couple of months to file the actual report with the Attorney General's office in their state. After learning of it, many choose not to notify the public.
Some companies don't even bother reporting it at all, which I just don't "get." In my opinion, there should be hefty fines in place for non-compliance, so that they must file a report. They are putting the public at risk by denying them the knowledge that their information has been compromised.
They have reasons for not complying, almost all the reasons are financial and reputation oriented.
Watchdogs who learn of breaches have been the heroes for notifying the public of the data breaches.
On the flip side, you have companies who have been hacked (yes, they actually hate that word and that's too bad!). Their spokesperson makes public statements for their company that minimizes the actual damage or extent of the breach. Often they "fudge" on the actual breach dates, either intentionally or because they haven't done enough homework to see how far back the breach dates.
In other words, they glossed over it.
I don't like "glossing over" tactics.
In fact, I hate them!.
These companies make me mad. If they don't think enough of putting out an "All Points Bulletin" to notify the public that their databases, credit card networks, etc. have been compromised (i.e. Hacked), then I will.
In an effort to air as much of their dirty laundry as possible, I have decided to create my own "Hacking Report."
This is the first report of many and I will keep updating them as more information or solutions become available.
Feel free to SHARE this article, but please do not copy it.
Use the share buttons on the right side of your screen if you want your friends on social networks to read this article.
If you want to email your friends the link, use this one:
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
Definition of Data Breach
Even if you have not been a visitor to P F Chang's China Bistro or their other restaurants, this report still has important information in what exactly happens to your credit or debit card data when it has been stolen from an establishment in some manner or if there has been a "data breach."
Data Breach
"Data breach" is a information technology, governmental and finance term meaning "your personal information has been hacked."
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
P F Chang's China Bistro

P F Chang's China Bistro Breach
Dates of Breach:
P F Chang said they learned of it on June 10, 2014 when they were notified by the United States Secret Service. But by the end of the second week in June, the agency said the breach spanned from March 20, 2014 to May 30, 2014. Now it is the end of June and published accounts state that the dates are far more long range than originally reported. The dates are now September 18, 2013 through June 11, 2014
Date of Report:
June 12, 2014
Number of People Affected:
An "estimated" 2 million credit card accounts, which includes all patrons who visited any of over 65 US based P F Chang restaurants, over 40 international locations, their 66 Flemings Steakhouse locations or 20 of their fast food chain "Pei Wei" for a total of over 190 locations.
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
One of the many duties of the United States Secret Service is to investigate breaches of counterfeit debit and credit cards.
P F Chang's data breach has the potential to become a rather large breach given the total number of locations P F Chang's owns, the fact that their payment systems are linked and that an "estimated" 2 million credit or debit cards are involved. There could be more.
I'm a bit peeved with the wording of the company's initial statement because I feel it can be taken two ways and is rather misleading to the public.
Read the following statement and see what conclusion you come up with. I provided you with the link under the screenshot to show you that I didn't alter the quote and so you can read more of the company's statement.
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
P F Chang's Spokeswoman's Statement
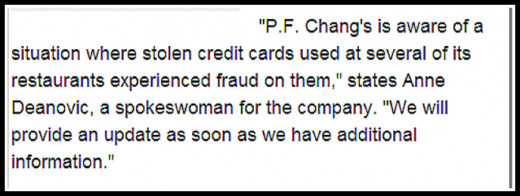
"Where stolen credits cards were used at several of its restaurants experienced fraud on them"
Did you arrive at the same conclusion as I did? Did you take the statement to mean ...
Wording of P F Chang's Statement
Thank you for answering the poll question.
To me, the statement implies that there were stolen credit cards used at their restaurants when in fact, the credit card data was stolen from their network, not the other way around.
The wording "experienced fraud on them" is just an odd choice of words in any vernacular, in my view.
To the average reader, the statement that "stolen credit cards were used at several of its restaurants and experienced fraud on them" could mean that P F Chang's got stiffed for their bill when someone used stolen credit cards at their restaurant.
You can see how a few words can change the total meaning of the incident.
To be clear: If you used your credit or debit cards to pay your food check at any P F Chang locations or their subsidiaries, be aware that their network has been hacked. All credit and debit card data has been compromised (stolen).
