Siemens Halts Computer Virus For Key Infrastructures: Utilities, Nuclear Power Plants
Chernobyl Nuclear Power Plant: Virus threatens World-Wide Industries -- Could This Happen Again? Unidentified Foreign Threats


Virus Called, "Stuxnet;" Spread by USB Devices
A concern is a virus such as "Stuxnet" could be used by criminal organizations, terror groups, or nations to sabotage power plants and other utility networks that are important to national security or well-being of the United States. As I had noted in another hub, our infrastructure is vulnerable to cyber attacks.
Most industrial control systems were engineered 10 to 15 years ago and virus attack was not a concern for industrial automated systems. Vendors are now entering into the discussions to devise, plan and implement controls to not be vulnerable.
Siemens AG said per article in Wall Street Journal, August 13, 2020, by Christopher Lawton, "the threat has been largely suppressed, but the threat has stepped up government and private-sector efforts to ward off future attacks."
The virus was detected in June. It was the first large scale attack on infrastructures. The German engineering giant (Siemens) is one of the largest makers of automated systems, making it a good target. Siemens in July released a tool for customers to detect and eliminate the virus. This a vulnerability for corporate espionage and national security.
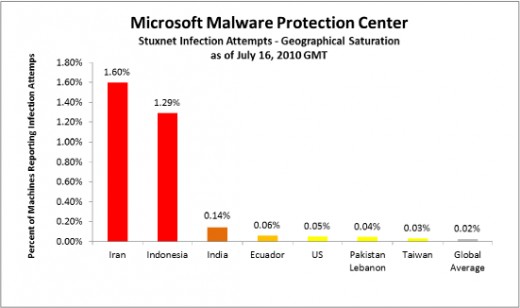
According to Microsoft website advisory, a high concentration of reports of infection attacks, as much as 1,000 computers per day, are in Iran, Indonesia and India. (See above chart)
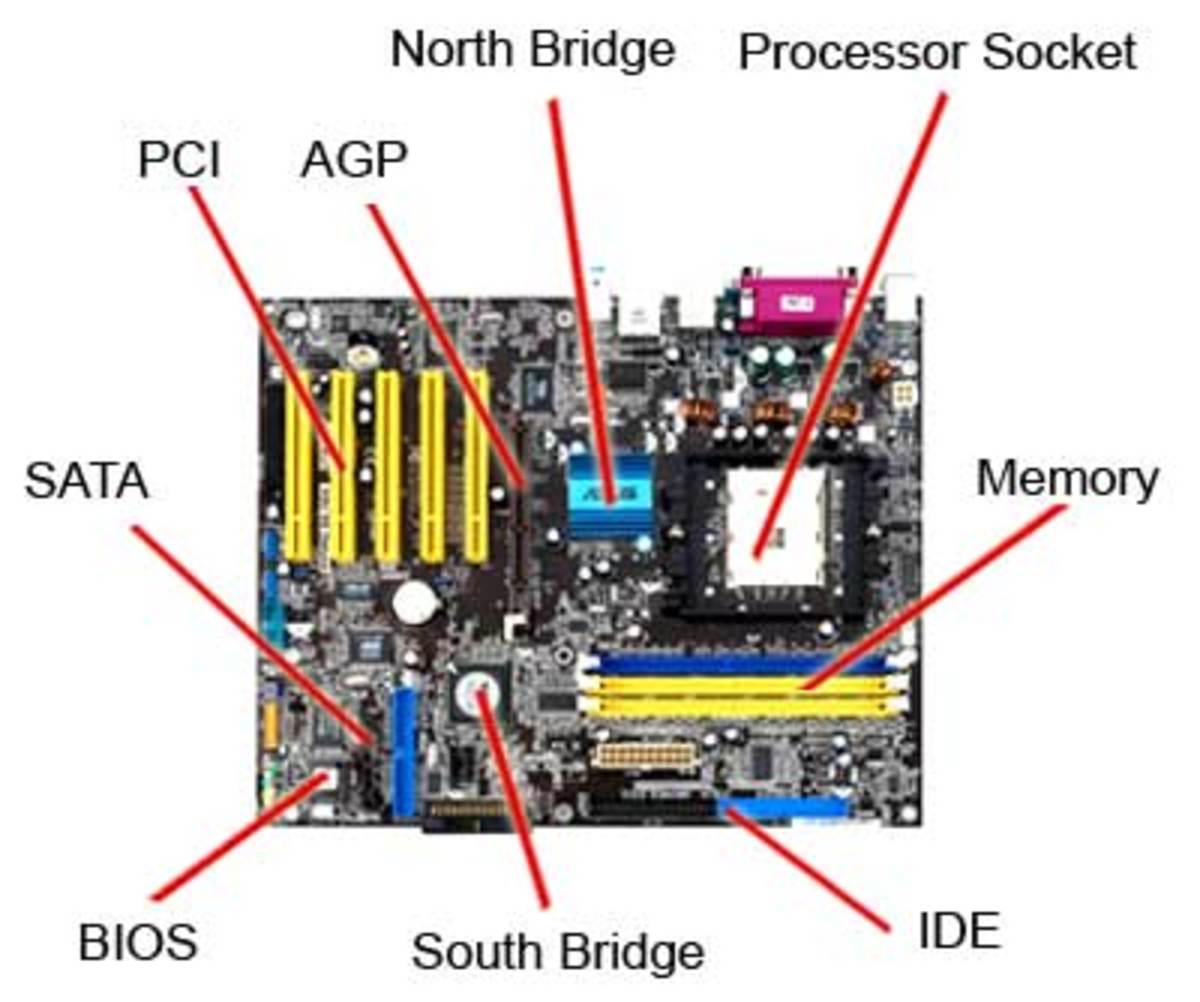
A related threat is software is made by thousands of programmers all over the world. Circuit boards are produced are also produced in many countries. Both may (highly likely) to have designed "back doors" that will not be noticed until the correct code, or instructions are given to unleash a planned action.
Our government is aware of this possible breech of "security." Computer programs are being utilized whereby "command and control" portions of the computers are limited to key sections only. Computers are being designed to operate on the "need to know basis" just like people are with Top Secret Security Clearances.
If a computer suddenly receives instructions to execute a series of actions that is not within given parameters, it will not perform the requested instructions and will notify the default alarms to others, or shut down on a case-by-case basis.
Next "Virus" attack unknown. The danger is foreign governments and terrorist can disable our infrastructure and shut down our country before any "hostile" action is taken.... We are vulnerable to many "distractions" while somebody "stabs" us in the back...
Related Information, Update:
http://hubpages.com/hub/Computer-Worm-Stuxnet-Hits-Nuclear-Plant-in-Iran