Is Your Computer Hacked?
Are We Hacked and Do Not Know?

What's Going On? Cyber Attacks...
The Challenge – The Executive Branch Knows something Weird is Going on…
The President noted, "cybersecurity is a challenge that we . . . are not prepared to counter." This is the tip-of-the-iceberg. A top Department of Homeland Security official has admitted to Congress that imported software and hardware components are being purposely spiked with security comprising attack tools by unknown foreign parties.
Rep. Darrell Issa (R-CA) during a White House Cyberspace Policy Review hearing stated, “Software infrastructure, hardware, [and] other things are built overseas that come to the United States with items that are embedded already in them by the time they get here to the United States.”
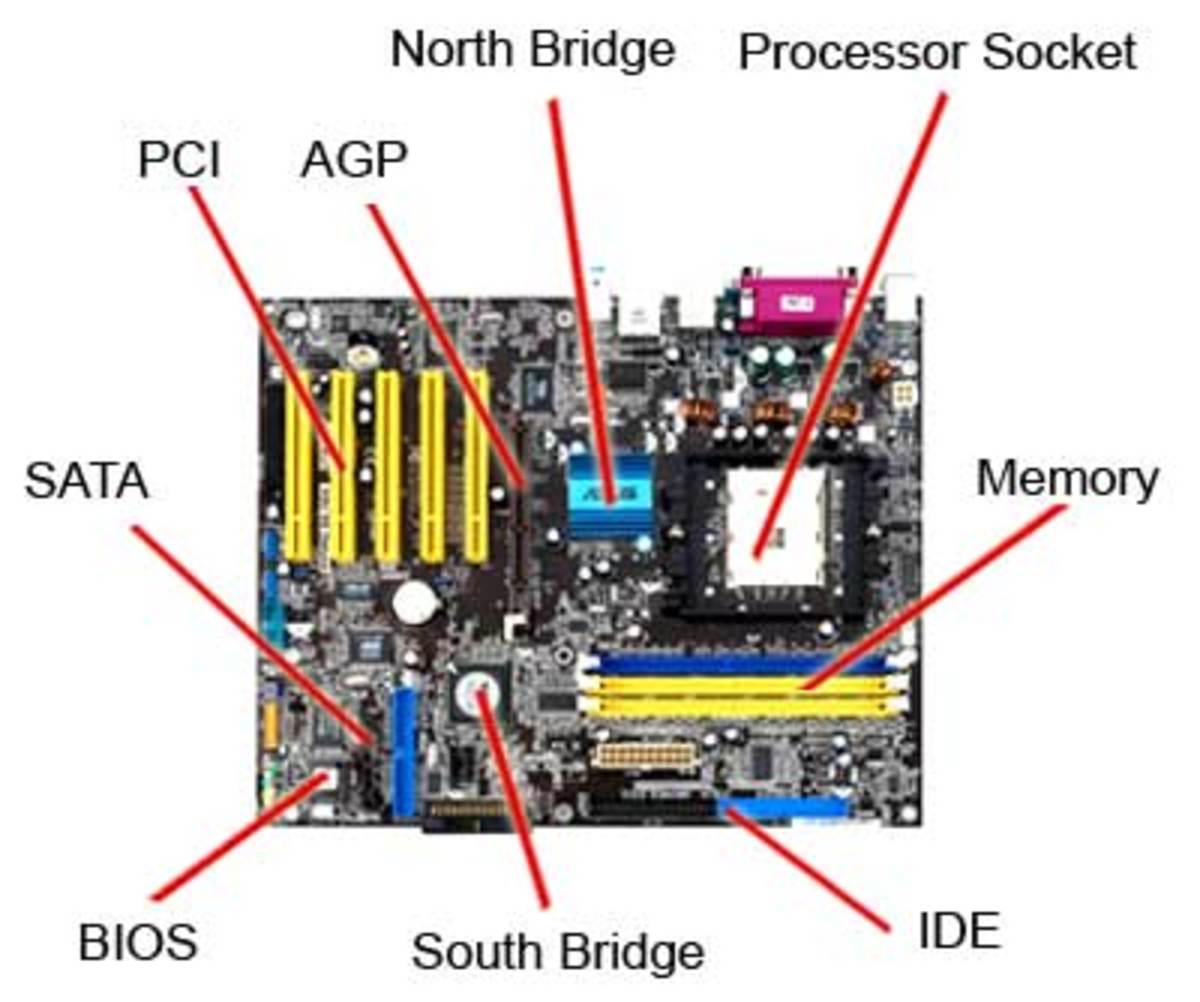
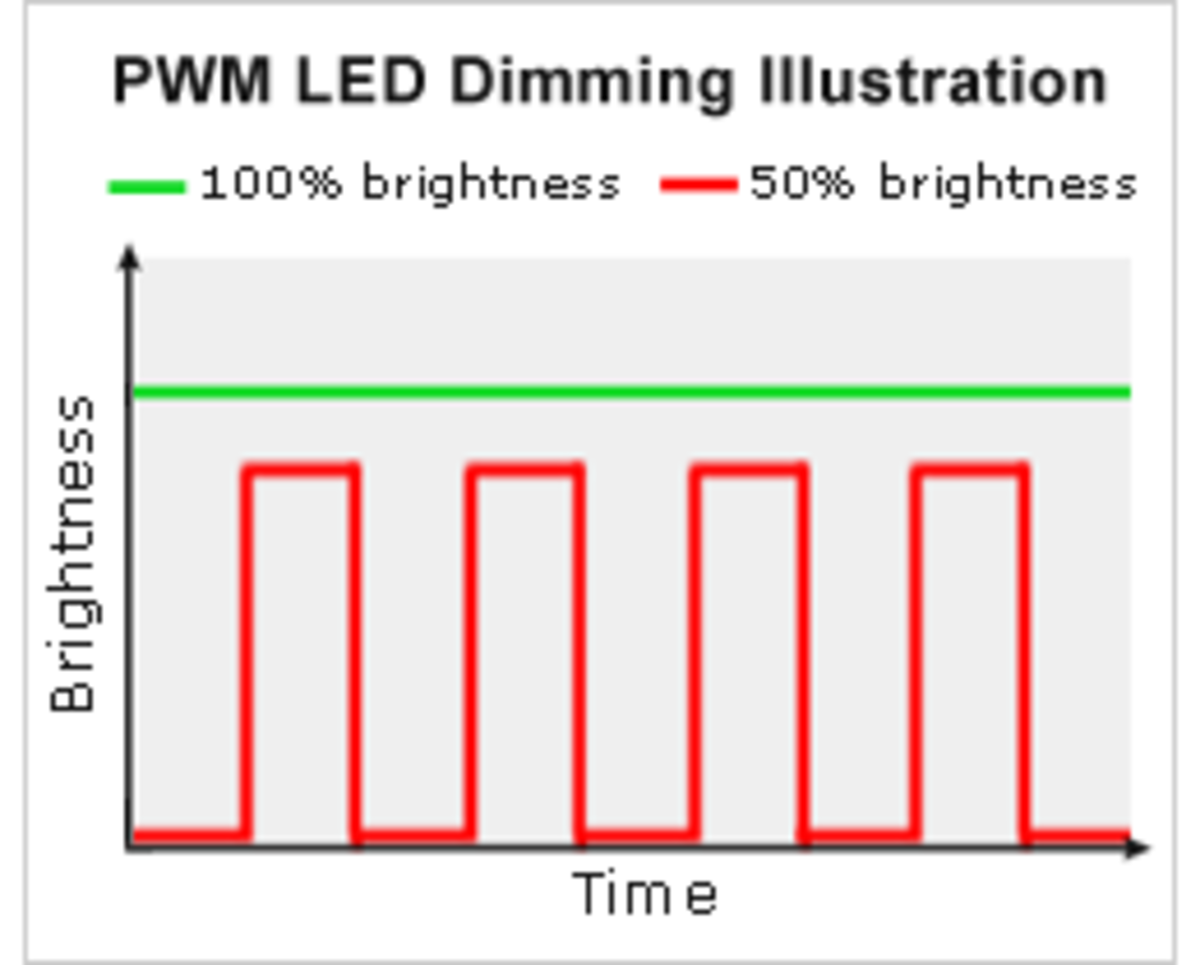
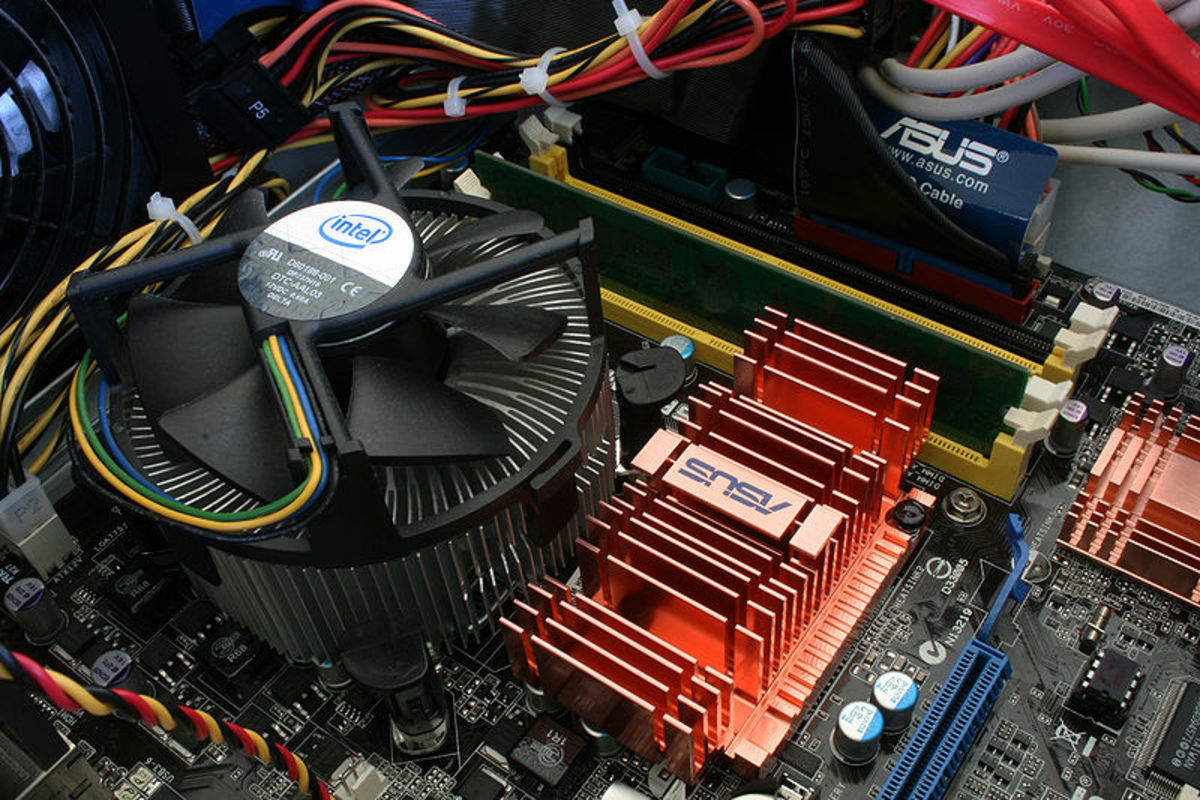
According to White House documents, the executive branch is actively studying the risk of nation-states purposely installing sleeper, one-use attack tools in software and hardware components marketed in the U.S. hardware manufactured abroad has been embedded with malicious code, a problem described last year in Scientific American by John Villasenor, a professor of electrical engineering at the University of California, Los Angeles. The design of modern integrated circuits has become so complex, says Villasenor, that malicious agents could insert unwanted instructions into the circuits at some point in the process.
Malicious Firmware
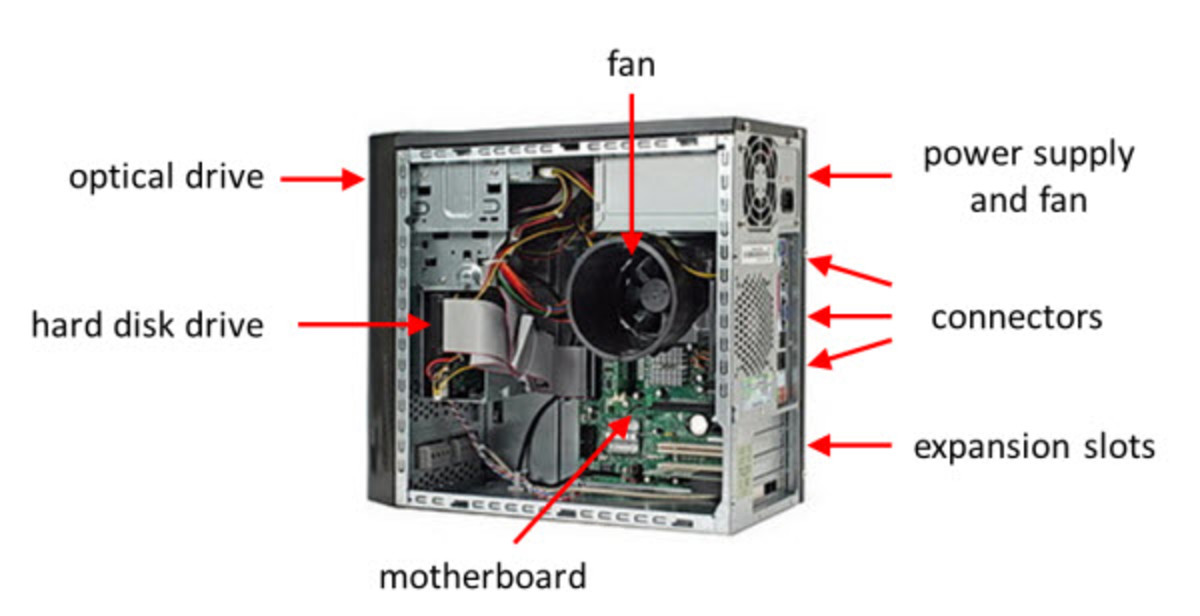
The existing danger from the supply chain that comes from global sources, for electronic components could be infiltrated by hostile agents. These hostile agents – not limited to foreign governments – could alter the circuitry of the integrated components. Logic “bombs” can be created that would cause terrible harm and economic disruptions on a global scale. The damage and disruption is only limited by the needs and skills of the hostile agents.
What Does This Mean?
Examples of the danger already embedded in our electronic devices, cell phones, hardware and computers is where our cell phones may be preprogrammed to shut down at a certain predetermined time. It gets worse. Anything that uses a microprocessor – anything electronic – is a target. Integrated circuits are the brains of our digital world. They lie at the heart of our communication systems and the world’s utility systems. They fly our planes, operate our cars, and operate our banking systems and vaults. Our society is fully integrated into the digital age. Our armed forces use digital devices in almost every critical system.
A well designed planned attack could bring commerce to a halt and immobilize critical parts of our military system and government.
What to do?
To prevent malicious firmware getting into our digital world is almost impossible. The supply chain from the manufacturer process, distribution, and use must be controlled. At any point, a counterfeit component could be substituted, or existing electronic components altered.
A “real-world” possible control would be to require counter-measures that include the design, fabrication, assembly, and distribution of the electronic components destined for government or critical use systems to be carried our domestically in an controlled environment. The entire process must be supervised by screened personnel with verification procedures.
There must be an on-going process of probing, searching for malicious devices by varied means and devices.
Related Article:
http://hubpages.com/hub/Computer-Worm-Stuxnet-Hits-Nuclear-Plant-in-Iran
New Book Available - Buy Direct from Author and Save $$$
www eyeswideshutanenigma dot com or simple enter name of book into Goggle Search Engine: "Eyes Wide Shut: An Enigma"