Why Microsoft Created User Account Control for Microsoft Windows Vista, Windows 7 and Server 2008R2
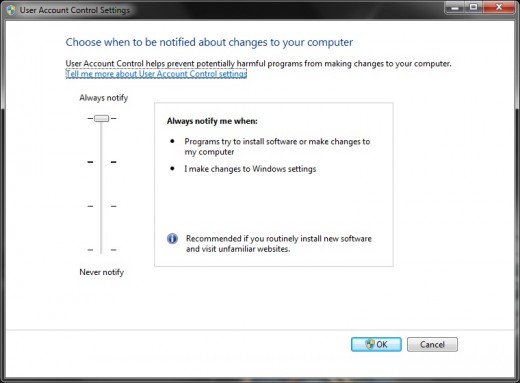
Starting with the rollout of Microsoft Windows Vista, User Account Control has been the source of many complaints aimed at Microsoft’s newest Operating Systems. With Windows 7 and Server 2008R2 Microsoft has enhanced UAC considerably, making it more user friendly and configurable, but do you still want to keep it on? In this article I will discuss the reasoning behind UAC, how it works (without getting technical), and what you can do for your own Windows Systems. TIP – to quickly gain access to the UAC control panel simply type UAC in the search box.
Why the need for UAC?
Back in the ‘Ol days (Windows 95, 98, ME, etc), there was no concept of different privileged user accounts. Every user was granted an admin by default. In fact, most or all of the programs that ran with your Windows system also HAD to run with admin privileges, or they wouldn’t work. The problem with that was that every program running while you were logged on, (every Java app, every flash component, etc) also ran with admin rights and without barriers. Think of the modern internet, almost every page has live, streaming, animated content that is written with multiple languages and code; Languages and code that must be interpreted and downloaded by your web browser. It is within some of this very code that spyware and malware hides. TIP – Java, flash, and adobe updates are almost always security patches, and important to keep up to date. (Even more important than Windows updates if you look at the statistics). With Windows NT came seperate user accounts, but users would log in with restricted permissions, and the applications\processes that ran could still "elevate" themselves (or be elevated) and influence the system at other levels. This is why UAC came about, to help restrict applications and processes unless specifically consented for by an administrator.
Tokens
In Windows Vista, Windows 7, and Server 2008R2 separate user accounts are used and privileges are handed out in the form of “tokens”. (Don’t make it hard, just visualize a subway token).
When a standard user logs in they are granted a “token” with restricted access. “Restricted” meaning they cannot make changes that will affect the entire Operating System. When an administrator logs in, the user is granted two separate tokens for that session, one restricted token and one unrestricted admin token. While the Admin is logged in applications are started under the restricted user token and only elevated after the user is alerted and gives consent (“Run as Administrator”).
Surf as a USER not an ADMIN
One of the best ways to help keep your PC clean is by simply logging on and running your daily tasks as a user and not as an admin, especially when you are surfing the internet. As HubPage writers our research can sometimes take us to the far ends of the internet. We are almost always on new pages, sites, forums, social networks, and blogs. My advice is to do this while logged in as a user. Need to install a program? That’s when you can log into your admin account. You can read more about the UAC settings here. NOTE -- not all malware needs admin privileges, some will go for the user profile, which is why you should clean your PC on a regular basis.
There are many opinions on the validity of UAC. The bottom line is that no system protection is flawless, but the combination of a good antivirus package, Windows Firewall, routine cleaning and UAC can be quite effective. My advice is to turn UAC up until it bothers you, then turn it down a notch. If you can stand to keep it all the way up then do it. The middle two options will suffice but don't turn it off completely. One of the smartest things you can do is to surf the internet as a user, not an admin. Clean your PC as often as you remember too and you'll be good to go. Some of my other blogs include: