PROTECT Your Computer's Security from ATTACKS like from THINK POINT
You alone must PROTECT YOUR SYSTEM FROM ATTACKS
Only you can protect your computer systems from the "embed attackers".
Security Expert Robert Vincent will explain how YOU CAN STOP THEM when they hit your system, and prevent them from entering and eating away your entire windows system right before your eyes!
This just may be the MOST IMPORTANT INFORMATION of the year. Share it with everyone: We all need to know? Virus companies do not want you to know this information.
Because they are not a virus, not a bad cookie and not malware per-say: That is why all virus malware protection applications CANNOT STOP THE EMBED HACKER ATTACKER. modules: But, only you can! If you learn how you can stop them from entering your system.
Please share the link to this lens sharing to help your friends and family in understanding who, what, how and why ONLY they can protect their desktops, tablets and on the go computers.
This knowledge is shared freely to all that desire understanding and a way to protect their systems!
They are a "Direct Hacker" entering your system because you granted permission for them to enter and once inside they take total control of your entire computers system.
Read and learn! And, please share the link with everyone you know.
WARNING.....THE WORST ONE EVER CREATED BY THOSE COMPANIES IS NOW OUT THERE....Read below.
How to REMOVE Virtumonde.sci INFECTION....The worst one for 2015
And, visit often as we will UPDATE as needed to keep you informed.
The Art Painting is titled: Girl Thinking by Arkansas City, Kansas artist pabear48
None of our hubs are monetized.
We share them because that is the thing to do.
You alone can Save your System
The news is informing everyone of a new malware?
The DNS Changer Malware?
Scaring many and bringing in tons of income as people scared try buying a fix or protection.?
While DNS Malware is real....it's targets are the SERVERS and not home computers. But, it does hit at home also!
Simply follow the advice below as it APPLIES TO ALL MALWARE EMBED ATTACKERS.
DNS CHANGING MALWARE is no worse that all the rest listed.
Remember the basic rule: 99.99 percent of all Malware comes from when you use any search engine and then CLICK THE PAGE LINK
and I show you how to protect from those false links. ( They are false because they create a duplicate page and add their malware auton inserts on that false page)
DNS is not NEW! It was first created about 4 or 5 years ago....This is simply the same one being resent out.
Protect yourself as you should from all Malware with my simple instructions and your good common sense.
You alone can Protect Your Systems!
Update: February 3, 2013
Once more I was right on and they were not. Ask your self why they scared so many Americans?
How much did many spend trying to protect their systems?
Then remember share this lens with everyone you know! Learn security for FREE. Right here!
UPDATE:
Another new one is out there attacking Windows7 systems.
It calls itself: Windows Anit-Virus Rampart
Acts like Microsoft Security Center
Attacks and Deactivates your entire system....It is totally fake....DO NOT GIVE THEM MONEY! THEY WILL DRAIN YOUR CARD.
Made by FakeVimes Family.........Fake program MALWARE
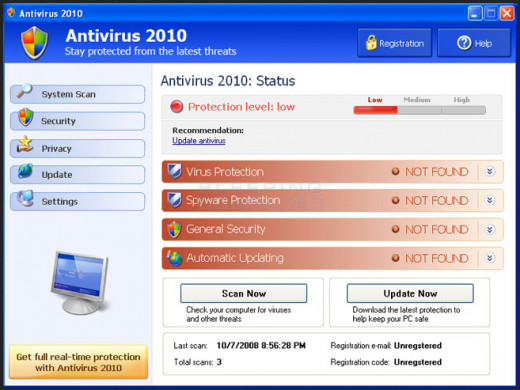
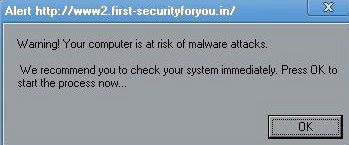
Watch out for fake virus alerts!
Embed Attackers also use security software, and it does appears to be beneficial from a security perspective to the average internet user. However, it clearly is NO GOOD AT ALL.
They do not do anything but go for your system and your money. And the applications continue to hit you with itself, and they provide very limited or no security. But, they do generate erroneous "FALSE" alerts, AND TO GET YOU TO PAY FOR THE APPLICATION.
EMBED ATTACK UNITS are made by rogue software designers to create legitimate looking pop-up windows that advertise security update software. They are not real except the part of DESTROYING YOUR ENTIRE SYSTEM.
Embed Attack Modules also do all of the following instantly when they attach.
Some use social engineering to steal your data.
Install malware that can go undetected as it steals your personal password.
Launch itself with false or misleading alerts.
Slow your computer or corrupt files. Changes the Registry. Turns off Virus Apps.
Disables Windows updates and/or may also disable updates to legitimate antivirus software.
Prevent you from visiting antivirus vendor websites.
Embed Attack units may also attempt to spoof the Microsoft security update process or deny access to it.
