Twitter Hacked - Denial of Service Attack - What does that Mean?
Recently the wildly popular web site Twitter was hacked. The site went offline for a short period, causing minor panics throughout the population of the free world with too much free time.
What happened? Did evil ninja scientists sneak into Twitter headquarters and bog down the server by playing numerous games of Solitaire or Exteel or Evony? Nope. The unpleasant truth is that your computer or the computer of someone you know may have played a part in this international event.
What is Denial Of Service?
A Denial of Service, or DOS, (also called a distributed denial of service, or ddos) attack is a relatively common occurrence on the Internet. Most denial of service attacks go unnoticed by Internet patrons. Modern web servers and web server software are designed to detect and circumvent DOS intrusions without major disruptions in service. Ddos protection is the standard, not the exception. Rarely do DOS attacks even make the news any more.
Visualize a DOS attack this way; you are strolling down the street
in your hometown. Periodically you recognize a friend from high school
who greets you and asks "What are you doing, Bob?" (for the sake of
this discussion, play along and act like your name is Bob ... Roberta is also acceptable). You are
happy to see your old friend and you pleasantly respond with a few
words to bring them up to date on your recent activities. Your friend
moves on, satisfied with your summary. Now imagine that every person
from your graduating class and every person you've ever met since then
simultaneously taps you on the shoulder and wants to know what you're
up to. You have thousands, or even millions, of people all waiting for
a personalized response from you. Along with a very sore shoulder from
all that tapping, you quickly realize that you will never be able to
even begin to recognize and respond to all huge crowd forming around
you. Panic sets in. You rush back into Wal Mart, where no one knows
your name. If you are offended by Wal Mart, just imagine yourself
curled into a ball on the sidewalk. Same difference.
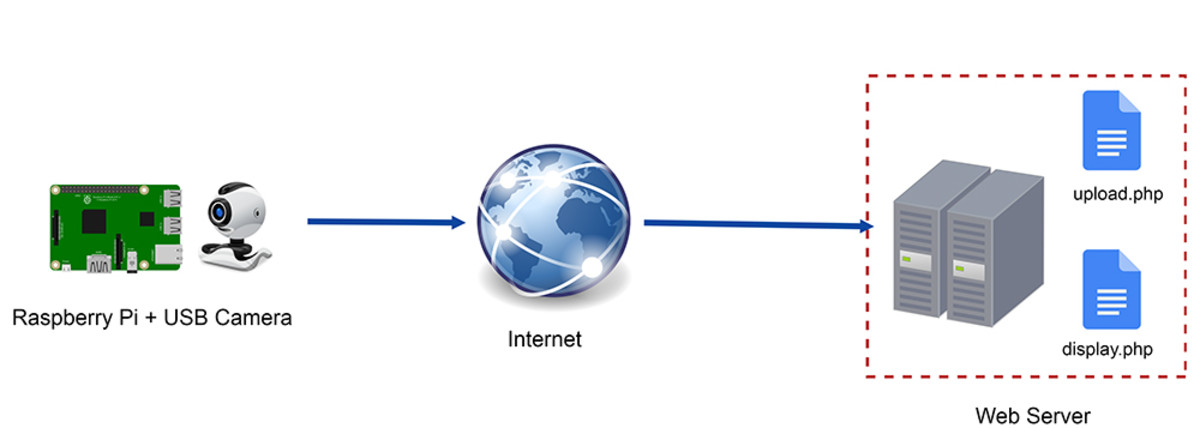
A DOS condition is somewhat like that, except you are a Twitter web server and your friends are browsers all over the Internet. The Wal Mart is still a Wal Mart. The Twitter server becomes so overwhelmed by requests that it simply shuts down, refusing to respond to anyone. A well designed server, actually an array of servers referred to as a "server farm", can politely deal with DOS intrusions through highly technical means such as ignoring them or asking other computers on the Internet to stop relaying their requests. The Twitter servers just need a little upgrading; the Twitter craze exploded so quickly that they probably outgrew their hardware.
How Does This Happen?
How could such a thing happen? Imagine a disgruntled Twitter user sitting at his computer clicking incessantly, creating Tweets with the sole intent of overloading the Twitter server.Now imagine hundreds or even hundreds of thousands of coordinated computers generating Tweets at the same time. That's a Denial of Service Attack. Twitter didn't break, it just overheated and needed a time out. It's very unlikely that any data was lost, save for the attempted tweets that may have been ignored when the DOS was in force.
Anyway, how in the world did the Forces of Evil manage to coordinate so many computers all over the world. Well, that's probably your fault. One of the primary purposes of computer viruses these days is to control infected systems and use them for nefarious purposes. Should you get a virus that merely insists on serving you pop-up ads, consider yourself fortunate. A really devious virus take over your machine and allows someone on the other side of the world to control what it does. Your computer, or a computer in your neighborhood may have participated in the Twitter DOS attack.
There are viruses floating around that take over computers and sell your computer time to the highest bidder. A typical computer is idle about 95 per cent of the time anyway. You can't press keys and click the mouse fast enough to make a modern computer work very hard. The Central Processing Unit, or CPU, spends the vast amount of its' time doing nothing. When you do need it to do something, that something happens very quickly, then the CPU goes back to waiting. Hackers who write viruses take advantage of the horsepower of modern CPUs to install subtle programs that leverage idle CPUs to perform nasty tasks like coordinated DOS attacks. A 'good' or well-written virus will stay our of your way; you'll never know it's there. Of course, make sure your anti-virus programs are current if the FBI knocks on your door.
I think Twitter...
Some images may be courtesy of http://www.sxc.hu/