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
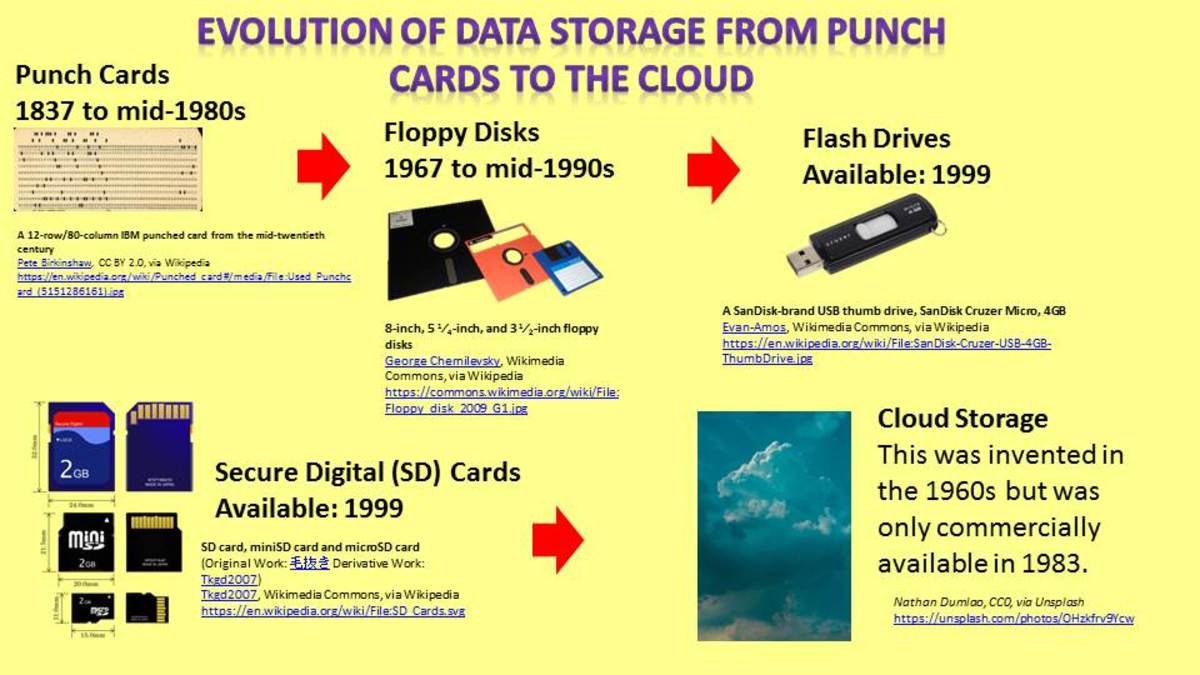
What Happens After Your Data Is Stolen
Several online security experts, whom I follow as subscriber to their blogs, strongly feel and in the last couple of weeks have provided proof that there might be a connection to the November 2013 breach of 40 million credit cards stolen from Target and 282,000 from Sally Beauty Supply Company because many of the stolen credit and debit cards from P F Chang's network breach have already been offered for sale online at the same underground credit card website.
1. The website "Rescator" is a black market site that sells stolen codes from credit card magnetic strips either individually or in bundles called dumps. (see photos in the sidebar)
- On June 9th, Rescator started advertising (for sale) thousands of newly acquired (stolen) debit and credit cards. An "investigator" gained access to their forum, purchased some of the cards and they have now been verified to have been used at P.F. Chang’s locations from March 20 to May 30, 2014.
- According to the investigator who made the purchase, Rescator is using the tag "Ronald Reagan batch" to identify this load of cards.
- On June 10th, P.F. Chang's received a warning from the U.S. Secret Service that its network may have been compromised. There's no proof it was the same hacker. It could have been just a coincidence of timing. But I doubt it; I'm not a believer in this type of coincidence.
2. Rescator guarantees valid cards. The card numbers are worth more shortly after stealing them, before the fraudulent transactions start getting noticed at Points of Service and before banks and consumers become aware that their card has been breached.The longer Rescator holds on to them, they risk the cards getting flagged at Points of Service, making them worthless to their buyers.
- The way they validate them is they do test purchases on batches of cards (usually on internet) to make sure the cards are accepted and that the charges go through.
- With this knowledge, they are able to validate 100% that the cards are usable. The higher the validity rate, the more reliable the seller's reputation and the higher price he can get for the card. If the card proves not to be usable, the buyer is given a credit toward another card, but no refund. However, word gets around fast if someone's purchase was flagged and it is only a matter of time before more cards are flagged in that "batch."
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
Company Website
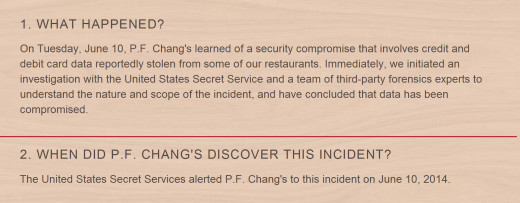
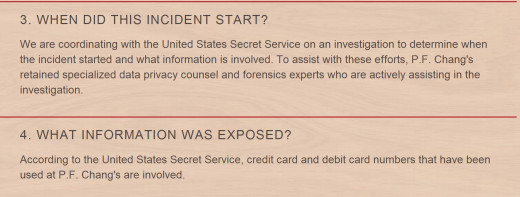
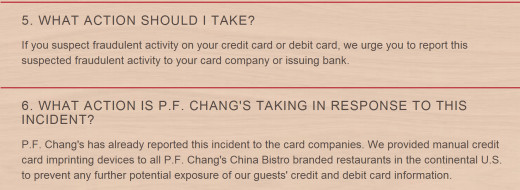
In my screenshot photo below of what P F Chang put up on their website to answer security concerns, please note #1 where they say "credit and debit card data reportedly stolen from some of our restaurants."
Then note #8 where they say "we do not yet know which credit or debit cards may be involved. P.F. Chang's has notified the credit card companies and is working with them to identify the affected cards."
