What is the Microsoft Security Intelligence Report (SIR)?
Microsoft's SIR (Security Intelligence Report) is published by Microsoft twice a year, and defined by Microsoft as a report "that focuses on software vulnerabilities, software exploits, and malicious software".
You can find Microsoft's SIR website and download the latest (and previous) reports (in pdf format) here: Microsoft's SIR Download
Don't let the name fool you, Microsoft's Security Intelligence Report is much more than just the report itself! It's a dynamic website full of great resources, (including all previous SIR editions), tools, threat encyclopedia\glossary, a SIR community, and videos..
Microsoft does a great job presenting security information so that it's easy enough for most readers to quickly understand, yet detailed enough for IT professionals to get some real world statistics and mitigation techniques.
In this article I'll briefly explain some of the site features and information that I've gathered from the latest Microsoft SIR.
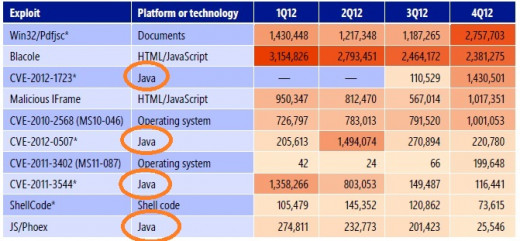
Note - If you gain anything at all from this article, take a good look at the graph of the "Top Ten Exploits found" and remember that Java updates are currently the most important of all.

Microsoft SIR Vol. 13 - the report
First, let's talk about the PDF report itself. The latest Microsoft SIR (at the time of this hub) is Volume 13, Dated January - June 2012, or commonly referred to inside the report as "1H12". (First Half of 2012).
Looking through the Table of Contents, you'll see three main areas of discussion:
- "Deceptive Downloads - Music, Movies, and Software"
- "World Wide Threat Assessment"
- "Mitigating Risk"
As you browse through the report, you'll see easy to read summarized information, and then detailed information, statistics, graphs, and even resource links for further information. Just by browsing through the report, I was able to pick up on a few hot areas of discussion:
- Be careful with what you download. Illegal downloads, especially software with "keygen" software or "key crackers" are an avenue for malware. Also noted were downloaded movies and music.
- Within the top ten exploits noted, 5 of them were Java. Also noted were Flash, and document readers. (Page 23 or PDF page 33)
- Blocking P2P applications is good practice for network admins. This can be done at the router, proxy, or even OS level with Microsoft's new "Applocker".
TIP - Keep your Java, Flash and Reader up to date. (The updates are almost always security related). See below for a graph that specifies the Top Ten Exploit Families found for more information.

Suggested Reading
Deeper into the Report
Mid-way through the report, you can see detailed information on malware infections, locations mostly affected, trends (malware rankings), types of malware, and again, plenty of links to resources for further reading. For example, you can click on a discussed "exploit" to read more about the specifics.
The third section of the report is titled "mitigating risk", and discusses specific attacks, trends and mitigation techniques. One of the tips I was able to quickly pick up was the value of User Account Control and the use of "non-elevated" accounts.
TIP - One of the best ways to limit risk is by surfing the internet as a normal user (not an administrator, or account with "administrative" privileges).