They also shut down in many instances SYSTEM RESTORE ( XP, VISTA ) So far not in Windows7 ? But, expect it to happen as they modify their applications.
I am sorry to inform you use OF THIS!
However, we did repair a hit system today by USING SYSTEM RESTORE.......Going back 10 days and it appears to have repaired that computers system. We also did a full cleanup after restoring it. We used on start up the F8 key to use SAFE MODE....In Safe Mode we cleaned up IE by shutting down the add on using MANAGE ADD ONS.....DISABLED THEM....THEN USED system restore. Upon restart the unit did not appear and Microsoft Security unit did come back, We then use MRT.EXE for another clean up.
Will write more if needed.......Bob
Update:........January 2012 another one has now been detected: The module says:
Microsoft Security has detected some errors and must run a scan .........STOP....TOUCH NO KEY....COLD BOOT DOWN!
This is an "embed hacker attacker".......You can protect your systems!
Computer Tips by pabear48: (( I will update as new ones are discovered ))
My free information can save your systems if you learn the steps you need to do to protect your windows system.
The Internet grows and expands every single day. Your enjoyment and the safety for you and your's now depends on knowledge you learn to protect your home system or even your laptop while surfing, exploring and enjoying the entire Internet.
Sadly: There are people out there determined to extract your personal information and if possible steal your identity or simply use methods trying to have you "buy" an item under the guise it will protect you and your system. They are attack hackers willing to destroy your computers and they destroy your entire widows system because you granted them permission!.
There are many virus's and Trojans out there. Many companies that sell applications they say will protect you and some free ones that say the same. Malware dos applications ARE NOT A VIRUS! They are not a Trojan! They are an attack application!
More specifically "Embed Hackers Attack" auto insert modules are the worst of all of them!
Mcafee, Nortons, Microsoft One Care, Microsoft Defender, Spy Bot and EVEN ALL POPUP STOPPERS
DO NOT STOP THE EMBED Hackers ATTACKER. units.
Anti Virus known now as THINK POINT and as Best Virus is absolutely the worst hacker attacker out there and is an Embed Attack Malware Type Unit . IT WILL LITERALLY EAT YOUR SYSTEM piece by piece once it has installed it self in your working system. The hackers that create this make false pages of real sites and then the search engines guide you to them. One click to view and your hit!
More bad people are soon going to be using this same type and style attack module and only you can learn what to do and share this with everyone that uses the computers at home or even at work because even firewalls can not stop this unit. It is used to sell you a product: But their product does not work either? They simply drain your accounts of money! Period.
Thier attack module is granted 100 ,percent access because when you go to a page or click any link from any search engine where they have attached this ATTACK APPLICATION: You by clicking (you yourself) then grant permission for the link to open Therefore YOU GRANTED permission for ALL THINGS ON THAT PAGE TO ACTIVATE AS IT OPENS IN YOUR WINDOW. That is why and how it can appear!
YOU CAN STOP the Embed Attack Module!
Details: THIS IS THE ONLY KNOWN STOPPER METHOD!
If while your surfing or goggling and get hit when you click a link to a page by XPAntivirus2008 or 2009, or Pro Version: or the newest BEST VIRUS, and NEW one called Alpha: 2010 also called now Security Tool or now as THINK POINT and their box opens and appears on your screen: Security Tool has now been made worse in that if the new version hits you and locks in it will stop SYSTEM RESTORE from working: Unless you bypass the applications working: READ FULL LIST BELOW!
Many have asked what I would do and to share it!
First...........Do not click their box: click no where: STOP
Instead STOP.......Touch no key and do not click the mouse: Simply restart your computer with the ON OFF BUTTON doing what is called a "COLD BOOT DOWN"........DO NOTHING ELSE except a cold boot down ASAP
Your system will shut them down this way:
Upon restart:
Once on desktop. Go Control Panel. Internet Options. Open and clear out all caches (Internet Explorer): If using other browsers (make a short cut to its cleaning options in settings of the browser) then you can click that short cut and clean the browser of choice you use (when needed).
Now use disk cleaner.....Restart......Now use disk cleaner once more and use also the top option tab to use the system restore cleaner unit......restart and once on desktop make a new restore point saying like CLEANED MALWARE OUT....restart....that is it!
You are NOW clean and once more safe from this vicious invader.
Hope this aids those who requested and others interested to be safe: Learning how to guard: That is exactly what this writing is about and explaining how easy you can stop them properly so they do not get a registry entry: It is important to learn this easy way! Why?
Because many more companies are getting ready for drop sale markers. Exactly as this company has done because no law against them doing it. AND, no program can stop their hitting you if you bring up any site they have actively linked to auto set:
IF YOU DID NOT STOP and accidently did click anywhere?
There is one LAST DITCH EFFORT that may work?
If it is caught quickly!
There may be a way?
