Internet Safety: Safe Surfing and Securing Your Devices
Previously I discussed the programs one should have on one's system, and that one should keep them up to date, as in as soon as you learn of an update, download and install it. Here I'm going to write about actions you can take to increase your security - and some of these may depend on software, others hardware, others maybe just common sense. It's all about further improving security and safe surfing.
Set up a limited user account on your PC
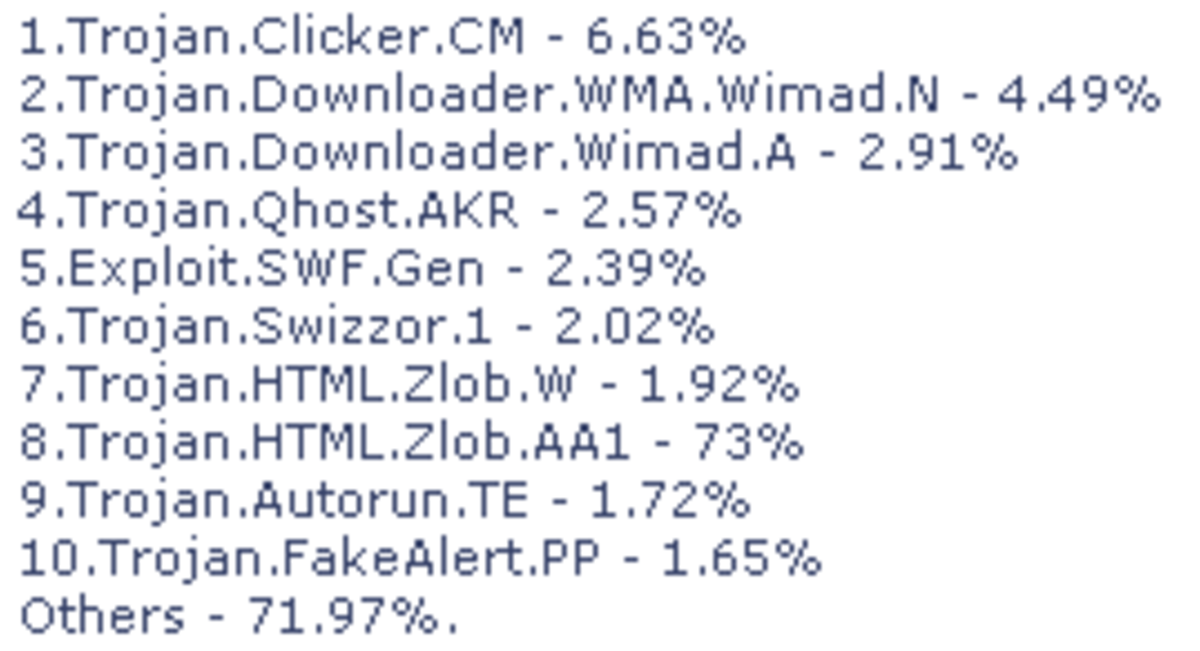
Especially if you are using older versions of Windows, like XP, it’s important to set up limited accounts, and not to rely on administrator accounts. Because if you’re online and happen to come across some malicious program that gets on to your system, it can do greater damage if you’re running an admin account because it has practically unlimited access. A limited account typically lets you do the usual things you would do on your PC, but the installation of software and drivers will be restricted, for instance, thereby decreasing the chance or at least the effects of infection.
Windows Vista and Windows 7 have UAC, or User Account Control, which will help ensure that you’re the one doing the installing of software and nobody/nothing else. So even if you are running an admin account, you’re less vulnerable. But the experts still recommend setting up a limited account in any case.
Setting up limited accounts also allows other people to use the computer and access their own files and do work, but prevents them from accessing your files and having full admin access over the entire computer with other people's work and potentially private information.
"If you’re online and happen to come across some malicious program that gets on to your system, it can do greater damage if you’re running an admin account because it has practically unlimited access."

Did you know?
The US military strictly forbids the usage of media such as CDs, DVDs, and removable storage devices.
Lock down autorun
Autorun worms spread via media such as CDs, DVDs, removable storage devices like flash drives and external hard drives. Plugging your flash drive in to someone else's computer may infect it with autorun malware.
There are a few steps you can take to reduce the risk of infection here. First protect your flash drive. There are programs like Flash Disinfector or Protect My Disk which will do this. You should preferably run such a program with a new, uninfected flash drive to help prevent it from being infected in the first place.
You can also disable autoplay in Microsoft Windows. Autoplay and autorun are not the same thing but they do similar things. You can create dummy autorun files on your system, too, but this can be a complicated process although there are tools that will do this for you. Flash Disinfector is one of them.
