Computer Worm Stuxnet Hits Nuclear Plant in Iran
Aimed at a Specific Facility in Iran?
Cyber Attacks: Multiple Government Involvement
More than 100 countries are currently trying to break into U.S. networks. We are not "ready." The Pentagon's Cyber Command is planned to be operational in October, 2010. The rest of the U.S. government is mired in bureaucratic defining varied responsibilities of different agencies, cyber security is "not prepared," nor coordinated... While "Rome burns," and the generals play politics to align with Obama, who claims, "We are staffing up" while we are probed thousands of times each day.
The U.S. and the Israelis are the best in the world at hacking other country's computer systems. However, the U.S. does not have the best defenses. The Internet is abuzz about the virus Stuxnet, a worm that attacks industrial-control systems. The Stuxnet worm is described as a "cyber-missile," designed to seek out and destroy specified targets. Its unusual sophistication hints of a well-financed nation, rather than a group of rogue hackers trying to steal industrial secrets or to cause problems.
Per the Wall Street Journal, September 25th edition, "Stuxnet alarmed officials both in the Pentagon and the U.S. industry, because it targeted the core of industrial computer-control systems." The Stuxnet is by-passing the computer "nervous system," and going right to the computer "brains." Stuxnet targets a specific Siemens (German industrial giant) software, called WinCC, which runs on Microsoft windows. Stuxnet gets around firewalls and having isolated computer networks not connected to the Internet by USB memory sticks, or key drives. When an infected memory stick is plugged into a computer, the Stuxnet software checks to see if WinCC is running. If it is, it logs on and installs a backdoor control system and contacts a server in Malaysia for instructions. If the computer cannot find a copy of WinCC, it looks for other USB devices and copies itself onto them. It then is spread across local networks via shared folders and print spoolers.
WinCC is a reasonably obscure "supervisory control and data acquisition" (SCADA) management system. This would indicate the normal run of "hackers" would want to infect as many computers as possible using the more popular control systems and not have focused on the rare SCADA management system.
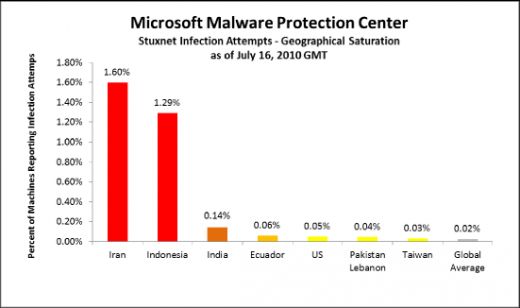
Stuxnet examines the systems it is running on and if specific characteristics are found, shuts down specific processes. This worm is honed to do very specific tasks. Stuxnet is a very expensive worm that uses the combination of two compromised security certificates that were stolen from compainies in Taiwan and uses Windows to launch automatically when a user tries to access the memory stick on which it is installed. One would think Stuxnet was designed to perform specific task for identified locations. Given Iran is the most infected, it is apparent it is the target. The Stuxnet worm requires comprehensive knowledge of a particular control systems. Given this, it appears to be softeare aimed a one specific facility.
The U.S. needs to TODAY, not tomorrow, realize our way-of-life and our world as we know it is at stake. We are a target! Again, quoting the Wall Street Journal September 25th, 2010 issue, General Keith Alexander, the chief of the new U.S. Cyber Command told a congressional panel this week: 'What concerns me the most is destructive attacks that are coming..." He went on to say, "The danger is that such attacks can do damage that is difficult to reverse and can't be fixed by blocking Internet traffic by destroying computers and other automated device connected to the Internet before the government or a company can respond."
An area in the U.S. that is very vulnerable is our infrastructure. Referring to the same article above in the Wall Street Journal where General Alexander stated, "...such attack could be mounted on the U.S electrical or banking sector, and the affected company would largely be on its own to defend itself."
Obama has not figured out a way to aid the response to an attack on the private sector. If there were an attack to day, there is no government authority that is authorized to respond to the threats...
We certainly cannot pen our hopes to the futile attempts by the U.N. working group, the U.S., China, Russia and other countries that are taking "steps" to devise ground rules for cyber crime and cyber warfare! If I get into a "fist-fight," I will fight to win, to "eliminate" my partner. I do no fight per Marquess of Queensberry rules (1867). Fighting, to me is not a sport. Warfare is not a "sport." There is only one rule: winning...
Update: http://hubpages.com/hub/Computer-Worm-Stuxnet-Hits-Nuclear-Plant-in-Iran