I will try explaining it fully step by step:
1. Shut down the unit
2. Upon start up start tapping the F8 Key
3. When the target board appears: Use the arrow keys to scroll to START IN SAFE MODE-without networking.
4. When your Main Page appears then go to System Restore: .Choose a restore point before the date of the attack and highlight and restore.
5. When system restarts and returns to main desktop .use Disk Clean up tool. Then make a NEW RESTORE POINT: Now use disk cleanup once more and this time click the top tab options and the Bottom choice should be clean out or clean up system restore points (these must be cleaned out) because the embed attack program is in there. Now the system will now clean itself. On Vista cleanup files means CLEAN SYSTEM RESTORE POINTS OUT!
6. Restart: It should automatically do its thing and bring you back to desktop and the attacker should be gone.
I hope this works for you: We have saved many computers doing it this way before it attaches deeper into the drives. If this does not work..then Factory Restore will accomplish the task 100 percent: But, this is an option that works 98 percent of the time if we can catch it quick.
Pabear48
ONLY YOU CAN PROTECT YOUR OWN SYSTEMS
No program removes them!
This method works on any invader. And it makes your system safe after a hit. If you follow it exactly!
Update - A new one has appeared?
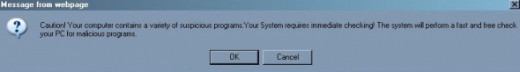
On December 26th I discovered the newest "Embed Attack Module" and snapped an on screen photo of it so you can see what it looks like.
Of course, I then cleaned it all out from my system which is protected far better than most and allows me to try keeping up with these over seas attack companies in order to aid you in protecting your computer systems.
Pabear48
How they do it?
By pabear48
I was asked to explain "HOW they do the attack"?
I will try explaining it as simple as I can: Which high lights again: WHY ONLY YOU can protect your computer SYSTEM.
Every time you activate any page? On that page are the security descriptors, the fields and the attachments: Attachments are like the ads or the pop up modules which are embedded into the coding of the page. The problem is you probably got to that site via a search and then a click to view it. And, it is a FAKE COPY OF THE REAL SITE....With the attack module activated to auto install when the page is loaded by you.
When you "click" to open any page whether a direct lick or via a Search Engine search and then you decide to click a link from the search:
1. By clicking: You gave permission for that page to connect with YOUR COMPUTER
2. By clicking you granted total permission for all attachments to connect with your computer.
a. This connection allows entering your RAM and there by entering your system and Hard Drive.
3. The "Embed Attacker" has coded scripts.
a. Goes directly to the Registries
1. First shuts down any and all Virus Programs
2. Shuts down security and opens a port in the Fire Wall
3. Attaches three interconnected modules to the Browser you are using: They use three which if you can find and deactivate one then the other two reinstall the one deactivated automatic . Once attached they are easy to view: But impossible for the normal user to remove them all at once, and few experts can either once they are embedded. Each unit has from 5 to 9 extra registries attached and now embedded to the hard drive itself. From that point they begin eating away at the system piece by piece.
4. Kills system restore which is its main target.
Lastly, no application exists as of yet that can REVERSE AND FIX without a Main Restore or Factory Restore if they become embedded. UPDATE: SpyBot Search and Destroy newest version is now taking on Virtumonde.sci
And, no application exist that can Protect you 100 percent! Except yourself!
That is why sharing this information with all your friends and family is so very important. My directions work and have saved thousands of systems ONLY BECAUSE the users had the knowledge of what to do BY READING.
Sadly, sometimes they still get through for one jiggles the mouse a tid-bit when the POPUP pops open....That is all it takes to grant 100 percent permission.
I have a great friend! He knows what to do...but, his hands shake and we have had to re-build his system many times for him because he jiggles the mouse some times.