It might also pay to scan CDs, DVDs, and flash drives before using them to see if any autorun malware is found on them. Then appropriate action can be taken, such as quarantining the threat or disposing of the media if necessary.
Check your browser settings
After a session of surfing, it’s a good idea to clear your history, cookies, and cache from within your browser. While cookies aren't inherently dangerous, if they were to fall in to the wrong hands, scooped up by spyware, that could be potentially problematic. You can also use a browser’s private surfing mode so you can be somewhat more anonymous online. Most modern browsers have this feature. Also make sure to check your cookie settings, particularly when it comes to third party cookies, and make sure your browser is set so that websites may not track you. In Internet Explorer, also lock down ActiveX.
Also use HTTPS wherever you can. This is a form of encryption and prevents sensitive data from being gleamed through eavesdropping attempts. You will also receive HTTPS cookies from websites which are encrypted.
Extensions like Noscript, Adblock Plus, and HTTPS Everywhere for Firefox are a must. Also use browser virtualisation software like Sandboxie, or one that might be bundled with an internet security program like Zonealarm's Forcefield. This is especially important if you have multiple tabs open at once in your browser. Don't have multiple tabs open when carrying out activities such as online banking.
"Use HTTPS wherever you can. This prevents sensitive data from being gleamed through eavesdropping attempts."
Scan or look up websites before you visit them
Google will inform you of sites that might harm your PC, by adding them to a blacklist. The owner of the site or blog will have to clean their site before Google will take it off that blacklist. This can often happen due to malicious code which has been written into a seemingly harmless widget that the owner will willingly and unwittingly put into their blog or a website has been hacked to serve malware. Other times malware on a person's computer can end up infecting their own websites. You can check Google diagnostics pages of websites to see what's going on, whether they're infected, and details on the infection.
You can also try websites like Sucuri to scan websites to see if there’s anything malicious on them. They will also list references such as Norton Phishtank among others that will say whether a site is safe or not. VirusTotal also has a URL scanner. It’s highly recommended that you scan your own blogs and websites every now and again, too. You can check your Google Webmastertools account for this if you have one.
WOT, or Web of Trust is a community that ranks websites and will indicate whether they've had any bad experiences while visiting a particular website. There are also notices that indicate that a website has been involved in the distribution of malware. That way, even if the website scanners like Sucuri don't find anything, someone else might say otherwise and know it from personal experience.

Your surfing habits
You want to keep the computer that you access your most important accounts from as clean as can be. So avoid surfing adult sites (very few of them are really ever safe), torrent sites, warez sites and the darker places of the web - not only because it's potentially dangerous for your PC, but depending on the content downloaded, it may be illegal. If you must do these things, then do it from another computer and try to keep the data transferred from that PC to others to an absolute minimum. You don’t want it spreading an infection to other systems.
A little bit of safesurfing and common sense will stop you from stumbling in to some nasty parts of the web. Stick to trusted, reputable websites - this is the best advice.
Phishing sites
People fall for phishing scams every day. They’ve been around forever. Someone will send you an email, and you’ll see a message asking for your banking details, and the like. You NEVER reply to these emails. It’s a phishing scam. You can usually tell which emails are going to be spam or scams by reading the header, and who it’s from. If it’s a name you don’t recognise, or if the header doesn’t look like it has anything to do with you, don’t even open it, and certainly don’t open any attachments within it either, as this could have dire consequences for your system.
Always make sure you’re dealing with the real deal and not some phishing site, which is intentionally cloned to look like the original. Don’t enter a website unless it’s on the first page of the search results. Rather use a bookmark or type an address in the URL field, than use a link in an email, or clicking a link somewhere else. Check to see if the website uses HTTPS, which is an encrypted, secure connection. In fact, if you have the option to use HTTPS on a website, like Twitter, then consider using that instead of just plain old HTTP. If a site’s security certificate is outdated or non-existent, then beware – it might be a phishing site. Either way you should reconsider logging in to the site until the issue is rectified. Perhaps inform the webmaster too, if it's a website you trust. It should be said that not all sites utilise HTTPS though - but the most important ones should.
Use URL unshortening services
A lot of links posted on social networking sites like Facebook and Twitter lead to malicious websites. Use getlinkinfo.com, a website that will unshorten URLs commonly posted on social networking sites. If it's not a website you know of, or the link is sent by a person you don't know or trust, then avoid it. You can either ignore it, or just report that person for spam. It's not uncommon however, for someone to have their Twitter account hacked, and then all their followers spammed either through mentioning them using the @ symbol and their name, or even sending them a direct message. The same could happen anywhere else.
