Signals Intelligence Explained

SIGINT at a Glance
Signals Intelligence provides a lot of information that at times and be up to the minute if not real-time or live. Compromising capabilities can adversely impact combat operations such as the time that that reporter probably assumed Al Qaeda didn’t have access to media coverage when they mentioned that the U.S. was tracking Bin Laden by his mobile communication device causing him to stop using it. For this reason, much of it is highly classified and I’ll only cover it briefly. Part of the criteria for classification is proximity of information (to many relevant tidbits in the same place). You’ll notice that I’ve referenced more sources than I’ve cited.
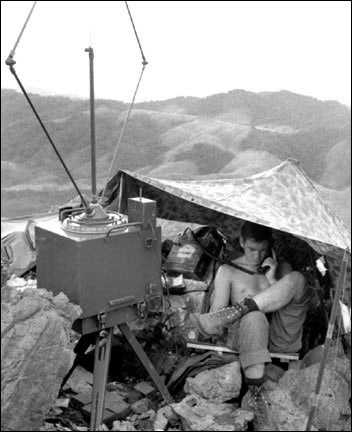
SIGINT is actually a combination of two types of intelligence Communications Intelligence (COMINT) and Electromagnetic /Electronic Intelligence (ELINT) (Andronov 1993, 57) ELINT is information gained from electronic signals that do not contain speech or text and is divided into two major categories: Technical ELINT (TechELINT) And Operational ELINT (OpELINT). (National Security Agency 1998)
OpELINT focuses more on threat assessment and targeting at the tactical level and provides information to both military planners and battle field commanders. TechELINT is information about things that emit electronic frequencies such as radar stations, communications frequencies. TechELINT is more concerned with the fact that you’re talking more so than what you’re actually saying which would be COMINT’s piece of the puzzle. TechELINT will pick up on trivia such as what types of communications are being used for example, walking down the hallway of an elementary school you may hear chalk tapping and scratching on a board, that’s the communication platform. This platform is generally used in a classroom with children. Further down the hall, you may smell dry erase markers and hear them squeaking away on a dry erase board. This communication platform is usually used with adults so there could be a staff meeting or training session in progress. The rate at which the chalk writes on the board could be considered traffic or chatter. The more there is, the more information is being communicated. Rapid writing on a board is probably a teacher writing notes for the class to copy while a more slow and deliberate or hesitant writing may indicate a student doing a math problem and showing their work in front of the class. COMINT could be compared to peeking through the blinds and reading whatever was being written. COMINT also involves cryptology, code-breaking and languages. So if the class was playing win-lose-or draw or perhaps learning a foreign language, the COMINT analyst would have to interpret what was on the board and report it to his intelligence consumer.
SIGINT has actually been a bit of a game changer in the Global War on Terrorism. In spite of some media leaks, we’re using it to our advantage in Afghanistan to help keep troops alive as well as to locate and neutralized enemy positions.
Was this hub helpful to you? If so, Please Click here
REFERENCES AND FURTHER READING
Andronov, Major A. Kosmicheskaya Sistema Radiotekhnicheskoy Razvedki VMS SShA "Uayt Klaud" [The U.S. Navy's "White Cloud" Spaceborne ELINT Sys]. London: Jane's Publishing Company, 1993.
Associated Press. Report: 7 Bin Laden Attacks Stopped. February 24, 1999. http://www.anusha.com/newladen.htm (accessed June 15, 2010).
Brian Ross, Mike Lee. Officials Narrow Bin Laden Search to Caravan. March 07, 2003. http://abcnews.go.com/International/story?id=79633 (accessed June 15, 2010).
Cal Perry, Jamie McIntyre, Barbara Starr, Henry Schuster, Randa Habib. Cell phone tracking helped find al-Zarqawi. June 10, 2006. http://www.cnn.com/2006/WORLD/meast/06/09/iraq.al.zarqawi/ (accessed June 15, 2010).
Kessler, Glenn. File the Bin Laden Phone Leak Under 'Urban Myths'. December 22, 2005. http://www.washingtonpost.com/wp-dyn/content/article/2005/12/21/AR2005122101994.html (accessed June 15, 2010).
National Instruments. Strategy for Signals Intelligence from Antennas to Analysis. February 11, 2010. http://zone.ni.com/devzone/cda/tut/p/id/6429 (accessed June 15, 2010).
National Security Agency. Cryptologic Almanac 50th Anniversary Series. February 24, 1998. www.fas.org/irp/nsa/almanac-elint.pdf (accessed June 15, 2010).
NSA. SIGINT 101 Seminar. August 24, 2007. http://www.fas.org/blog/secrecy/docs/seminar.pdf (accessed June 01, 2010).
Owen, David. Hidden Secrets: A Complete History of Espionage and the Technology Used to Support It. New York: Firefly Books, 2002.