pabear48
List of the known Embed Attack Modules
HERE IS A LIST OF ALL THE OTHER ONES I KNOW OF
Each comes as you search or surf VIA A POPUP Module
Smart Engine SecureDefense TrustDefender ShieldSoldier
IronProtector RegistryClever IronDefense IronDefender
Antivircat SafetyGuard DesktopLayer HelpAssistant
Windows Defence SpyDefender 2010 A-fast Antivirus
Acommander Active Security ActiveAntivir AdCare
Advanced Security Tool 2010 Advanced Virus Protection
Adware Scanner 2010 AKM Antivirus 2010 Pro Alureon
AWM Antivirus Anti virus Protection Anticare
AntiMalware / Anti Malware Antispyware Defender
Antispyware Soft Antispyware Software AntiSpyware Soldier
Antivir / AnVi Antivir Solution Basic Antivir Solution Pro
Antivirus-1 / Anti-virus-1 Antivirus 7 / Antivirus7
Antivirus 8 / Antivirus8 Antivirus 360 Antivirus 2009
Antivirus 2010 Antivirus 2010 / Antivirus2010
Antivirus 2010 Security Centre Antivirus Action / AntivirusAction Antivirus GT Antivirus IS Antivirus Protection AntiVirus Protector Antivirus Security Antivirus Soft Antivirus Software Alert Antivirus Solution 2010 Antivirus Studio 2010 Antivirus System Pro Antivirus XP Antivirus XP Pro AV Antivirus Suite AV Checker AVDefender 2011 AVScanner AV Security Suite / antispybase.net AVSecuirtySuite ByteDefender Cleanup Antivirus / Clean up Antivirus Contraviro Control Center ControlCnt CoreGuard CTRLComponents Data Protection DeadEye / Dead Eye Defence Lab Defense Center / DefenseCenter Defender Pro Desktop Security 2010 Desktop Security 2010 Digital Protection Dr. Guard drive cleaner Earth Antivirus / Earth AV" ErrorWiz Extreme Security 2010 EzPrivacy Gala Search Green AV Security Suite GreenVaccine Hardclean Inprivacy Internet Antivirus Pro Internet Security 2010 IP Clear IronProtector / Iron Protector ShieldSoldier Live Security Suite Malware Destructor 2009 Malware Destructor 2011
MalwareDestructor2011 Malware Doctor MalwareDoc
My Computer Online Scan My Security Engine My Security Shield MyClean MyFasterComputer NavaShield Net Protector AntiVirus 2010NetworkControl / Network Control OneClean OneScan PC Defender PC Defender Antivirus PC Sweeper PC-Guide Pcenter PCommander
Personal Anti Malware Center Personal Antivirus Personal Security Privacy Center ProtectInfo Protection Center / ProtectionCenter Protection System RegClean Registry Doctor Registry Smart Pro ResetInfo SafetyPC Sahat SecureDefense / Secure DefenseSecurity 2009 Security 2009 Security Hijack Security Master AV Security Suite / SecuritySuite Security Suite Pro Security Tool / SecurityTool ShieldSoldier / Shield Soldier SmartSecurity / XP Smart Security SP Center Spy Cleaner SpyAway Spycheck AntiSpyware / Spycheck Anti-Spyware 2010 SpyGuard Spyware Cleaner 2010 Spyware Protect SpywareVanisher / Spyware Vanisher SysGuardSysinternals Antivirus System Antivirus 2008 System Defragmenter
System Security System Security 2009 SystemArmor SystemArmor ThinkPoint Total PC Defender Total Security TrustDefender / Trust Defender TrustDoctor UnVirex User Account Control User Protection VaccineCenter
VaccineData VaccineTree Vdoctor Virus Doctor Virus Protector Virus Remover Virus Remover 2009 Virus Remover Professional Virus Total 2010 VirusCatch VirusCure VSCAN7 VSCodec Pro Trojan Win Antispyware Center Win Center WinBlueSoft WinCleaner Wind Optimizer WinPC Defender / Win PC Defender / Win PC Antivirus Win7 AV Wireshark Antivirus XP Deluxe Protector Your PC Protector Your Protection
Tango toolbar ResultDNS and THINK POINT
FirstSecurityforyou.in is the newest right now !
Read very carefully !!!!
By pabear48.....Read before trying!
There is something else you can do that adds more time to protect yourself when surfing the internet and or using search engines? But, please read and re-read until you understand how to use this information yourself.
I suggest printing this out!
*******************************
Update:
We have received many e-mails thanking us for adding this to our lens sharing, and that people have been able to follow the directions we have tried our best to make as simple but complete as we can! Thank you to those whom have contacted us about this portion of the lens sharing...pabear48
Learning to use the "KEYS" works...and takes patience! Must be done for clicking all links on any web page as well to allow the link to open.
It took me almost a week to get my fingers doing the KEYS automatically, Practice! That was a long time ago and it is now normal procedure and so easy I pay no attention doing it. Took Annlee four days to master using the KEYS and protecting her system.
*************************
I have not shared this because many people we know simply ignore the instructions or because they get tired of having to use the "ctrl" and "alt" keys.
Nevertheless, I have been asked to share this information and now shall.
1. In your browser set the POP UP STOPPER to it's highest setting.
To do this click TOOLS and then click INTERNET OPTIONS and then PRIVACY......You will then see the POPUP STOPPER unit...click it's settings button: Now set to the highest using the tab choice button. Click the APPLY button and finally click the OK button.
( If you cannot in the future learn using the KEYS you can reset this popup back in seconds)
2. This new setting will now prevent any and all pop ups from popping.
As you go to your favorite sites or games to use them at times you must hold down the "ctrl" and or also the "alt" key to allow that page to activate a link or a module ( like a game ) or a (box unit)
You allow then the pop up because you KNOW THE SITE, AND Trust the Site. You can set your browser's pop up stopper to always allow that particular site and then do not need to always use the "ctrl" and or "alt" keys. You do this by clicking first TOOLS and then Popup Blocker and then click POPUP Blocker Settings....copy and paste the site url you wish to always allow pop ups from and not using the KEYS. Example if it were Yahoo. Type in ( www.yahoo.com ) If it were FaceBook ( www.facebook.com ) No brackets of course!