Another place where shortened links crop up is in your blog visitor stats like in Blogger. This is often referral spam and you must not follow these links at all.
"A little bit of safesurfing and common sense will stop you from stumbling in to some nasty parts of the web. Stick to trusted, reputable websites."

Watch out for identity theft
Needless to say, as an individual you should really consider not using your real name online unless it's crucial - such as filling in information inside your online banking account. This goes for your details too. At the very least, never put your street address or your personal phone numbers online. And you may want to consider not putting your personal email address in public too.
Information that can be used to personally identify you or lead to identity theft should not be put online, at least not publicly for all to see. Some, such as writers, may want to use their real name to establish their brand. If they want to take the risk, fine - but street addresses, social security numbers, and phone numbers are out. A business address or a business number are usually fine, however. P.O. boxes are okay, too. Also beware of putting information out there about family, pets, location etc, that someone may harvest from your social networking profiles or favourite hangouts to try to learn more about you, your habits - online and offline. Stalking is fairly easy nowadays when people put all their info out there for all to see - stuff that they might not willingly talk about in the real world. Always assume that a stranger might be reading.
Always be careful of what you fill out in your bio on a website like Facebook, and restrict who can actually view your profile and photos, etc.
Some internet security programs have features that will scan the web for cases of identity theft. This is when someone uses your name or details for nefarious purposes. For example: someone uses your name, details and the like to start up a Facebook profile. One way of doing this is if you have a Google account, to set up custom Google alerts, which will notify you via email if your name, details and personal information crops up online. Then you can take appropriate action such as getting Google to deindex the pages, get the pages taken down, and possibly notify the authorities who deal in cases of cyber crime. It pays to search manually for your details and the like too, occasionally, but only do so using Google encrypted search.
"Always be careful of what you fill out in your bio on a website like Facebook, and restrict who can actually view your profile and photos, etc."
Make regular backups
To ensure that your precious data that you have on your HDD isn’t infected, stolen, or lost in the event of a virus or something malicious, make sure to backup frequently.
Use DVDs, flash drives, or other devices to store your information, projects and things you can’t live without. You might also consider secure online backups. Also make sure to make system restore points on your system too, which can possibly help reverse your system to a functioning state.
Do regular anti-virus scans
It’s always important to do scans not only of your PC, but other things too: like removable devices such as flash drives, external hard drives and CDs, DVDs, and so on. This way you will spot something potentially dangerous before installing it or copying it on to your HDD.
Some programs like MBAM (Malware Bytes Anti-Malware) will offer to run a quick scan of your system, which will look for spyware and/or viruses in the most common places they tend to hide if on a system, such as the registry, memory, startup processes, running processes, autorun entries, and your Windows/system folders. Do one of these every day or every other day. Then do a full AV scan at least once a week. This is to ensure you catch something potentially malicious early, before it’s too late.
Downloading files
When it comes to downloads, scan them for viruses and spyware, too. Only download programs from trusted websites and the like. Be careful about going to a dodgy website, or a “mirror” – a website that also has the program or file for download, which has more chance of being infected. Get it from the official site if at all possible, or a trusted website. Files will often be hosted on Download.com or SourceForge and the likes. These are usually fine. But be careful of some site or blog you’ve never heard of, particularly - dare I say it - foreign websites that have text in a language you don’t understand.
Opening files
If the files are pictures or videos, make sure that they are indeed media files, before you double click them. See if you can view the contents in thumbnail mode, depending on what OS you’re running. If it’s a file type you don’t recognise, be careful opening it. Scan it, even analyse it, look it up online to see if anyone else has something to report on it, before trusting it. Also make sure that Windows is set to list items with extensions. So if you see something called "example.jpg.exe", then do not run it. Be wary of files with .exe extensions, particularly if they crop up in your emails. You can use Sandboxie to isolate your media player or email client from the rest of your hard drive. so if anything malicious tried to worm its way on to your PC, it would be trapped inside the Sandbox, which you can then empty, and the threat is shut down.
Now chain emails are fun, but they can pose a threat to your system. An email will be sent from system to system over the web, and it could pass on an infection that’s been on somebody’s computer or laptop. Get an internet security program that has an email scanner, and set it to scan incoming and outgoing emails. Then emails will be checked for threats before you open them, or the attachments therein. Don’t open emails or attachments from someone you don’t know personally, or have no business with.
