Programs Which Are Dangerous To Your Computer Security Due To Multiple Vulnerabilities
Kaspersky Labs, creator company of one of the most succcessful and powerful security suites available (Kaspersky Antivirus), recently announced their findings on a 2012 survey they had conducted.
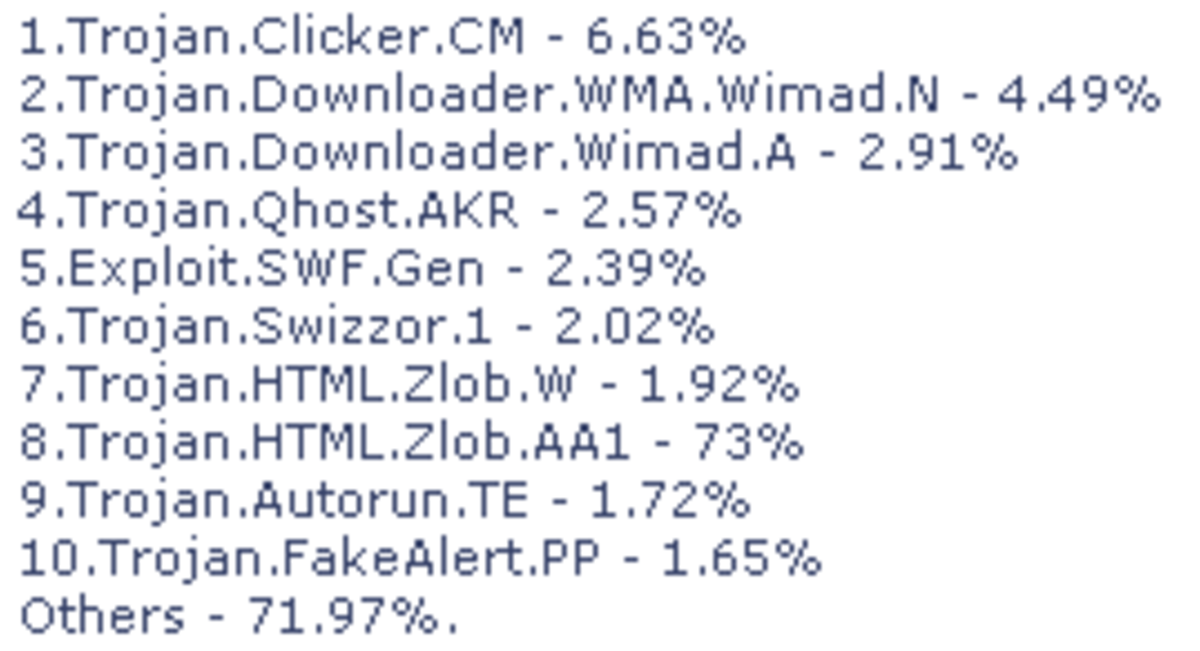
Based on focused examination on security and privacy loop holes in a wide range of computer software in 2012, and using data gathered by their cloud-based Kaspersky Security Network, Kaspersky specialists have identified more than 132 million vulnerabilities in more than 11 million computer systems worldwide.
This number, with a simple division, indicates that there are approximately 12 vulnerabilities per computer user... a whooping number which shows that regardless of how computer and software have progressed throughout the years, still there is much to be done in terms of user privacy.
Moroever, what is quite astonishing is the fact that only in 2012, more than 800 software vulnerabilities have surfaced.
The Worrying Findings
Cyber cirminals typically target specific software which exists in all systems regardless of operating system - Adobe Reader, Adobe Flash Player and Java are 3 of them. Surprisingly, in 2012, only 8 vulnerabilities were identified in these three applications and that is definitely a step forward. Java was found to contain 5 loop holes, Flash player had two, and only one vulnerability for Acrobat Reader, which is widely used.
These tools however still are a powerful way in the hands of hackers who aim to bypass user security software and attempt to gain access to private data computers, sensitive information such as credit card numbers and sometimes even sabotage industrial systems or government websites.
Aside indicating the multiple vulnerabilities of widely used software, Kaspersky Labs also state that users tend to delay or even avoid updating their software to the latest version, even if it is free of charge and even if they are notified that the latest version fixes security loop holes of the previous ones. The particular analysis shows some worrying results; older versions of software remain installed and are commonly still used - the danger of data loss and privacy risks are of higher level.
In particular, the survey showed that 6 weeks after the notification of a new version of Java becoming available ( September-October 2012), only the 28.2% of users managed to update their systems to it. More than 70% of the computer systems were left vulnerable to cyber criminals who had already found out how to manipulate the loop holes of the older versions. More examples of the same problem - an obsolete, full of loop holes version of Flash Player from 2010 ( three years old!) was still active in 10.2% of systems and didn't seem to decrease - that means the users would not remove and update. Similarly, a serious security vulnerability found in Adobe Reader in 2011 was still present in the 13.5% of systems examined.
The numbers might be boring, but the truth is that software vulnerabilities are a huge concern for privacy, be it single-user or large companies. It isn't hard to decrease the dangers from the afore mentioned issues; the updates are free, notification on their availability is on time and the loop holes are fixed quite fast.
Additionally, there is no reason anymore that computer systems remain unprotected; most computers worldwide have internet access, many worthy antivirus and other security software are provided for free and in general, all we need to do is be cautious with what we do on the web, regularly update our software and antivirus and have some common sense.
How Often Do You Update Your Software?
Other Hubs About Computer Security
- How To Fix Certain Problems Viruses Cause In Your System
Sometimes an antivirus cannot keep a computer system safe always. For those bad times when a security threat has infiltrated, you can use the freeware software Quick Disaster Recovery. You can repair particular issues that come along with tough worms - How To Keep Your Computer Safe Against Spyware And Other Viruses And Threats
An antivirus software is necessary; is it enough, however? Learn how you could keep your computer safe using anti-spyware programs. - How To Use Android Lost To Locate Your Lost Or Stolen Smartphone
With a free application from Google Play, you can locate your smartphone, no matter if it is just lost or stolen. - Best Choices Of Free Antivirus
You don't really have to pay for a good antivirus. - Laptop, Tablet Or Smartphone Theft: What To Do To Prevent It And How To Try To Recover It
The dreadful moment when you notice that someone has stolen your smartphone/laptop/tablet... what your first steps should be, how you need to deal with the incident and what to do to prevent it.

![How to Remove Kaspersky Password Protection? [Easily Recover] How to Remove Kaspersky Password Protection? [Easily Recover]](https://images.saymedia-content.com/.image/t_share/MTc2Mjk3NDcwOTAzNTkyMTI2/how-to-remove-kaspersky-password-protected-easily-recover.png)