But, here is why it helps: In Search Engines!
Ok, you searched an item and now the page displays all the sites you can go to and or explore and learn even more about what you searched for: If your pop up stopper is set AT HIGHEST SETTING:
Then when you click the search link a strange thing happens you can actually see with your eyes..?
Learning this is the key!
The link starts loading like all do but it "LOADS REAL SLOW" .
That is the indication you can see!
CLOSE THE BROWSER PERIOD! You stopped the "embed Attacker"
This is not a perfect solution of protection: But, it also does work!
The real indication comes when the UNITS APPEAR ON SCREEN, and then most of the time it is simply to late without the right knowledge of what to do or people jump and move their mouse (that grants permission to invade the system)
I have thought hard about adding this information because even friends whom we explained it to and then have tried it and a few friends quickly became tired of using the "ctrl" and "alt" keys when needed. Having to use this extra step to protect their systems was just to much bother for them they said. So they lowered their browser Pop Up Stopper from MAX and were then open to full attack.
Sadly, we have had to re do many of their computers back to factory and they loose everything personal on the system: You cannot burn or save anything once the embed attacker has attached or it simply attaches to the burned items and invades once more the next clean system you drop the items unto. Understand this if nothing more? They attach to the Registry System in multiple places immediately when they enter the system. Each registry entry protects the other entries. (( In other words...you find one and actually delete it from the system...the OTHERS replace it right after you delete it. This process of replacement never ends))
This is why I have really thought about sharing this added way?
But, have decided each person can decide for their own systems and internet usage if they want added time of protection from SEARCH
RESULTS because we all use the search engines: Including me!
Watch for that SLOW LOAD
This is not 100 percent protection? Just another level of added protection.
Pabear48
Microsofts MRT.EXE
How to actually use it!
Microsoft's Malicious Software Removal Tool
This application does remove many things but not the Embed Attacker.
Nevertheless learning How to use it on your systems is a very good idea!
This is a great and safe application to learn How to Use.
We have all seen Microsoft Update installing updates for this
Tool to use in finding and correcting problems from bad apps.
The problem my friends is few know How to Use it? The majority of computer users do not know how to run it?
To activate the MRT.EXE application:
Click on your start button icon.
Then click the RUN tab
Now type in the box: MRT.EXE
The application unit will now open up.
Click NEXT
You have choices: Quick scan and Full Scan or a Customized scan
Normally all you will ever use is the QUICK SCAN
But, once every month Run the FULL SCAN just before you head to bed because it takes a very long time and will be sitting there done in the morning.
RUN THE SCAN and, .If it finds anything simply follow it's suggestions and directions. If not close and enjoy your system.
IF it did find things Remember after a restart MAKE A RESTORE POINT.and then clean out all OLD RESTORE POINTS
MRT.EXE is worth the effort to learn How to Use !
Blessings .pabear48
REMEMBER this unit while good for many items but DOES NOT ADDRESS ALL MALWARE EMBED SPYWARE ATTACKS.
And, cannot remove then or stop then once it has activated with your permissions to insert simply because you wanted to view a web page you searched for and your browser opened the page and the "Embed was there".
Update
The photo I captured in a screen shot showing the newest embed attacker for 2011
I added it to this module as a Reminder that MRT.EXE cannot remove it from any system!
If this information was helpful? Please share the page with co-workers, friends and family who may also need the information today.
Outlook Express tip by Ole Pabear
Remember to share this with friends and family!
Hello All:
In this day and age E Mails are becoming larger and with animations and sounds embedded. Most ISP's have not corrected their servers to allow these to FLOW EASILY.
THIS YOU YOURSELF CAN CORRECT BY SETTING AN OVERRIDE
To set OUTLOOK EXPRESS TIME OUT OVERRIDE IS EASY:
Open Outlook Express
Click Tools
Click ACCOUNTS
Then click PROPERTIES
Then click ADVANCED TAB
NOW LOOK FOR THE BAR THAT SAYS SERVER TIMEOUT
SLIDE THE BAR TO THE RIGHT...ON FULL
CLICK...APPLY AND THEN CLICK OK
Now REBOOT SYSTEM
ONCE BACK MAKE A SYSTEM RESTORE POINT
SAYING: FIXED OUTLOOK EXPRESS
SAVE
REBOOT ONCE MORE
Thats it!!
YOU HAVE CORRECTED AND NOW LOCKED IN THE CHANGE
HAPPY COMPUTING
PABEAR48
Pass Word Security
By Security Expert pabear48
PASSWORD SECURITY:
Today, sad to say-but programs exist to steal your password from web site server computers. How then can you protect yourself ? SIMPLE! By simply creating a brand new password that is encrypted. Then use this password everywhere you use a password on the WWW.