Also when sending chain emails, or any email, make sure to use the BCC field instead of CC, otherwise anybody can see the recipients’ email addresses, and one should be cautious about who knows their personal email addresses. Hackers have long relied on email as an indispensable tool to distribute malware and perform other illegal practices.
"To ensure that your data that you have on your HDD isn’t infected or lost in the event of a virus, make sure to backup frequently."
Send files for analysis online
You can also send files to sites like VirusTotal to have them analysed in the cloud, online by a multitude of different anti-virus programs. So any suspicious files can be sent here. If a detection ratio is 0, you probably have nothing to worry about. But guaranteed the detection ratio is usually 1/45, or however many AV programs have scanned it. Reason probably being because at least one of those AV scanners has detected a false-positive. If it’s reported as infected by several, most or all of them, get rid of it.
Another popular service is Jotti, but this is recommened for users using Linux based operating systems, mainly.



Secure your routers and Wi-Fi devices
Using wireless devices can be hazardous for several reasons. If the device isn’t properly secured, you can risk someone coming along and stealing sensitive information just by sitting outside your house in a car with their laptop and a few programs.
Make sure you set up your wireless router correctly, and see that it uses WPA2 encryption. Also be sure to use HTTPS on websites. Be careful using wireless devices in public, in free Wi-Fi spots and the like – because the service might be free, but it’ll be costly to you in the end. There’s several other tricks and tips concerning Wi-Fi security out there you might consider as well.
Wireless keyboards and the like can also have information intercepted by someone with the right tools. A wired keyboard is safer, but especially if in public, check to see that there aren’t any hardware keyloggers installed. You’ll usually find these at the back of the tower or wherever the keyboard plugs in.
3G modems are more secure than wireless devices it's been said. If you use a 3G dongle or modem, you may still consider a 3G router, as it will usually allow for faster speeds and increased security. Make sure it comes with a hardware firewall (SPI or NAT, or both). Hardware firewalls are the device of choice when it comes to networks as you can have one hardware firewall and not have to install software firewalls across several computers, which is usually costly and time-consuming.
Your ISP may also filter out traffic too, so make sure to check with them about it.
The most secure setup would be the line installation (ADSL). But cable theft is a serious issue, especially in the third world, and isn't always an option. This is also true if you live in an older, or more rural area. That's where Wi-Fi and 3G come in - as alternatives.
Make sure you set up your wireless router correctly, and see that it uses WPA2 encryption. Also be sure to use HTTPS on websites and make sure it comes with a hardware firewall.


Secure your portable/mobile devices
The more portable the device, the greater risk there is of having it stolen or even losing it. Hackers are now targeting mobile devices like smart phones and tablets, particularly those running the Android operating system, which is quite a few, actually. Why? Because that's where the money is nowadays, and that's what a lot of hackers who bother are after in the end. People often use high end devices like these for banking, and other financial information will be stored or used on them.
The business person on the go doesn't have time to stop - he or she has to do things on the run. But there's not just the threat of someone physically trying to steal your devices, there's also the threat of malware making it on to your devices, too. That's why nowadays, people are quickly coming up with solutions to combat these risks. The days of malware being just a PC-exclusive problem are over.
"The experts claim that your device must have remote locking capability, meaning that if someone steals the device, you can lock it remotely so that it will be unusable."
The experts claim that your device must have remote locking capability, meaning that if someone steals the device, you can lock it remotely so that it will be unusable. You can even remotely lock the sim card, so that nobody can tamper with it, and try and remove the sim to put another one in its place. There's remote data wiping, so that if someone steals your device, you can remotely delete all the files on it so that nothing of value can be gleamed from it. Worst case scenario then is you have to go and buy a new device. Even if the police were able to track it down, I wouldn't want to use it again, personally, because I'd be worried that they had tampered with it in some fashion or installed malware on it to try and reel you in from afar.
Nowadays there are also apps that can be downloaded for your smartphone or tablet which are essentially anti-virus products, that will scan for and hopefully remove any malware that might have made it on there.
I also just want to add, that you should make sure to erase sensitive information from your phone or laptop or any device if you plan on lending it or giving it to somebody. Plenty of people don't bother doing this. So then some person who gets a hand-me-down phone has some information and contacts of yours that they shouldn't have. And they might do something nasty with that information.
Congratulations if you managed to wade through all of this. I may edit or update information present here in the future. Safe surfing to you all! In future I will go in to passwords and further protecting your online accounts.
© 2012 Anti-Valentine

![Microsoft Windows 10 Home USB Flash Drive [Old Version]](https://m.media-amazon.com/images/I/41nRbXjLGGL._SL160_.jpg)