Protecting Your Wireless Network
These days it's pretty easy to setup a personal wireless network. In 10 minutes you can have a Wi-Fi hotspot right in your own home. You can have access to the internet anywhere in your house. You might be aware that when you do setup a wireless network that you are broadcasting your network to potentially unwanted guests. Think of it as setting up your computer in front of your home where anyone is welcome to use it and has a big sign that says “Smith Family Network”. It's pretty scarey if you think about what kind of information they would have access to: finances, passwords, photos, personal documents, etc. Especially now that more and more home electronics and appliances become networked together.
Computer security has been a big concern for a while. Identity theft looms about wherever you may go and you always have to watch your back. Just because your wireless network is physically located within closed doors, doesn't mean people with malicious intent can't access it. They don't even have to be malicious. They may be your neighbors who don't want to pay for internet service so they use yours. Technically it's stealing and illegal. It could cause your internet connection to slow as they eat away at your bandwidth.
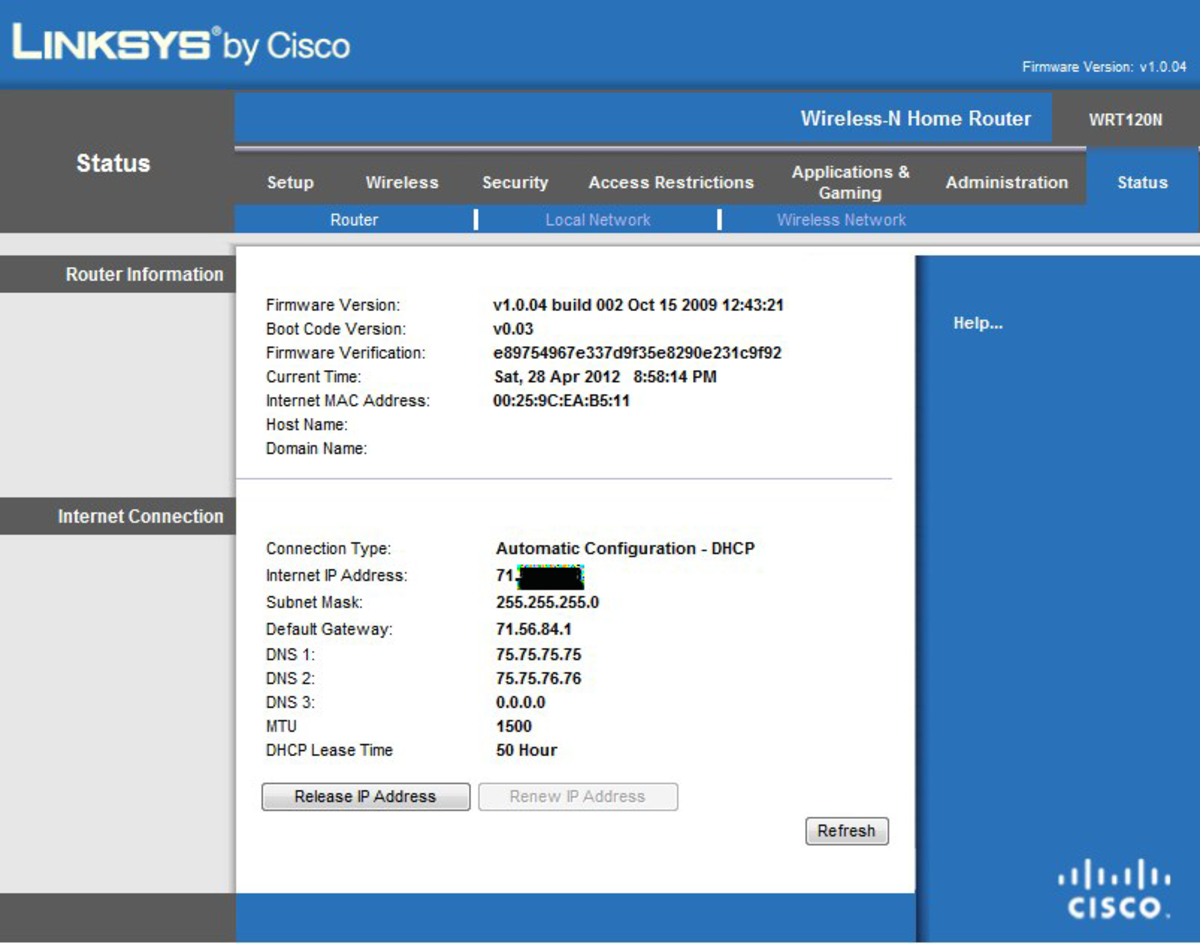
There are some precautions that you can take to make sure that no one without authorization can access your network. The first is to password protect your wireless router itself. You may not think of it but if someone is broadcasting an unsecured home Wi-Fi network, someone in their car across the street could easily access not only your computers on your network but also your router. They could not only change your settings, but they could cut you off from your own service. Most wireless routers can be accessed through a web browser like Internet Explorer or Firefox. Usually by default through 192.168.1.1 or a similar IP address. Accessing it is similar to typing in a URL. Setting a password for your router would be the first tip to securing your network.
The next logical step would be to password protect your network connection. Setting up an encryption between your router and wireless devices will help ensure your network is secure. Usually this is done through WPA/WPA2 (Wi-Fi Protected Access) or WEP (Wired Equivalent Privacy) encryption protocol. Between these options I would recommend WPA/WPA2 as it was developed in response to security weaknesses found with WEP. When encryption is enabled, wireless devices will need a password before the router will allow the device to connect.
Wireless routers broadcast a SSID (Service Set ID). Usually by default it is named “linksys”, “dlink”, or “belkin” for more common routers. When you connect to a wireless network, the SSID is the name of the network and it is what you see in the list of available networks. You can easily change the SSID when you initially setup the router or if it's already setup, in the router configuration tool-set like mentioned above. Keeping the default SSID may invite more malicious people to gain access as it assumes a poorly configured network. The best option is to disable SSID broadcasting all together. Doing so would mean the connecting wireless device would have to know the name of the network before it can connect. Coupled with a password, it would be difficult for the majority of those unauthorized persons to gain access.
There are more advanced settings that would further enhance your network security like setting up static IP address, enabling MAC address filtering, and setting up firewalls. Firewalls are common and Microsoft Windows has a default firewall that is usually adequate for the home user. Consulting your wireless router's manual can help you further if you feel inclined to go beyond what is discussed in this article.