One password for all applications and sites, and no need to change it. Once created.
IT IS SAFE AND SECURE.
Most passwords stolen come from people around you that watch for them? Sad but true!
Or the simple mistake of writing them down!
Here is how to create your own:
((( Sample ))) { 6555ptch02 }
First pick any four numbers that you absolutely know without doubt...do not write them down on paper...NOW. pick a five letter word you know by heart and never need to write down anywhere: Now remove the vowels and write it next to your four numbers. Then add two more numbers at the end
( your year of birth works nicely for the two end numbers): That's it!
You now have an encrypted password...Now go change yours at all sites you use one and feel secure...
As always! You can do it!
Remember to share this information by sending the link to friends and family: Thank you....pa
Ask why pay for save or backups?
By pabear48
Are you paying for a service to "Back Up" your files? Protect your files they state from everything? Of course they actually can do this! Many online companies simply use scary ads to take your monthly payments.
But: So can you save and backup every one of your files for FREE!
Backing up your personal files is extremely easy and simple?
YOU CAN LEARN HOW TO DO THIS.
And, you do not need any payed service to do it for you.
If you have a CD or DVD burner use that device.
If not, buy a Flash Drive and use that device when no cd/dvd unit
is on board like in many smaller notepads.
The key is to keep all your files: Every one of them located in one place
on your system: Like MY DOCUMENTS.
You can make and have as many folders as you ever need in MY DOCUMENTS.
NOW learn how to save which means BACKUP.
On most computers you simply right click the MY DOCUMENTS icon and choose SEND TO....send it to either a cd/dvd burner or to the FLASH DRIVE.
It is that simple! You have now backed up and saved YOUR FILES.
To replace: When and if ever needed...! Or if you loose or have to reformat and re-install your system. In any of these the procedure is the same.
Simply put in the cd/dvd and open it. Now drag and drop what you need...or simple Right click...choose all.......copy and now paste into your reformatted MY DOCUMENTS....and if a box states overwrite existing files...overwrite all...that simple.
Those services do not reinstall your entire operating system and your files. Only your PERSONAL/BUSINESS files do they hold and secure for you. That you can do your self and for FREE.
Any file you have can be saved: And then reloaded anytime you want or need to.
But, using one spot like MY DOCUMENTS to hold every file type is the simple way to save...and have secure all things: From personal notes, business, school, music, videos, pictures and all else.
Any time you add something and want is secured: Add it to a spare flash drive!
You do not need to pay any service to protect your PERSONAL COMPUTER FILES what-so-ever? The choice is now yours!
Some people invest in an external hard drive that hooks up to any computer or notebook unit via the USB plug in port. These also work just like the cd/dvd or flash units. YOU send what you want to the external drive for backup and saving, and then retrieve any file or all the files one at a time or in the entire batch as you choose. Again showing you do not have to pay monthly services to do what you can do for FREE.
Any system or any hard drive can go bad instantly without warning: Even an external drive! I use dvd's which hold tons and always make (TWO) sets because even a dvd disc can go bad for many reasons. When I use flash drives I also double copy to them and keep both sets in different places at all times.
I also use the FREE MSN provided Sky Drive.....Which you can upload any file and keep it 100 percent SECURE. Like an online flash drive or online cd/dvd. Just choose keep file PRIVATE! If you fill up your Sky Drive space: make another account and use another one. FREE and Easy!
It is just one more OPTION instead of paying some service a monthly fee.
If this aided------Please share the link with your friends and family!
Thank you.......pabear48
They charge you to save your personal and/or business files ONLY.
And, they do not rebuild your system....nor re-install your system?
Nor do they protect and reinstall the applications on your system?
They also do not update your operating system: that you do also yourself: Most units are set to auto updates for System.
You must do that also if and when needed.
XP DISK CLEAN TIP
Works on newer systems also!
I know that all you with XP Systems do use your disk clean up utility on a regular basis. This is good for you. Right?
But, do you remember to use the tiny scroll bar and add a check mark to COMPRESS FILE CLEAN UP? And make sure every box has a check mark?
I find myself sometimes forgetting this important item...If you have not done this...Try it and you may find thousands upon thousands of files that XP can automatically clean up. The application remembers your choices so the check marks will stay put.
If you discover you have been forgetting to look/scroll and add a check mark for total Disk Cleaning...Please do it now..
After...Disk Clean finished
Remember to reboot?
After REBOOTING....MAKE A SYSTEM RESTORE POINT with a note that you have cleaned ALL COMPRESSED FILES.
ALSO A GOOD TIME THEN TO USE A REGISTRY CLEANER TO CLEAN UP THE REGISTRIES....many sub applications come with cleaners for the registry:
Examples are: Mcafee, Norton's, Spy-Bot or purchase one for permanent use.
THEN,,,FULLY MAINTAIN...AND DEFRAG...RESTART...MAKE ANOTHER NEW SYSTEM RESTORE POINT
NOW OPEN DISK CLEANER ONCE MORE
CLICK OK
NOW WHEN IT HAS SCANNED
OPEN THE MORE OPTIONS TAB
GO TO THE BOTTOM ITEM...SYSTEM RESTORE
CLICK THE CLEAN BUTTON
CLICK OK AND NEXT BOX OK
THIS WILL CLEAN AND REMOVE ALL OLD RESTORES
NOW REBOOT ONCE MORE
WHEN BACK MAKE A FRESH RESTORE POINT THAT SAYS: all restores cleaned
Do a final reboot to lock all this cleaning in and your done
YOU WILL FIND THIS WILL RESTORE FULL SYSTEM SOURCES BACK TO FULL POWER.....IF YOU TAKE THE TIME TO CLEAN RIGHT...YOUR COMPUTER WILL LIKE IT ALLOT....SO WILL YOU!
And your system will run far faster once more!
BEST WISHES
PABEAR48
Please remember to send the link for this information to all your contacts, friends and family members who may also need the information?
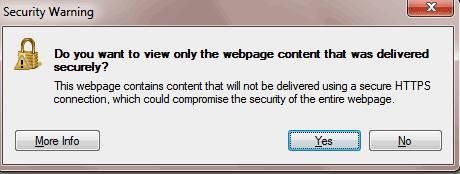
Fix that Annoying Security Warning in IE 8
Make a Custom Command
Fix that Annoying Security Warning in IE 8
This security warning can be changed to disable it!
On the popup box itself no matter how many times you say yes or no: It will not remember your choice, and still will continually popup while you surf the web.
However, you can disable this mixed content warning in
Internet Explorer. The warning itself simply means the web page has secure items and un-secure items usually in images or other elements hosted on a non-https location within the web page your viewing that is a secure HTTPS connection.
If you would like to disable this security warning forever, go to Tools: Then to Internet Options and select the Security tab. Make sure the Internet zone is selected and then click the Custom Level button. Scroll-down the list of options and set the Display mixed content setting from "Prompt" to Enable.
You have now customized your Internet Explorer not to show that popup warning. Sometimes after deep cleaning you may have to reset this choice in the future and now you know how to.
pabear48
How you can REMOVE Virtumonde.sci INFECTION
By Pabear48: Share this with friends ASAP
2014 NEW DEEP ATTACKER............READ VERY CARE FULLY
New Information:
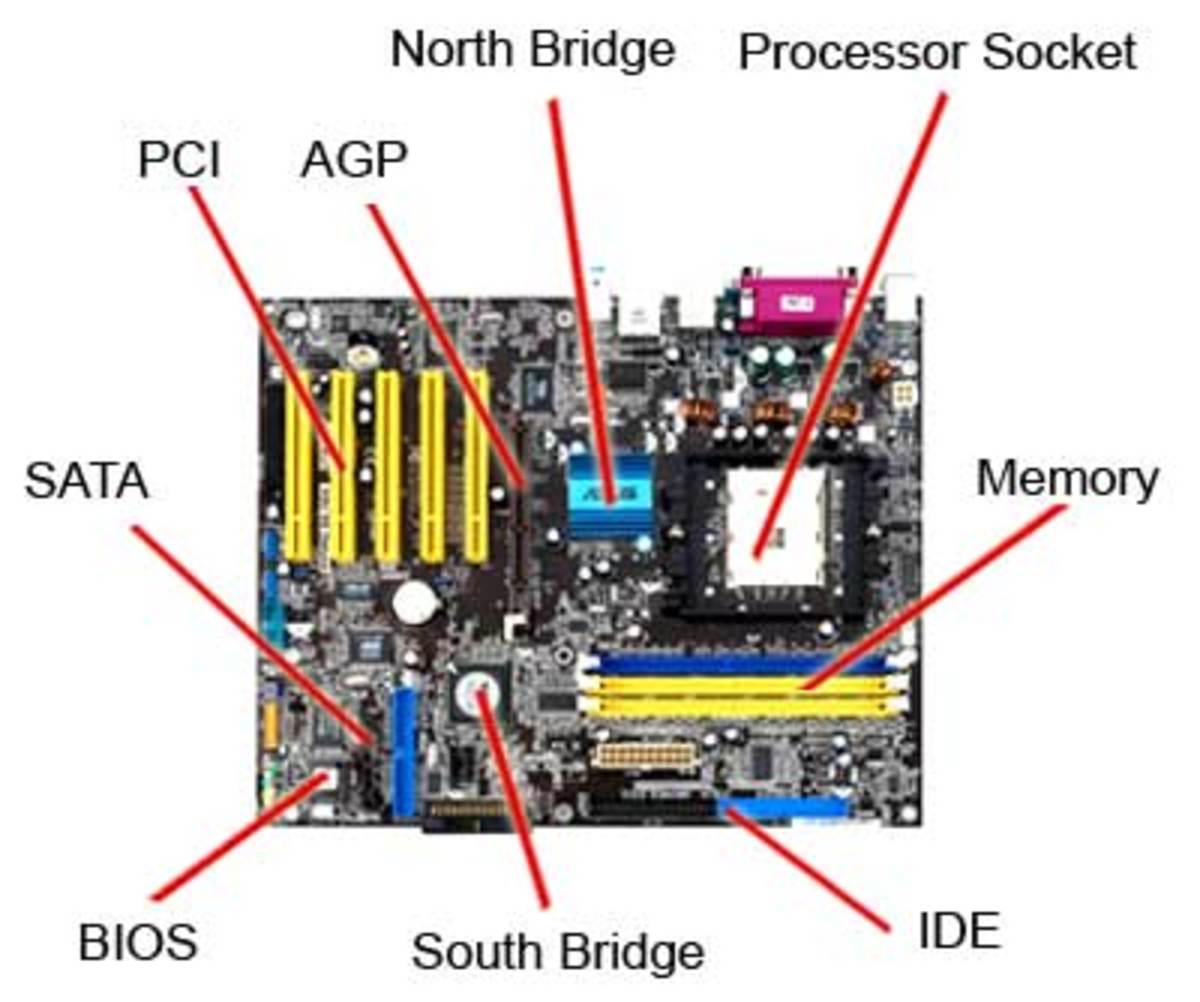
Right now the worst attacker has become Virtumonde.sci and it rips a system drive to pieces.
I have uploaded a photo just below this article that shows what a drive infected looks like when you check a drive with your fragmentation unit.
This bad program inserts the following:
Microsoft Windows Security Center.Anti Virus Override:
This allows the attacker to fully disable The Security Center and its protocols.
Fake Alert Windows Work Station: Full Malware that starts re writing itself thousands of times shutting down your system piece by piece.
Win32.Delf.uv: This bit kills the ability to restore/fix or change the above two.
This attack can be stopped and your system saved by the following choices:
1. Re do a format and install a fresh entire system.
OR : Try this!
Download and install SpyBot Search and Destroy: And, I suggest do that now and learn to use it.
IF your system gets hit by Virtumonde.sci use Search and Destroy:
How?
Start system in SAFE MODE:
AS SYSTEM STARTS... tap F8 until the screen appears: Choose Safe Mode (TOP LINE)
Use the up down arrows to move the cursor and the enter button to accept.
When it arrives At desktop start up Search and Destroy...Update it...then use full scan.
Allow it to run fully: It will detect the problems. THIS SCAN IS NOT FAST
When done click CHECK ALL and then click FIX....It will do it thing, but will not be able to remove and fix them all....IT WILL ASK IF AT NEXT START IT CAN RESCAN? choose yes.
Let system start up normally by itself: In that process Search And Destroy will appear and start scanning..........LEAVE IT ALONE....THIS SCAN IS GOING TO TAKE A VERY LONG LONG TIME.
When Search and Destroy finally ends: IT WILL TELL YOU.
Restart: Normal to desktop: Now use Disc Cleanup immediately...When that is finished: Open Restore and CREATE a RESTORE POINT...name it ONE...run it...Now OPEN Disc Cleaner again...run....use more options tab on top...then choose at bottom SYSTEM RESTORE CLEAN UP...check the ok and yes boxes...and then final OK...when it has finished: Back to make a RESTORE POINT...type in: Cleaned my system of attackers....then disc clean once more exactly as above.
Now restart system: When at desktop run Search and Destroy full scan again: It should now come up with no invaders and show they are gone.
YOU JUST FIXED YOUR SYSTEM
Best of luck.....pabear48 PLEASE SHARE THIS INFORMATION!
If this fails? Only total NEW SYSTEM INSTALL WILL WORK
FREE SPY BOT safe auto download url: copy AND paste http://www.safer-networking.org/mirrors16/
What your DISC will look like
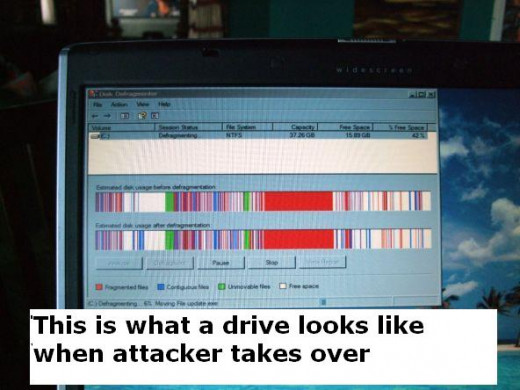
Example of Anti Virus Malware once attached to system - Totally FAKE and DOES NOTHING BUT DESTROY SYSTEM