How to Make and Detect a Keylogger on Your Computer

Welcome to Keylogger 101. Perhaps you found this article because you have had a Yahoo, Gmail, Hotmail or Bank Account Hack or perhaps you are just highly suspicious that there is someone logging into your accounts or spying on you. In this article we will fully discuss Keyloggers, how they work, what they do and what you should do if you believe you have one.
WHAT IS A KEYLOGGER?
A Keylogger can be a malware / virus that is installed on your computer due to user error, such as clicking a "bad link" or downloading a corrupt file. A keylogger can also come in other forms.
For example, a jealous / suspicious spouse or roommate can purchase keylogger software and download it onto your computer. Once the program is download, it will run undetected and the individual can monitor it from a remote location (meaning they do not need to access your computer again to retrieve it).
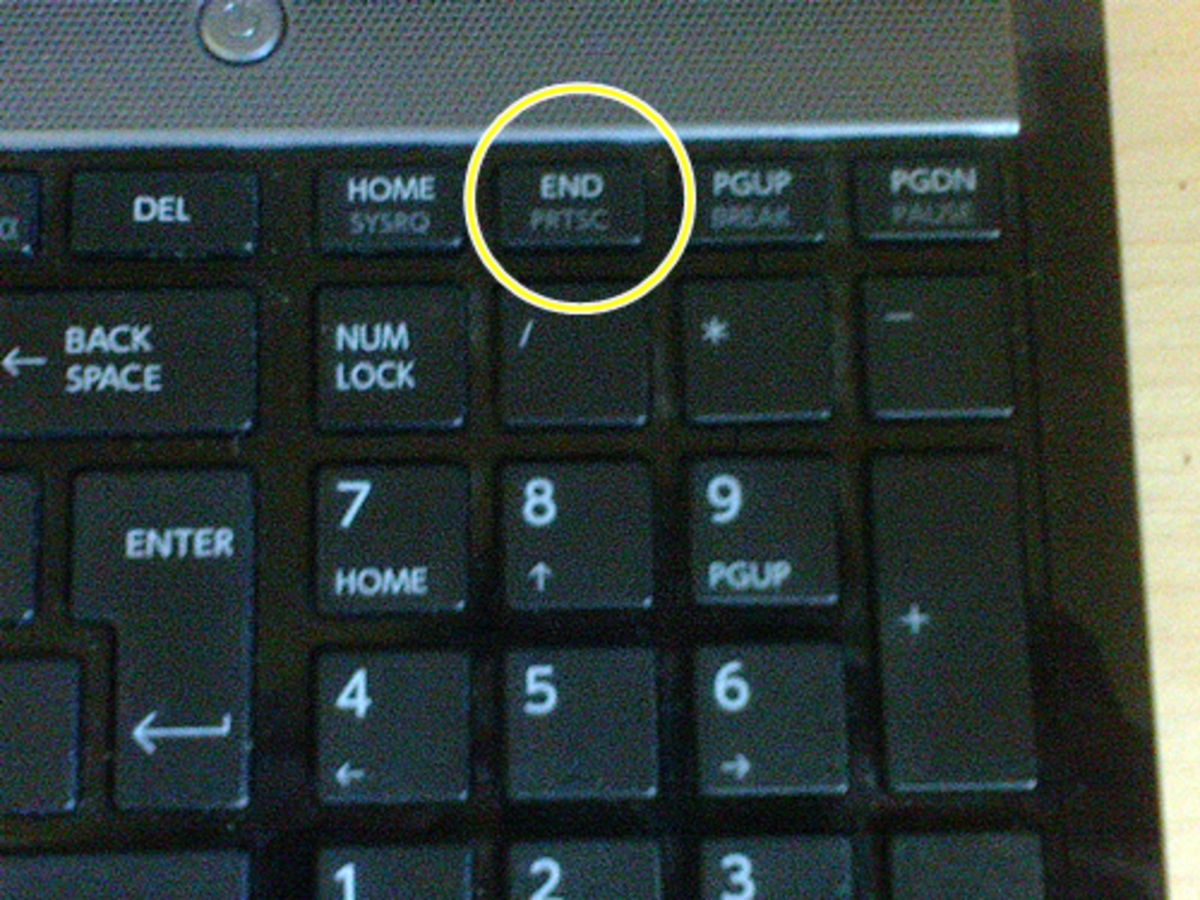
A keylogger can also come in the form of a computer plug-in device that can be purchased off Amazon.com or other websites:
HOW A KEYLOGGER WORKS
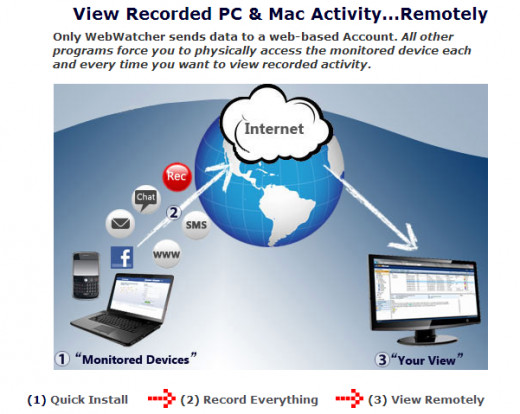
A keylogger works by recording data. Keyloggers come in a variety of basic - to - advanced. Some keyloggers capture every keystroke the pc user enters. It then sends this information to the installers remote location. Other keyloggers are much more advanced and capture screenshots, record calls and more. These advanced keyloggers then send the information as an email to the culprit so it remains as evidence that is forever stored by the culprit.
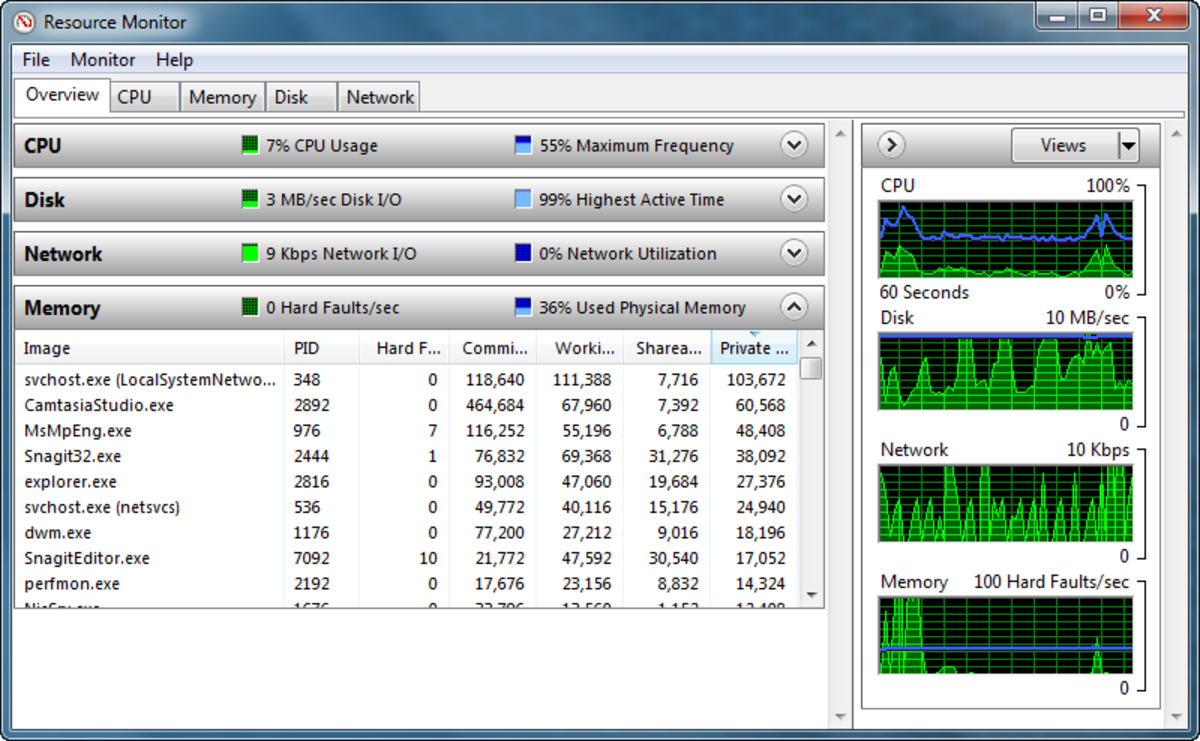
Check out the image below for a clear explanation on how keyloggers work:
HOW TO DETECT A KEYLOGGER
Since keyloggers come in different forms, there is no single solution for detecting a keylogger. You may have to use more than one of the following:
1. If someone who has had physical access to your computer is believed to be the one who installed the keylogger, it is likely that he/she may have inserted components into the pc. In this case, inspecting the keyboard's connection to the computer, or replacing the keyboard will solve the problem.
2. Antikeyloggers can scan your hard drive for the digital signatures of known keyloggers, and look for low-level software "hooks" that indicate the presence of a keystroke grabber. A free program like KL-Detector will find a keylogger on your computer, however it will not delete it. KL Detector works with Windows NT 3.51 SP3, Windows 2000, and Windows XP.
3. Use an AnitVirus program. However, keep in mind that Antikeyloggers and keylogger detectors are more effective against keyloggers than general antivirus programs because the Anti-Virus programs often don't identify keyloggers as malware.
4. Take your computer into the local repair shop. The repair shop should be able to find any keylogger on your computer. You can have your computer "wiped". Wiping your computer will not result in data loss as long as your information is "backed up". The computer shop should be able to do all of this for you for under $100.
HOW TO FIND A KEYLOGGER VIDEO: ADVANCED
If you are computer savvy, then I suggest watching this video that shows you how to locate a keylogger in under 2 minutes:
HOW TO STOP FUTURE KEYLOGGERS
There's a few methods you can use to prevent future keyloggers from accessing your keystrokes and obtaining passwords, credit card information or other info:
1. Using a program like Roboform will automatically fill in your email and passwords, thus eliminating you from having to type them and the keylogger gaining access. Of course this will not help right now.
2. Use a Voice to Type Program
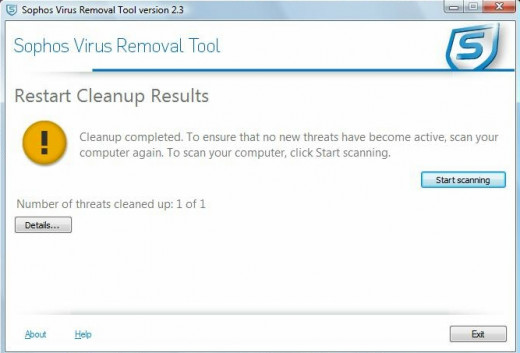
4. Download Sophos Virus Removal Tool:
HOW TO MAKE A KEYLOGGER
Making a keylogger is not for beginners. You will need to be familiar with scripting. This is why most people who are looking to "snoop" will either download a program and pay the one-time-fee or they will purchase the product shown at the beginning of this article (available on Amazon.com).
However, if you are familiar with scripting, then a keylogger can be created with C++ and stored as a Log.txt file. Below you will find a video on an alternate way to make a keylogger:
HOW TO MAKE A KEYLOGGER VIDEO
CHECK OUT MY OTHER ARTICLES:
- What to Do if Your Google Gmail Has Been Hacked
Has your Gmail account been hacked? How to tell if you have indeed been hacked and how to solve the problem as quickly as possible - How to Fix Your Hacked Hotmail Email Account: Who Br...
Do you believe your hotmail emai laccount has been hacked / broken into? Learn how to tell if your account has been compromised and what to do to fix it. - What to Do if Yahoo Email Has Been Hacked
How to tell if your email has been - How to File a Legal Case Against a Stalker / Harasse...
Everything you need to know about Stalking, Harassment, PPO's, Restraining Orders, Criminal and Civil Cases. A must-read before going to police or contacting a lawyer. - The Difference Between a PPO and a Restraining Order
If you are involved in harassment, stalking, cyber-stalking, cyber-bullying or need protection from someone, learn the difference between a Personal Protection Order and a Restraining Order - How to Stop Harassing Phone Calls from Google Voice ...
Google Voice is a service that allows users to make phone calls from a number other than their cell phone or landline. But what happens when the service is abused? Stop Harassment from Google Voice! - Getting Harassing Text Messages? How to Report Them ...
Harassing text messages come in many forms; from an angry / emotional individual to non-stop harassment from a business in the form of Text Spam. Learn how to solve your SMS Harassment - Am I Being Stalked: Signs of Stalking Harassment
Do you feel like someone is Stalking you online or in-person? Learn signs of Stalking and Harassment. Stalking is NOT legal and you do not have to tolerate it! How to protect yourself from Stalkers. - How to Report Internet Spam, Unwanted Calls, YouTube...
In my last article, I uncovered a new Domain Renewal Scam/ Spam. in today's article I will teach you exactly how to report Internet Spam, Scams and Harassment from them. - How to Stop and Report Facebook Harassment Stalking
Cyber Bullying is everywhere; from Google Voice to Twitter to Facebook - learn how to identify Facebook harassment and report it. Harassment is not legal and you do not have to take it! - HubPages.com HTML for Beginners Guide Tutorial For M...
Even if you have NEVER used HTML before, this guide will make you a professional-beginner! - Online Dating: How to Research and Investigate Before...
After you meet Mr. or Ms. Perfect on Match.com, PlentyofFish.com or other online dating sites, before you meet, do your research! Simple investigating using the internet can be a real eye-opener! - Why Gmail is Perfect for Staying in Touch with your ...
Once you read story this you will begin to understand how Gmail can make your life so much simpler. By just using it to contact customers and tips on how to get customers info the right way. - How to Stop and Report Facebook Harassment Stalking
Cyber Bullying is everywhere; from Google Voice to Twitter to Facebook - learn how to identify Facebook harassment and report it. Harassment is not legal and you do not have to take it! - CHASE Bank Account Hacked: Banking Fraud
It happens when you least expect it - a sudden withdrawal or charge that you have no knowledge of. It can quickly become the scariest moment of your life - OR it could all be a scam. READ THIS FIRST! - How to Make the Most Money HubPages.com Complete Gui...
The stuff nobody else will tell you! How to create Content that Makes Money: Secrets, Tips and Tricks. This Guide will give you all the info you need to be a SUCCESSFUL online author! - How to Make a Taco Bell Cool Ranch Doritos Taco Copy...
Are you in love with the new Cool Ranch Doritos Taco from Taco Bell? Learn how you can make this awesome Copycat recipe at home! - What to Do if Yahoo Email Has Been Hacked
How to tell if your email has been - Paid To Write: Squidoo VS HubPages
The ultimate battle of the popular PAID TO WRITE sites - which makes more money? Which is easier to use? Is it worth your time? A complete Battle-to-Death! - Received Domain Renewal Email to Fax 212-913-9858 SC...
Have you gotten a suspicious letter / email stating you must renew your domain name immediately via fax with your credit card information? Before you worry, read this article!