How Mobile Phone Tracking and Spying Software Works?
Before knowing what a mobile locator is and how it works, you need to know and have a clear understanding about the privacy violation rules and regulations of your country. Not everyone should be allowed to use this cell phone locator software.What if your every action is tracked by a mobile locator by your business competitors or someone else.Do you really know that how much your private life is secured? No, it does not mean in terms of life security-it is the question of maintaining a level of privacy from your side. Perhaps, for the time being you are living a peaceful and secure life,it does not mean that your every activity is not being monitoring by others or by any secret agency. Many of us even don’t have any idea how much advancements have taken place in the research of designing digital spying products-and mobile locator is one such software that is even publicly available for use to track and to collect the information about the a cell phone user. It is said that what is visible in the technical world is 20 years old tech. You are not given the real news of the happening events of the both industrial and educational research and technical domains . One of the existing digital privacy violating devices has been introduced in this hub- which is called by someone mobile locator or tracker or even cell phone spying software. Before saying anything about the impact of this product violating the privacy of our life we should remember that no device is bad, unless it is handled by unlawful and unauthorized persons. So, at the end well will see that this spy phone software has the equal potential to either safeguard or hamper our private life.
Mobile Locator and Tracking
You may need a mobile locator for a number of reasons. Secret agencies use mobile locator to track or keep an eye of their suspects. Adventurous people may need it in their mobile so as they can be tracked in case of emergency situations. For tracking a mobile the locating facility must be present in the mobile and this locating software will keep sending regular signals to its tracker about the present location of the cell phone.
Difference between Mobile Locator or Tracker and Spy Software
Mobile tracking and spying are much similar in terms of functionality but the purpose and output of the tracking signal may be different. For example, if you only need the exact GPS position of a mobile then you just need to have the longitude and latitude information of the mobile, nothing else. On the other hand if you want to read the messages and want to listen the voice calls received in the target mobile, then the mobile locator have to copy all sms and voice calls either sent or received by that cell phone and send to your receiver -thus tracking and spying are almost same in functionality, sending you the information of a target mobile. But the types of information sent to you may be different (sms, gps position, voice calls etc...)
"If you only want to track a mobile phone that can be done by your mobile operator without installing any software on the target mobile, and only the operator can read or hear all the SMS and Voice calls of that phone. But if you want to have all the copy of SMS and want to listen live calls of the target mobile phone then you must install software in the target mobile."
Cell phone spy software
Cell phone spy software helps you to spying on target
mobile phone to read SMS, listening live calls and tracking the GPS location of
the target phone. This is a completely stealth software, which you just need to
install in your target mobile phone for spying on anyone using that cell phone.And every spy software also works as a mobile locator.
What are the features of Spy phone software?
After installing the spy software on your target phone, you will be able to do the followings:
- Live call listening on the target mobile ph.
- You can have both incoming and outgoing SMS information and read it.
- You will be notified from time to time if the target person has changed his SIM
- Secret SMS can be sent to the target cell to control its functioning
- The target phone can be tracked from anywhere of the world. Even if your target keep moving from a country to another-then also the tracker software will be able to send you the target location and all the necessary calls related information to you within a minute.
- This type of software remains completely undetectable by the targeted person’s mobile.
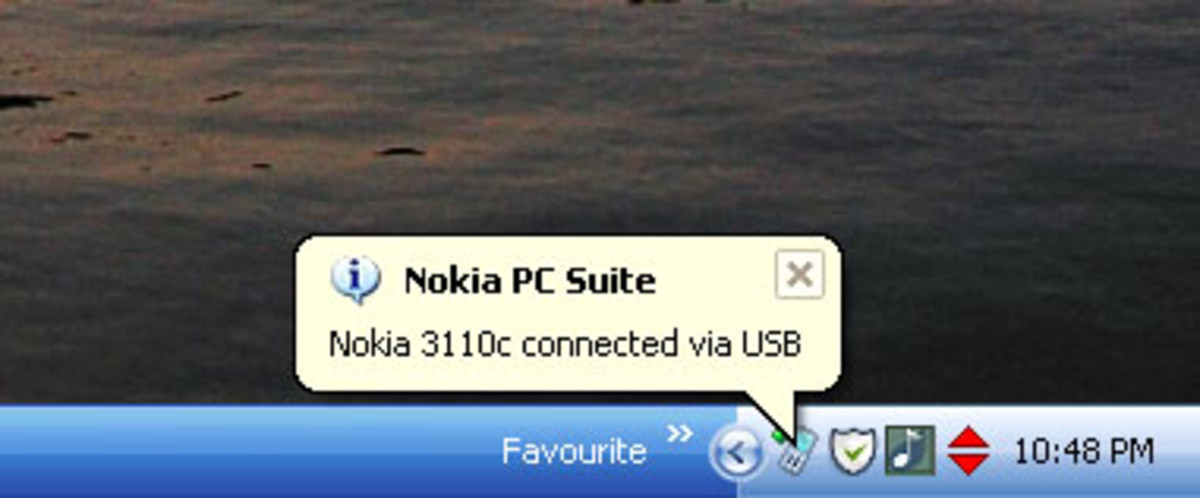
How spy/trackging software works?
For spying on any target mobile set, you must install the software on the victim’s (target) hand-set, it takes just a few minutes to load the software, and then you do not need to do anything with it. The installed software will keep tracking and recording all the activities of your target and keep sending all the records to you to your Internet account for that software. You can either access your spy account from your Cell phone or PC via Internet.
Limitation of Spy Cell Software?
It is very difficult for you to spy on someone who is not in contact with you, because at first you need to have physical access to the target phone for installing the software. The second limitation of this phone is that the target phone must be logged in to Internet on a regular basis for sending back all the tracked information from the targeted person’s cell. Another limitation of this software is-it works only with Blackberry, Android, iPhones, Windows mobile and Symbian OS. Furthermore, if the target person changes his hand-set, then once again you have to install the spy software on his set.
Ethical issues of using Spy phone software? Who should use it?
Someone may use this technology to spy on their spouses, business competitors, kids, neighbors etc. But this technology certainly poses a significant risk to our privacy, if it is used by ill-intentions by anyone. So, it is the question of ethnics who is selling and who is buying this software for which purpose. Upon verification of total identity of a persona and his background the vendor company should sell it. And then, of course, the person who buys it should be considering how to use this software for enhancing his personal security without costing the privacy of others. Think about a terrorist planning a deadly attack in a hugely populated public place like rail-way station or an airport. If spy software can be loaded on to all the suspected terrorists’ mobile phones, then law enforcement agencies will definitely become more effective in protecting us from future terrorist attacks.As far as effectiveness of mobile locator or tracker is concerned, many lost mobile phones can be recovered if mobile manufacturer include the mobile locator in every devices they produce,
Finally, spying laws needs to be more effective in governing and maintaining the privacy of the lives of common people. And spying equipments selling vendors need to be under strict and close monitoring of the law enforcement agencies, so as only person with the realistic need for a spy device can be benefited.