P F Chang's Security Page
Fleming's Steakhouse & Wine Bar

Fraud Spikes
P F Chang's spokeswoman said that "the payment card industry is closely monitoring cards used at all three restaurant chains for signs of fraud. So far no fraud spikes have been noted."
- That means that no credit card agency has reported them being used to rack up charges.
- My thought is -- if you don't know which cards were stolen, then how would you know which ones to be on the alert as being used fraudulently?
If a fraud spike starts, it will make the thief have to sell the cards very quickly to get the most amount of use out of them before they are flagged by the credit card companies as stolen.
If Rescator's "Ronald Reagan batch" indeed contains P.F. Chang's data, incidents of fraud will soon spike when real card owners report charges on their bills that are not their purchases.
- There are 1,650 Ronald Reagan cards being advertised for sale on Rescator, priced from $18 for a prepaid Visa debit card to $140, based on card types and credit limits.
- UPDATE: On June 15, 2014, Rescator site began listing for sale bulk discounts of 100 dumps ($2,000), 200 dumps ($3,500), and 300 dumps ($4,500).
They are trying to get rid of them fast.
It is still not clear HOW the card data was stolen from P F Chang. It could have been done the same way it was done at Target when malware was implanted at the point-of-sale terminals that grabbed data from cards as soon as they were swiped, and before the information was encrypted. Or there could have been a physical hack into their payment network.
The United States Secret Service is still investigating this case. As it is updated, so shall this hub.
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
Pei Wei Asian Diner

P F Chang's Solution
As of this writing, the P F Chang stopped swiping cards on Point Of Service terminals and are now doing business "the old-fashioned way" -- with manual imprinting machines for each credit card. They feel that this will make customers feel safe when using their credit cards at their establishments.
Now all they have to worry about is the carbon paper copies.
However, this is not the best solution because credit card companies stopped making embossed cards after learning that the raised lettering on credit cards was easy to duplicate to create stolen cards. So the new embossed cards can only be swiped through a card reader, not a manual imprint machine.
If patrons can't use their credit cards, I guess they better get acquainted with cash.
Or eat at home.
~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*~~*
Were you affected?
Were you a customer of any of the P F Chang restaurants (Fleming's, Pei Wei) during the breach dates of September 2013 to June 2014?
UPDATE: July 1, 2014
According to securityweek.com, P F Chang's China Bistro has been hit with a class action lawsuit due to the above reported security breach at their restaurants.
The lawsuit was filed on Thursday June 26, 2014 in US District Court in Illinois by John Lewert, an Illinois resident seeking monetary and statutory damages. He claims that around April 3, 2014 he used his debit card to make a purchase and that by using that debit card, it he had an "implied contract" with the restaurant that they would protect his debit card information. The data breach, he said, violated the contract by exposing his personal information.
It is interesting to note that this lawsuit says that P F Chang's has confirmed the breach of at least seven million debit and credit cards, whereas the report I read to write this article approximated the number at two million.
As I said earlier in my article, this breach has the potential to go large and I don't believe we have heard the end of it yet. This is just one class action lawsuit involving undetermined number of litigants because it is still collecting information from those affected.
You can read the 18 page complaint here but the gist of it is that the lawsuit is asking for a JURY TRIAL as well as:
- Ordering P.F. Chang’s to pay actual damages to Plaintiff and the other members of the Class;
- Ordering P.F. Chang’s to pay for not less than three years of credit card monitoring services for Plaintiff and the other members of the Class;
- Ordering P.F. Chang’s to pay punitive damages, as allowable by law, to Plaintiff and the other members of the Class;
- Ordering P.F. Chang’s to pay statutory damages, as provided by the Illinois Consumer Fraud and Deceptive Business Practices Act and other applicable State Consumer Fraud Acts, to Plaintiff and the other members of the Class
- Ordering P.F. Chang’s to disseminate individualized notice of the Security Breach to all Class members and to post notice of the Security Breach in all of its affected stores;
- Ordering P.F. Chang’s to pay attorneys’ fees and litigation costs to Plaintiff and the other members of the Class;
There are more but those are the highlights. Number five is the one that will literally destroy this company by having them destroy their own reputation. It asks that the company post notices in all their "affected" restaurants (I'm assuming subsidiaries as well) to let the patrons know of the security breach - which they will probably be reading as they stand in line waiting to be seated!
Anyone interested in joining this class action lawsuit, please contact:
Joseph J. Siprut EMAIL: jsiprut@siprut.com
Gregg M. Barbakoff EMAIL: gbarbakoff@siprut.com
Gregory W. Jones EMAIL: gjones@siprut.com
OR
Regular Postal Mail, Address your inquiry to:
SIPRUT PC
17 North State Street
Suite 1600
Chicago, Illinois 60602
PHONE: 312.236.0000
FAX: 312.267.1906
Update: August 5, 2014
SC Magazine is reporting that P F Chang's security breach of June 2014 was only affected at 33 of its locations and not all of its locations, as they previously had thought. Read more at the link.
Rachael O'Halloran, June 29, 2014
© 2014 Rachael O'Halloran