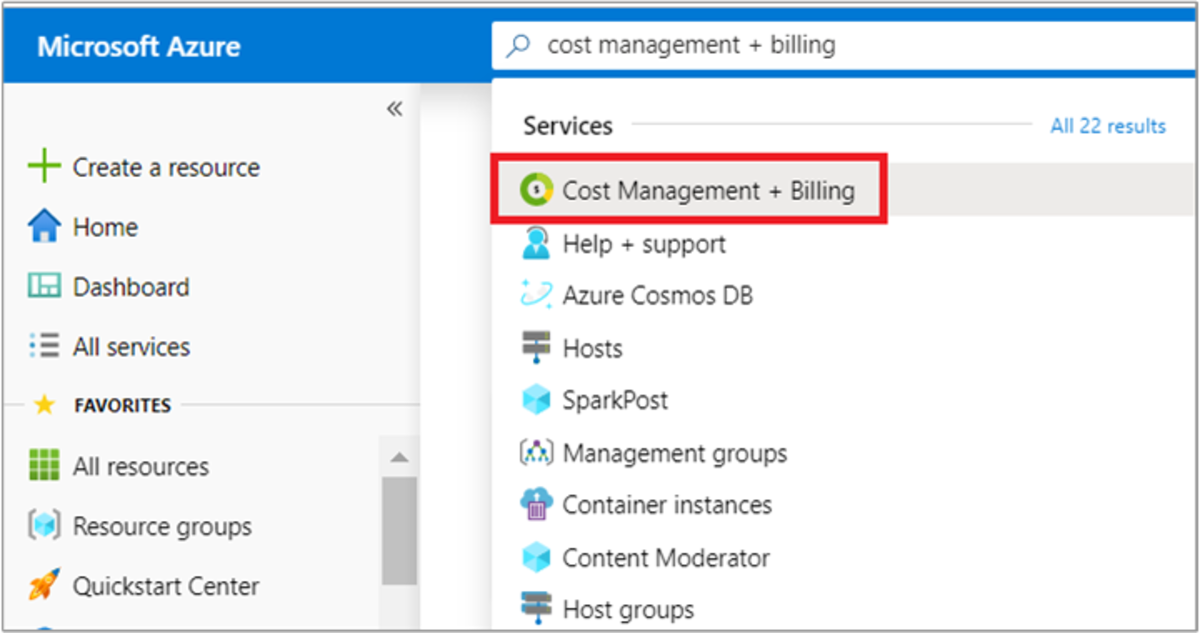
Microsoft SIR - the website
The Microsoft SIR website expands on the information gathered from the reports, and has several sections to browse through, including:
- Regional Threat Assessment -- with links to pdf reports for countries all over the world
- Featured Articles -- with a recap of some of trhe information found in the most recent report, case studies, and even articles such as -- What is a botnet? and Zeroing in on Malware.
- Managing Risk - a good resource for network admins.
- Glossary -- every term defined in one list
- A Video summary of the latest report
- A "Key Findings" PDF that reduces the report to 16 pages (anyone remember cliffs notes?)
The people at Microsoft put ALOT of work into these SIR's and corresponding website, and you can take as little as fifteen minutes to get a good broad overview, or spend hours digging deeper into the referenced material.
Either way, spending some time within this site and latest SIR will deepen your scope of the threat landscape and help you learn better practices for keeping your PC's clean.

UPDATE -- Microsoft SIR v14 -- 2H12
While looking to update this article with a graph to backup my philosophy of the importance of keeping 3rd party tools up to date -- Java, Reader, and Flash especially, I realized that v14 has been released. (Hey, I've been busy..).
Microsoft SIR volume 14 (which is a comprehensive study of threats found in Microsoft OS's during the second half of 2012), starts off with a feature article on the importance of running real time security software. (More important than ever IMHO). It then covers the "worldwide threat assessment" as well as "malicious websites".
I did notice something, on the particular graph I was looking for, "Top Ten Exploit Families Found", I noticed that Java now has four entries. In SIR volume 13, they had 5.
While this may not sound like a big deal, to me, it is good news, as it may appear that Java is improving in dealing with their vulnerabilities. (There have been a lot of updates lately).
My point with all of this is; of all the updates for your Windows PC, 3rd party are the most important. Especially Java, Reader, and Flash. I've attached a recent screenshot of the graph I'm referring to.
For more information, I highly recommend you download the latest copy and at least thumb through it.


Do you know the version of Java you're currently running

~ Credits ~
The Dividers -- All dividers used in this hub were created by howlermunkey.
*note -- This hub is an "editorial", and Is not affiliated with Microsoft or the Microsoft SIR report. My intention is to give my perspective on the information I gathered from the site, and to pursuade readers to use the site and resources within. The author is not associated with the Microsoft SIR, or the website itself.

More Windows articles from howlermunkey: